INSIGHT Dashboard
GuardWare INSIGHT includes the following predefined dashboards:
These dashboards provide a clear and interactive view of your organisation’s overall data landscape, highlighting user activity, file movements, and potential risks in one place.
Each dashboard includes widgets that provide real-time visibility into data usage patterns through charts, graphs, and tables, helping administrators track trends, detect unusual behaviour, and keep sensitive information secure. You can export a dashboard widget’s data to PDF or Excel by clicking the respective icons in the top-right corner of the widget.
You can also create custom dashboards and choose the widgets according to your requirements. For details on creating custom dashboards, see Create Custom Dashboards.
Risk Levels
Each activity category in the dashboard is assigned a risk level that indicates the severity of detected activities:
No Risk
🟩 Green
No unusual or unauthorised activity detected. These include routine activities within corporate policy.
Low Risk
🟦 Blue
Minor or low-impact activities that slightly deviate from standard policy but pose minimal threat, such as occasional access from non-corporate networks.
Medium Risk
🟨 Yellow
Actions that may require review, such as occasional file transfers to external sites.
High Risk
🟥 Red
Activities that indicate potential misuse or data breaches, such as unauthorised data sharing or file copying to external drives.
Risk levels are automatically determined based on the nature of the data involved and policy rules configured in the INSIGHT Management Console.
Risks Summary Dashboard
The Risks Summary Dashboard provides an overview of key security and data protection indicators across your organisation. It displays critical activities such as file sharing, data transfers, email usage, and device interactions, helping you identify potential risks and monitor sensitive information in real time.
This dashboard is particularly useful for executives and security managers who need a quick summary of data-related risks without navigating through detailed reports.
You can access the Risks Summary Dashboard from the Dashboard section in the GuardWare INSIGHT Management Console.
Each widget in this dashboard displays the following:
Activities related to various categories like SharePoint, File and data transfer, file upload, usage of AI tools, non-corporate websites and applications, and so on.
The total number of users involved in specific activities or incidents during the specific period.
The total number of incidents recorded for each monitored category. (for example, how many files were downloaded).
Risk levels for each activity category.
Widgets in Risks Summary Dashboard
Category
Widget Name
SharePoint Activities
Email Activities
Data Transfers
Device Usage
Behavioural Monitoring
1. External SharePoint Events
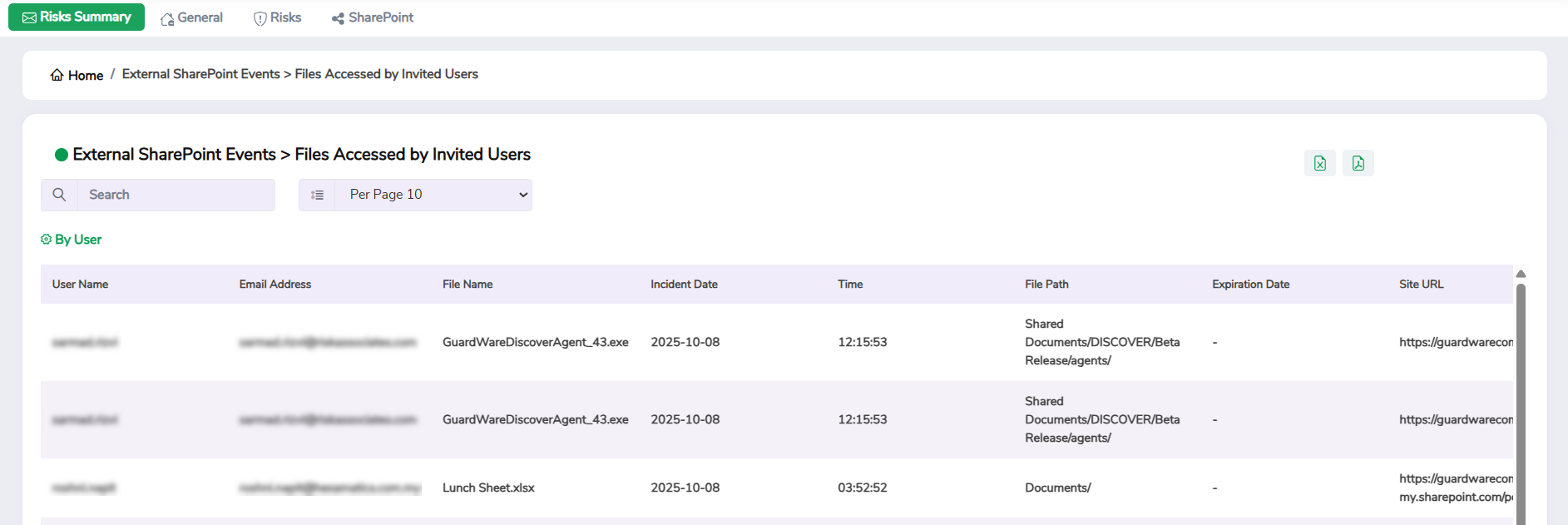
This widget helps you track how files are accessed and shared by users outside your organisation, such as partners, vendors, or contractors. It highlights activities such as access or downloads from sensitive libraries, actions by anonymous or invited users, access from mobile devices, and file interactions through links shared on Teams.
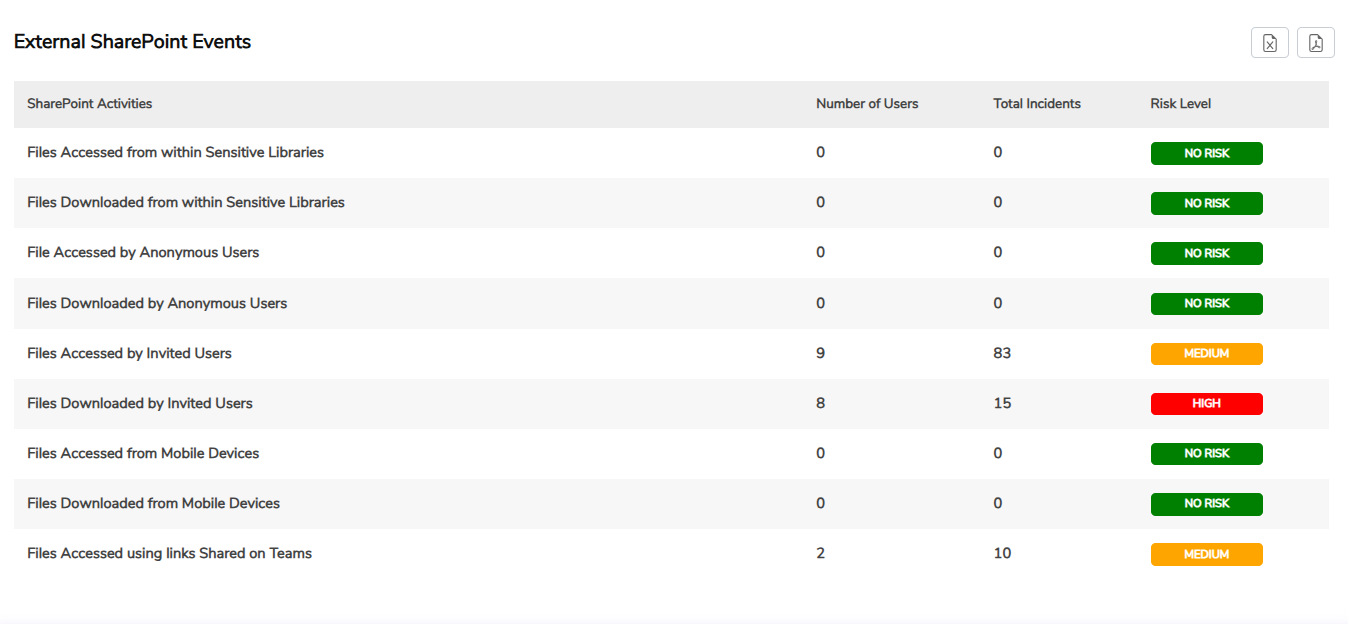
Click a specific record to view detailed information, including the username, email address, file name, incident date and time, file path, expiry date, and URL. Use the search box at the top to quickly filter specific information.
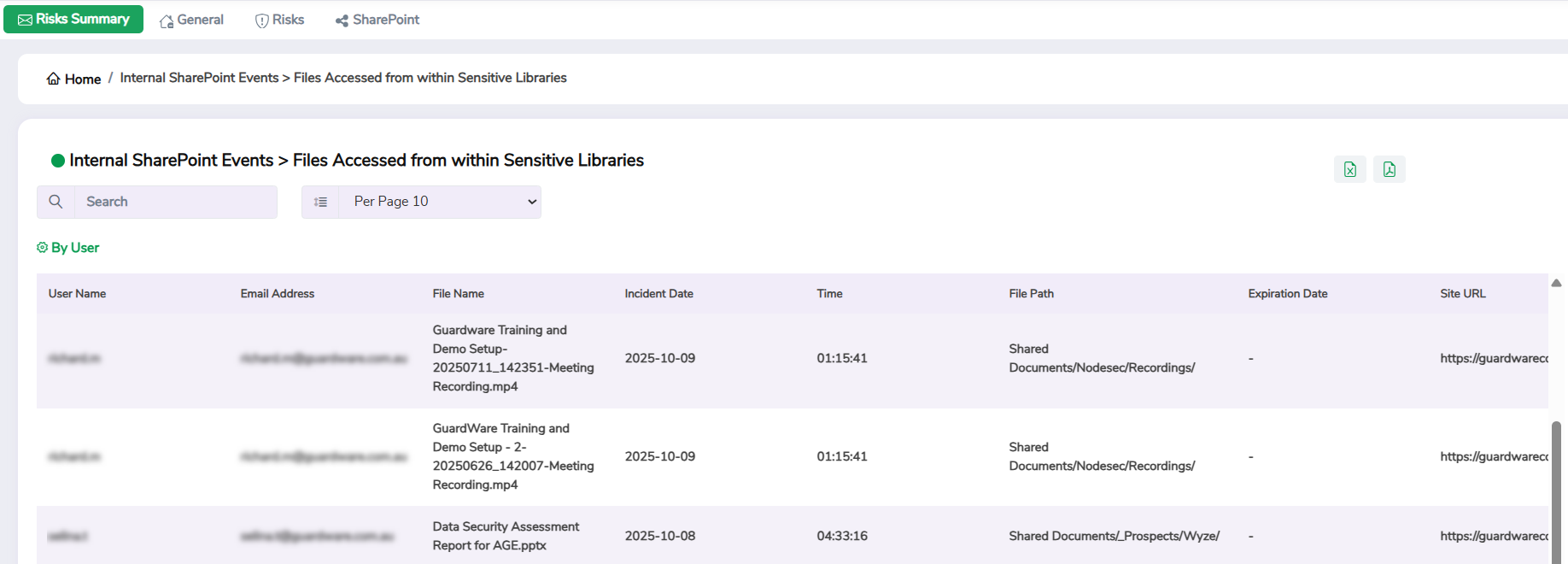
2. Internal SharePoint Events
This widget helps you track how files are accessed and shared by users within your organisation. It shows who has viewed, modified, or shared files across SharePoint, highlighting activities such as link creation for anonymous users, access to sensitive libraries, downloads from mobile devices, and file access through links shared on Teams.
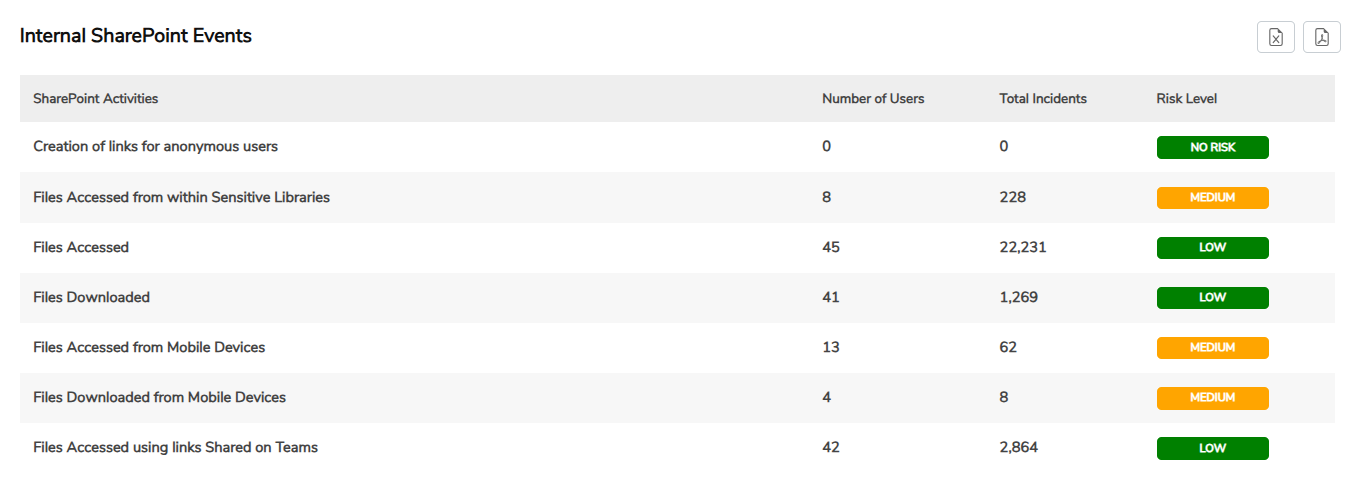
Click a specific record to view detailed information, including the username, email address, file name, incident date and time, file path, expiration date, and URL. Use the search box at the top to quickly filter specific information.
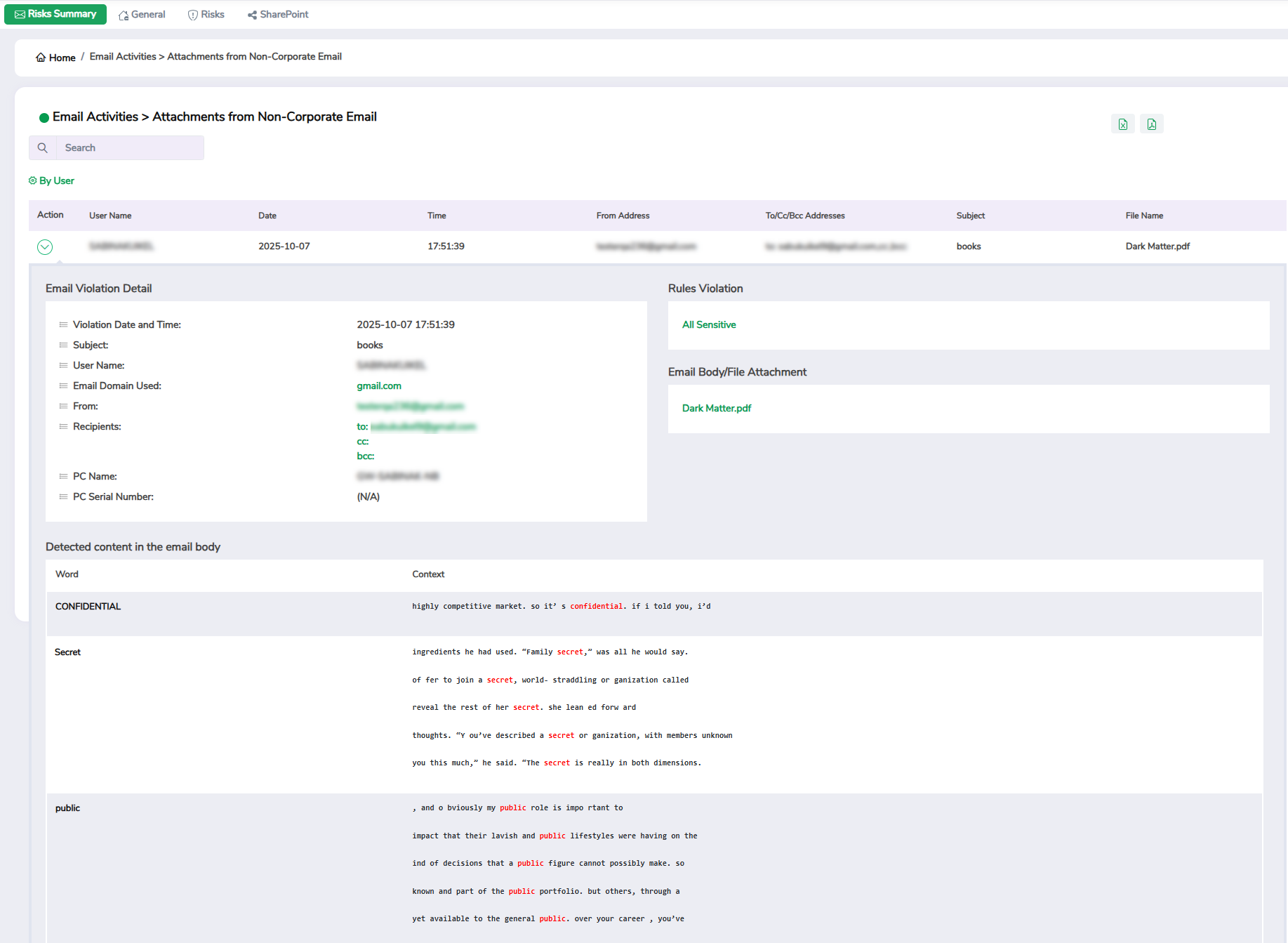
3. Email Activities
This widget provides an overview of email usage patterns across your organisation, helping you monitor how attachments and sensitive information are shared through corporate email channels. It tracks email attachments sent from corporate to non-corporate domains, as well as emails sent to insecure, personal, or internal corporate addresses, and attachments shared from non-corporate email accounts.
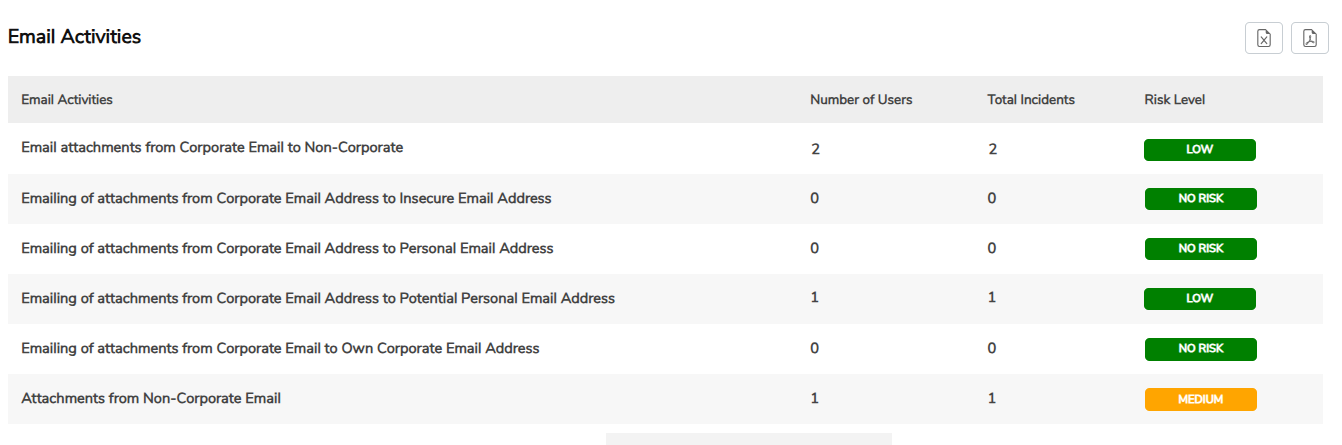
Click a specific record to view detailed information, including the username, date and time, sender and recipient addresses, subject, and file name. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
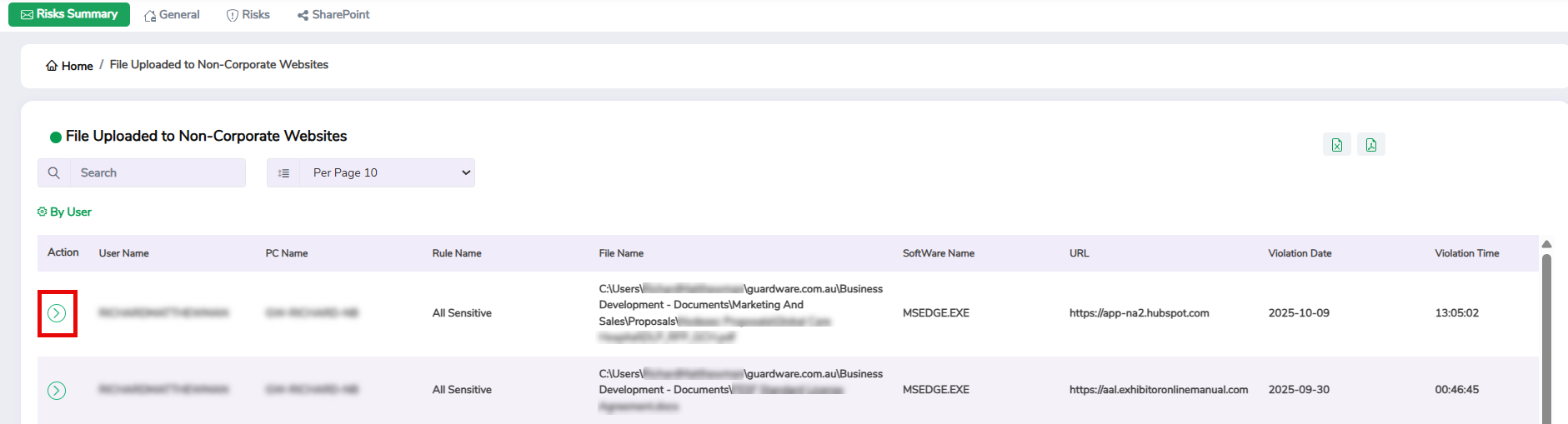
4. Data Transfer using Non-Corporate Websites
This widget helps you track file uploads or transfers made to non-corporate websites, such as public file-sharing services or personal cloud storage platforms. It helps you detect and prevent potential data leaks by identifying instances where sensitive files may have been transferred outside secure corporate networks.
Click a specific record to view detailed information, including the username, PC name, file name, software used, website URL, and the date and time of the violation. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
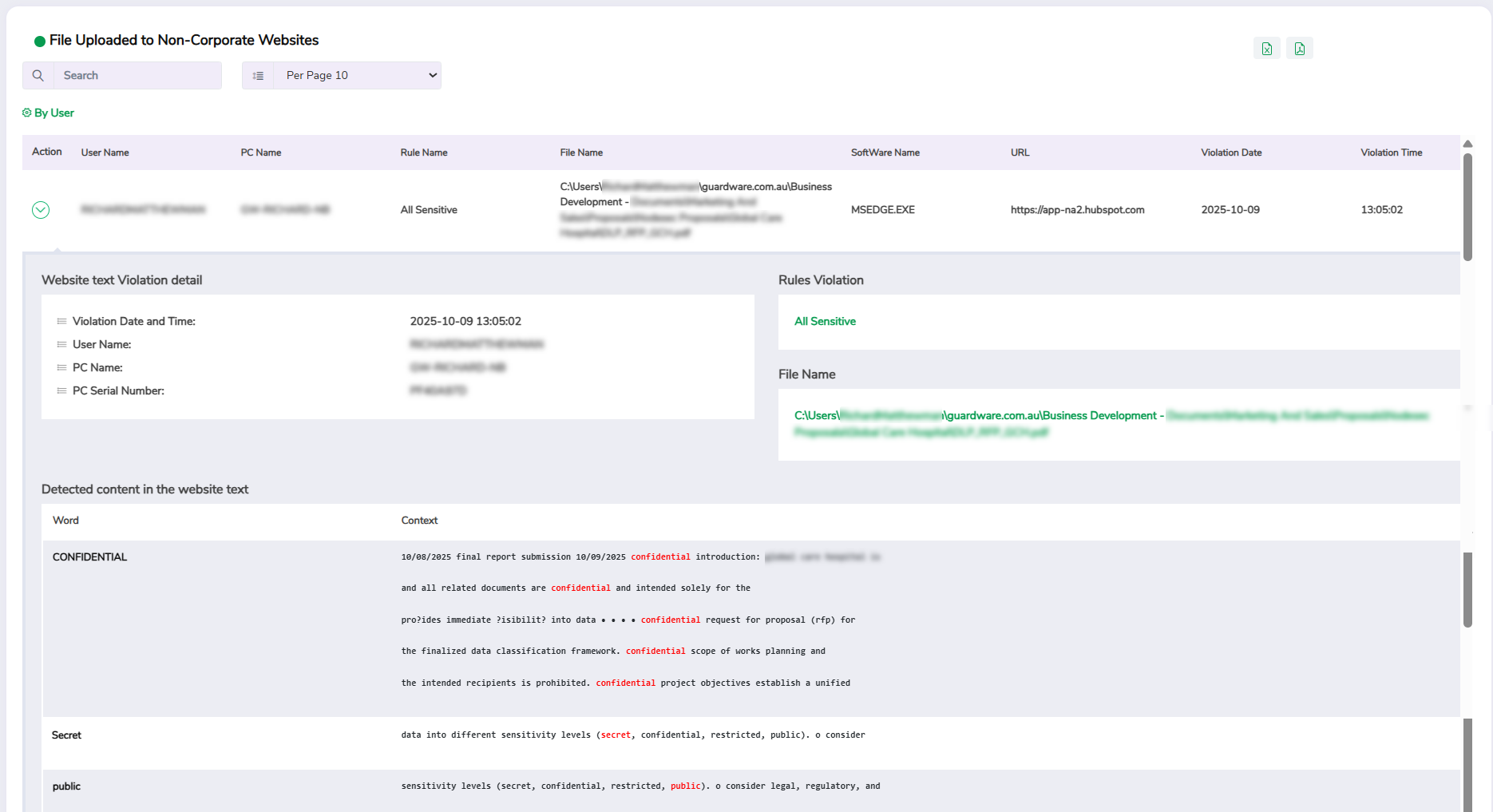
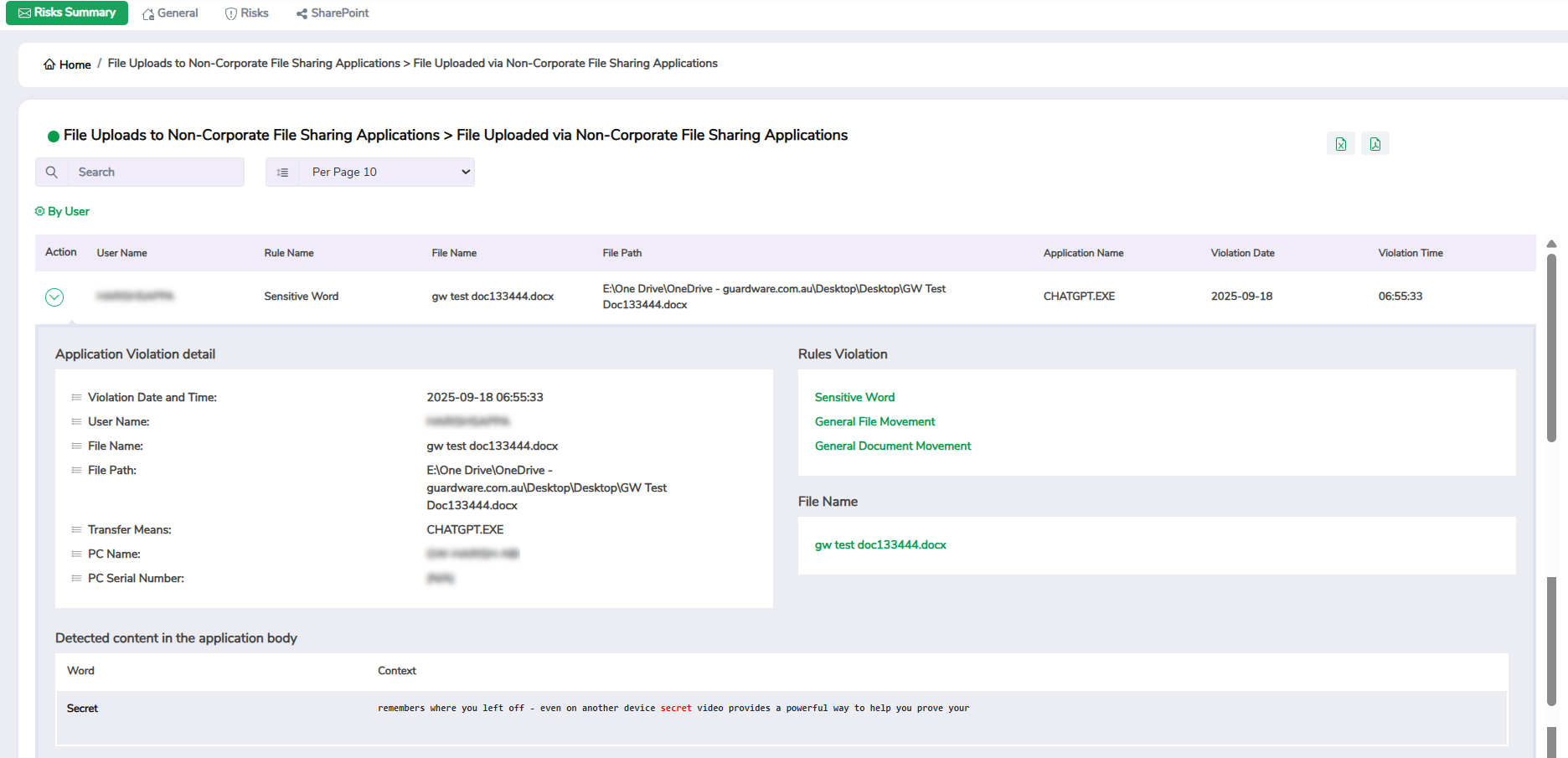
5. File Uploads to Non-Corporate File Sharing Applications
This widget helps you track files uploaded through applications like Dropbox, or Google Drive that are not managed under your organisation’s approved corporate accounts. Frequent uploads to these applications can indicate an attempt to bypass corporate storage policies or move confidential data to personal accounts.
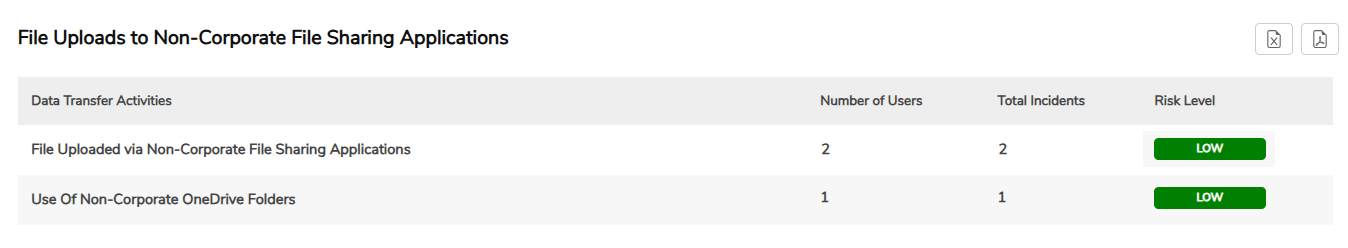
Click a specific record to view detailed information, including the username, file name, file path, application name, and violation date and time. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
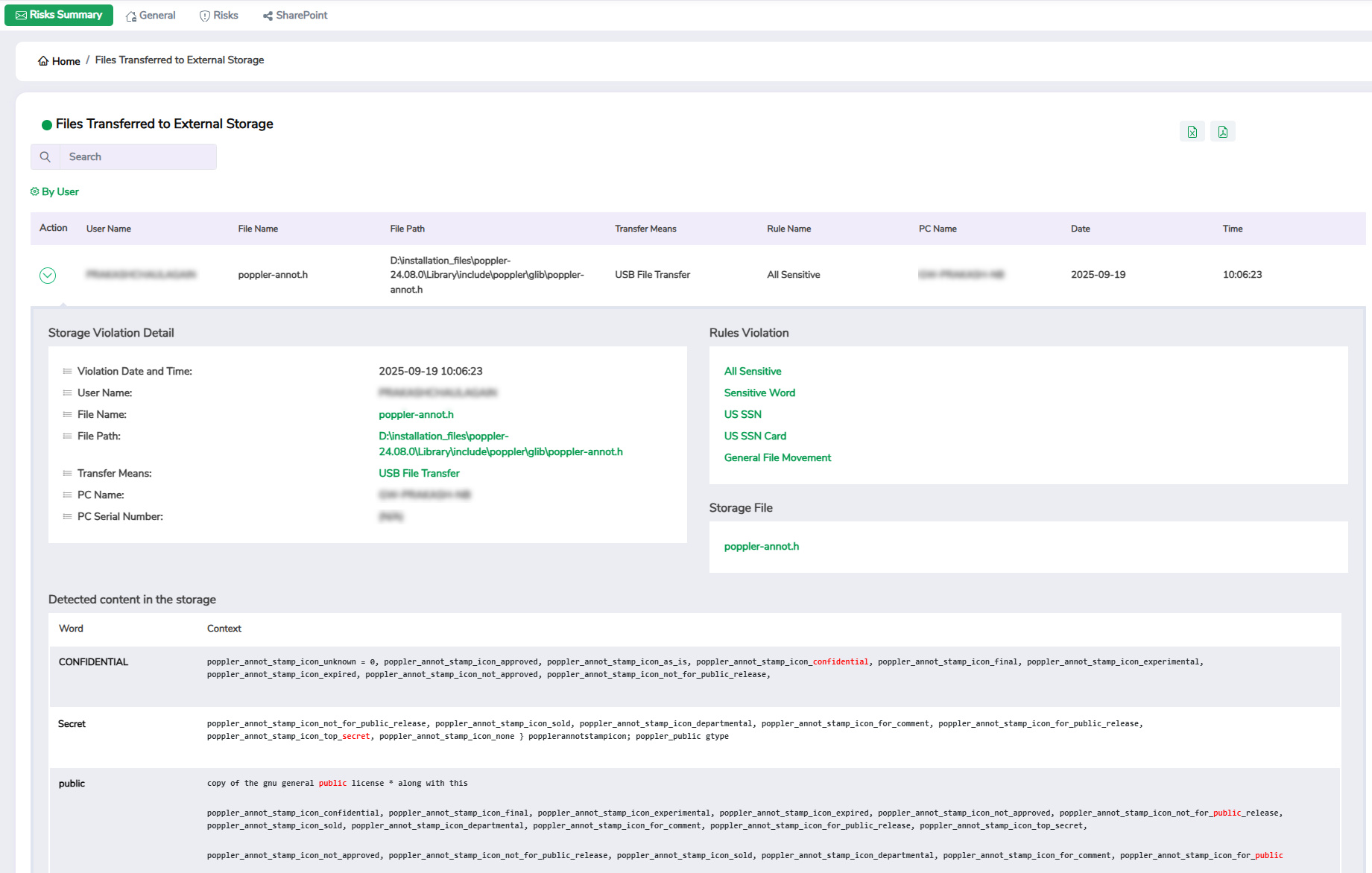
6. Storage Device Risk
This widget helps you track files copied or moved to portable storage devices such as USB drives or external hard disks, along with the users who performed these actions. Because these transfers are often offline and unmonitored, this widget helps mitigate risks of data theft or accidental exposure through removable media.
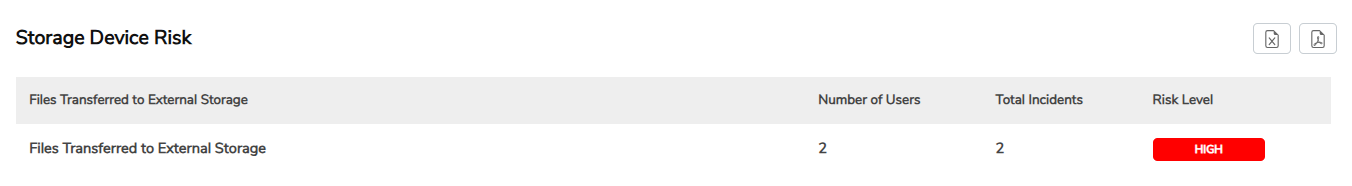
Click a specific record to view detailed information, including the username, file name, file path, transfer means, PC name, and violation date and time. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
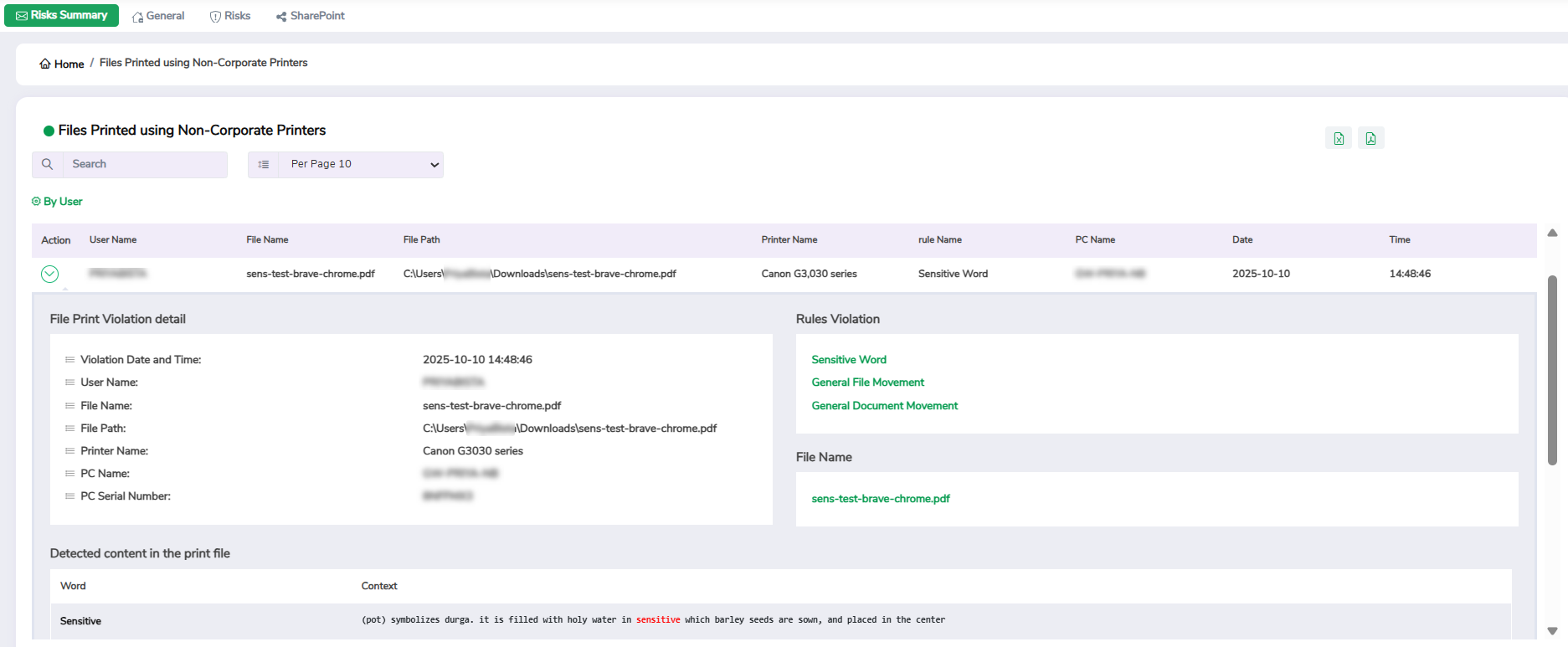
7. Printing Incidents
This widget helps you track files printed using non-corporate or unauthorised printers. It provides visibility into printing activities that may lead to hard-copy data leaks.
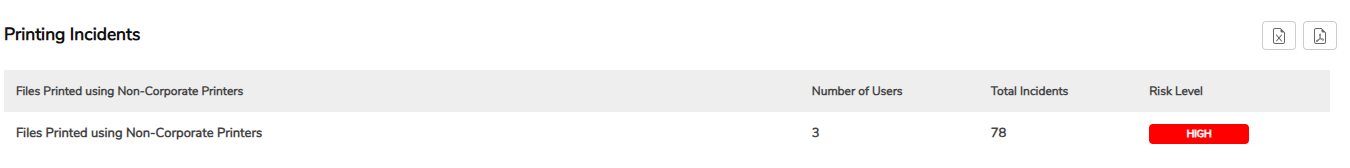
Click a specific record to view detailed information, including the username, file name, file path, printer name, PC name, and violation date and time. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
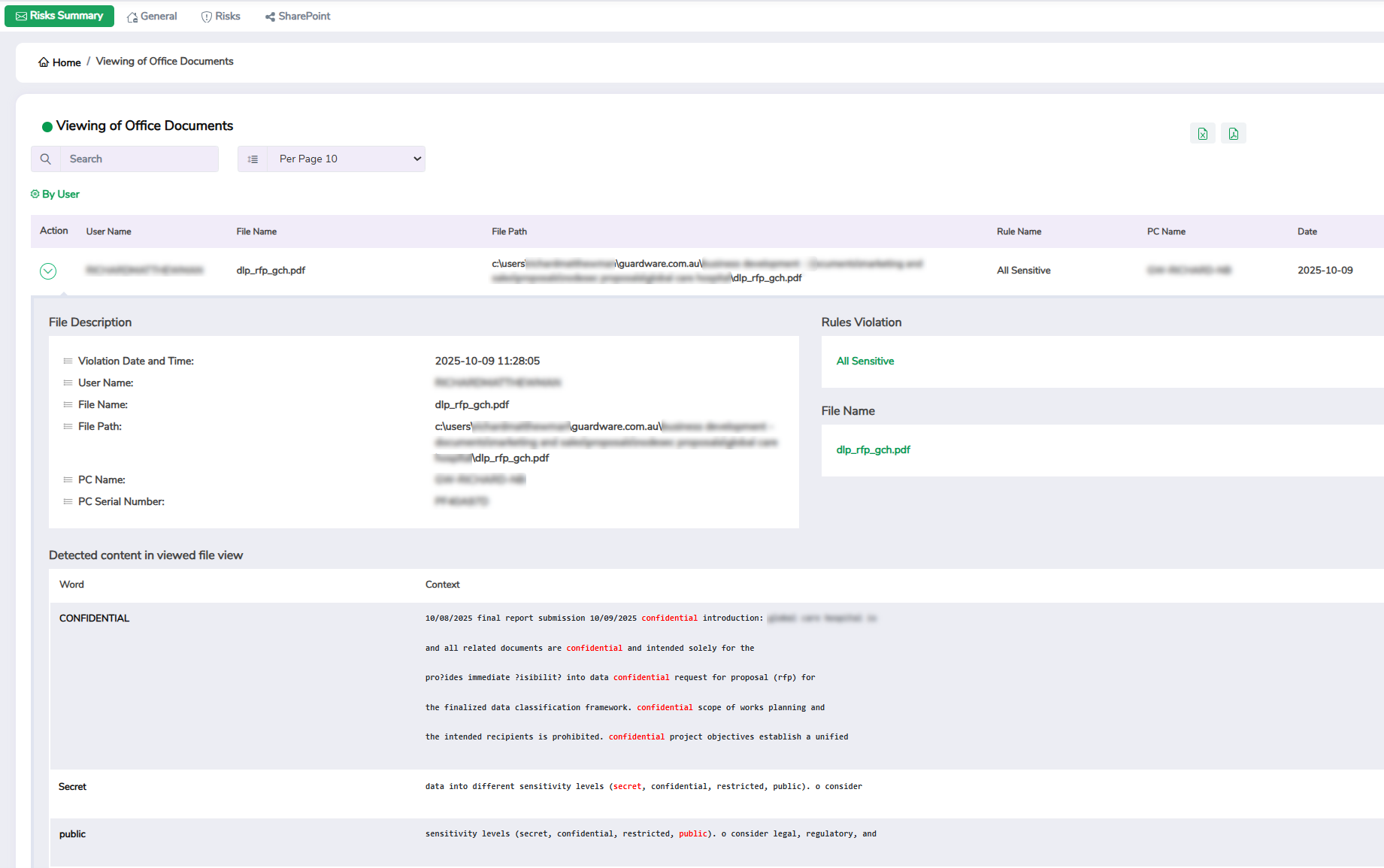
8. Access of Documents on Local Devices
This widget helps you track when Office documents, such as Word, Excel, or PowerPoint files, are opened on local devices. Tracking local document access helps ensure files are viewed only by authorised users and assists in identifying unusual access outside regular working patterns.
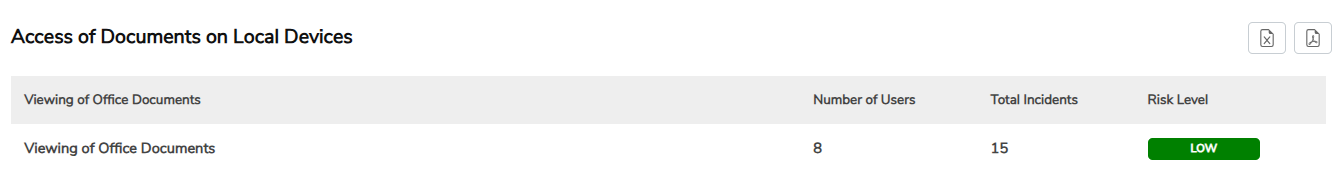
Click a specific record to view detailed information, including the username, file name, file path, PC name, and violation date and time. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
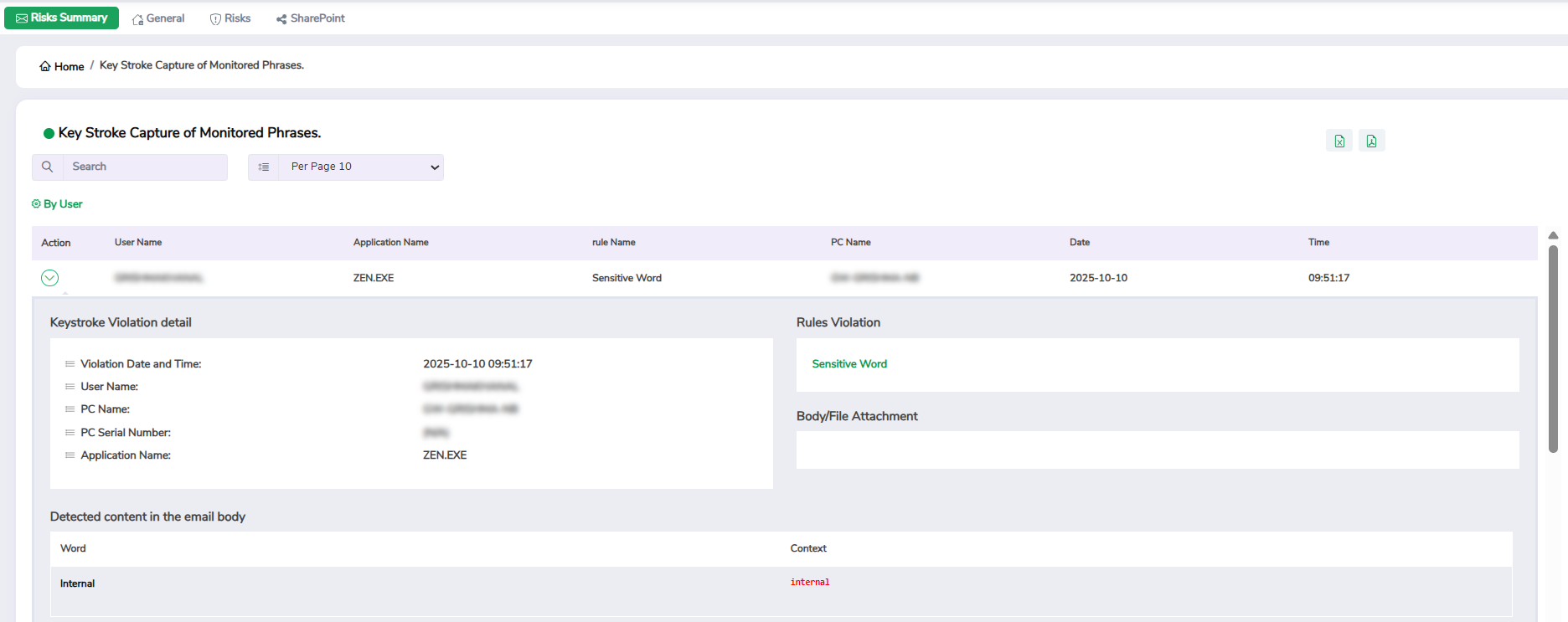
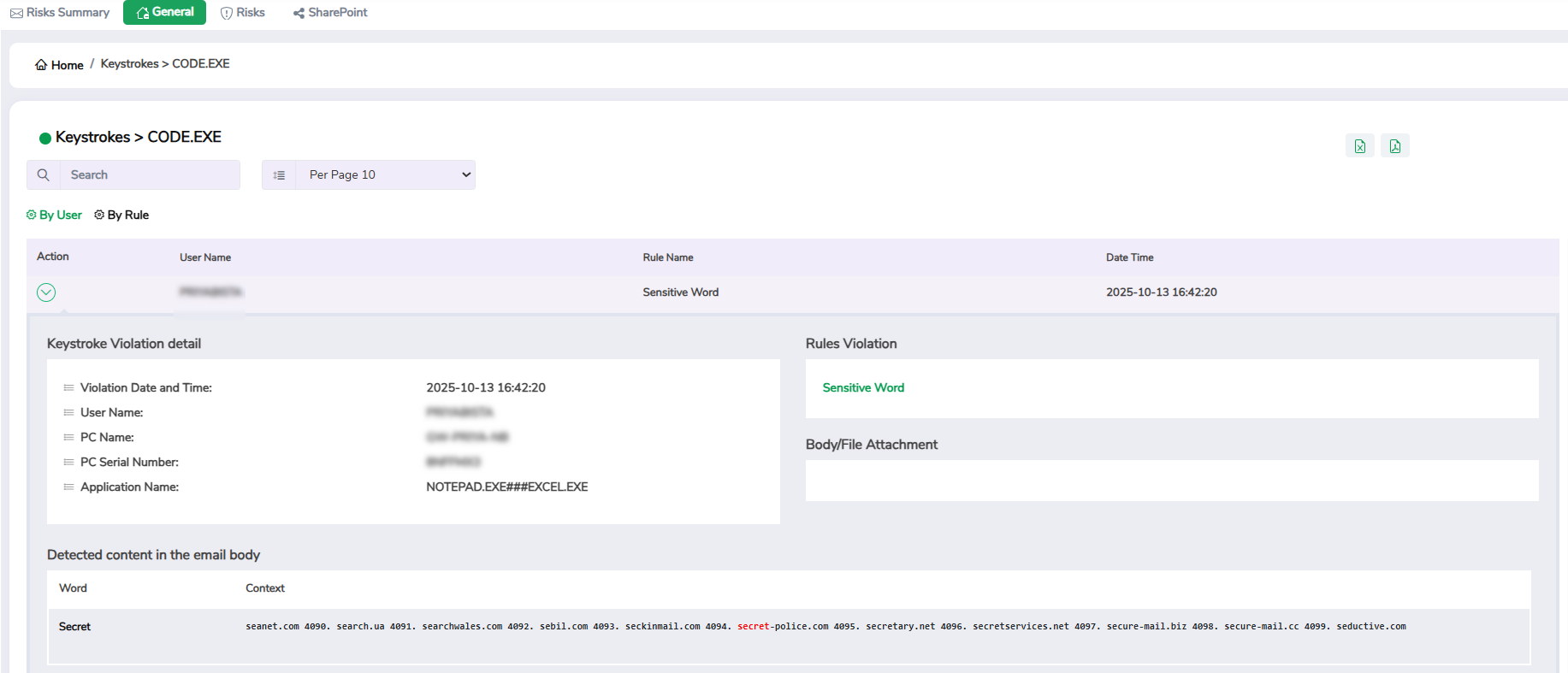
9. Key Stroke Capture of Monitored Phrases
This widget helps you detect specific keywords or phrases typed by users that match predefined monitoring criteria (for example, financial terms, project codes, or classified labels). It helps detect early signs of policy violations, insider threats, or attempts to exfiltrate sensitive data through manual entry or chat messages.
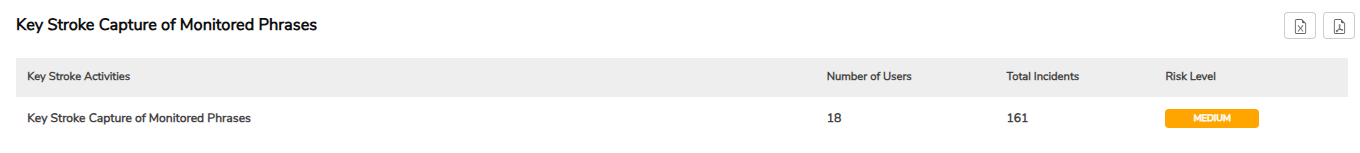
Click a specific record to view detailed information, including the username, application name, PC name, and violation date and time. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
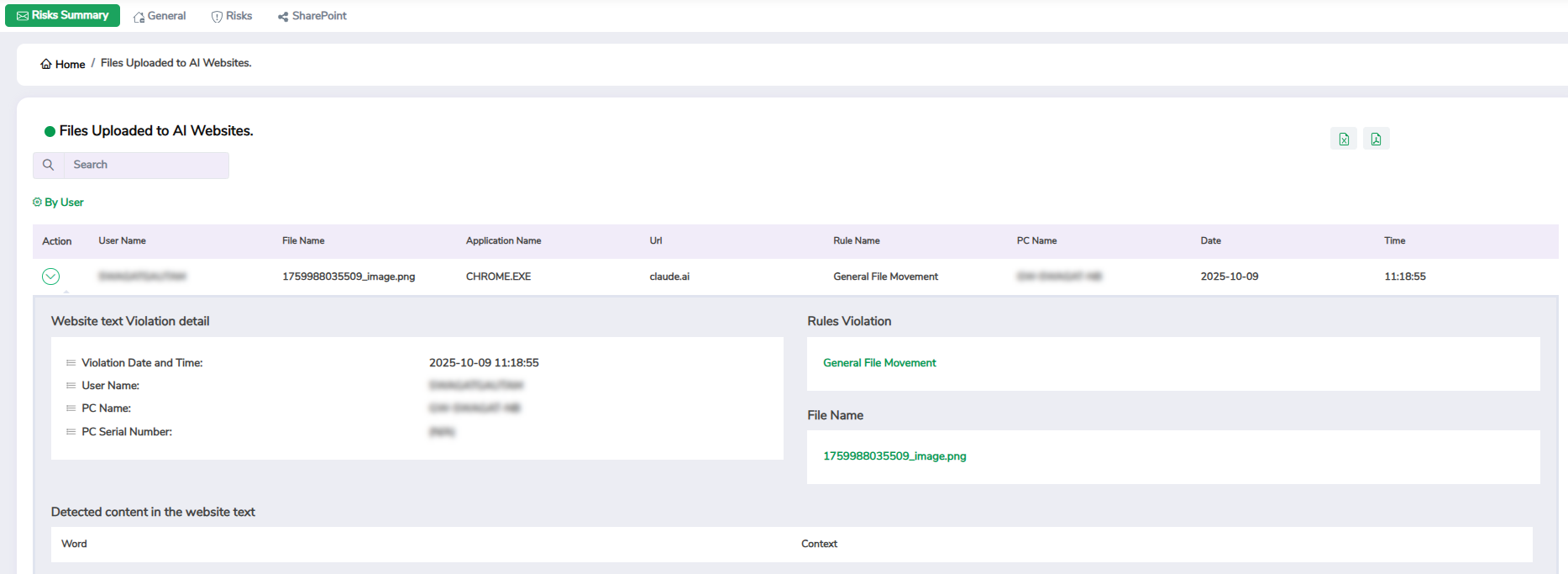
10. Usage Of AI Tools
This widget helps you track any instance where corporate files are uploaded to AI-powered platforms such as ChatGPT and Copilot. These tools may inadvertently store or process sensitive information externally.
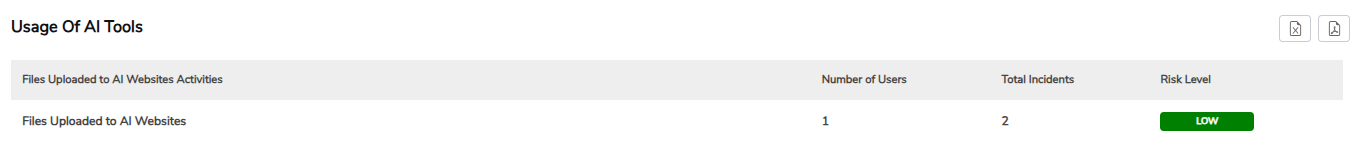
Click a specific record to view detailed information, including the username, application name, URL, PC name, and violation date and time. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
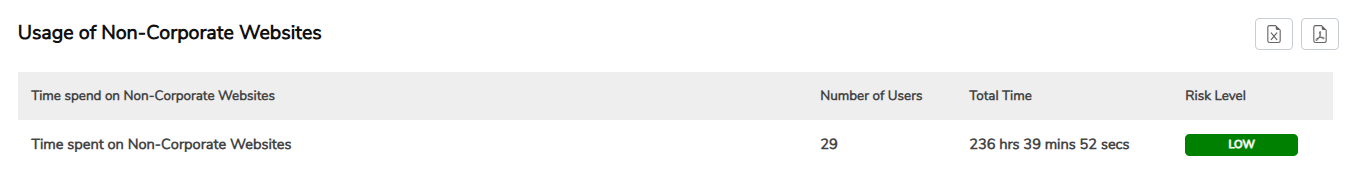
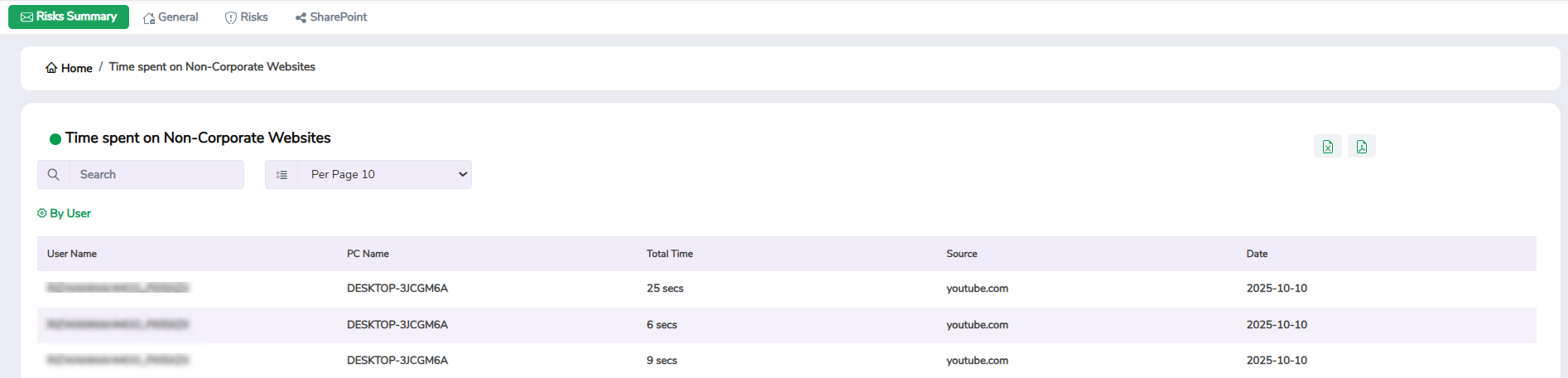
11. Usage of Non-Corporate Websites
This widget helps you track how much time users spend browsing or interacting with non-corporate websites. It helps identify productivity risks and potential exposure to untrusted domains.
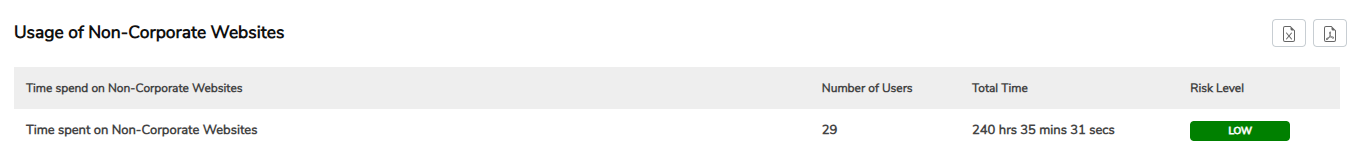
Click a specific record to view detailed information, including the username, PC name, website source, total time spent on the website, and violation date. Use the search box at the top to quickly filter specific information.
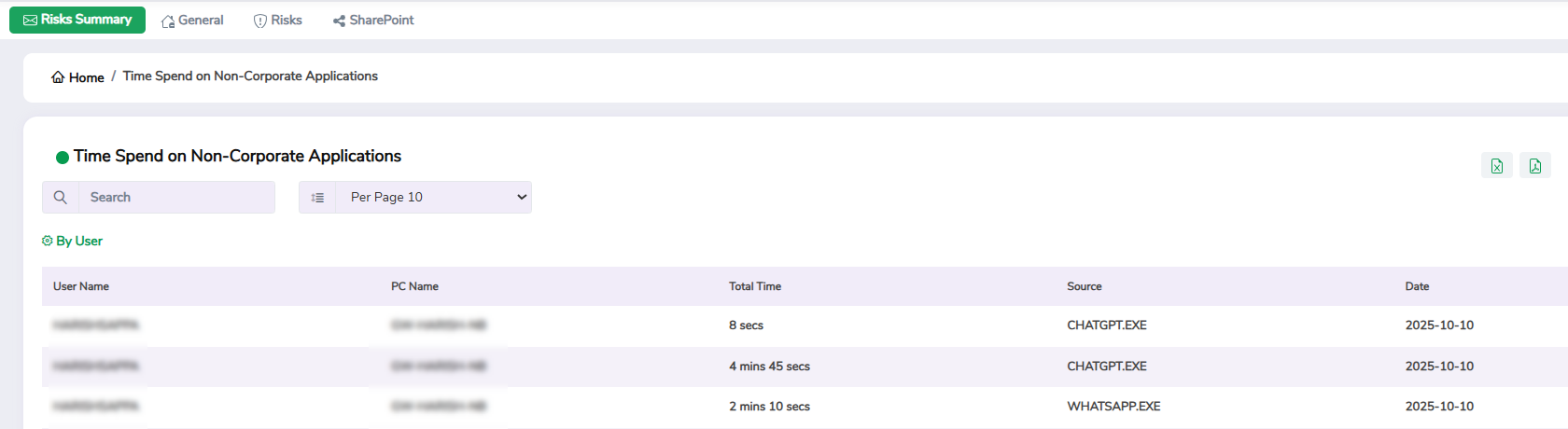
12. Usage of Non-Corporate Applications
This widget helps you monitor the use of unapproved applications that are not part of your organisation’s authorised software list. Frequent use of such tools can introduce vulnerabilities, create compliance risks, or bypass existing security controls.
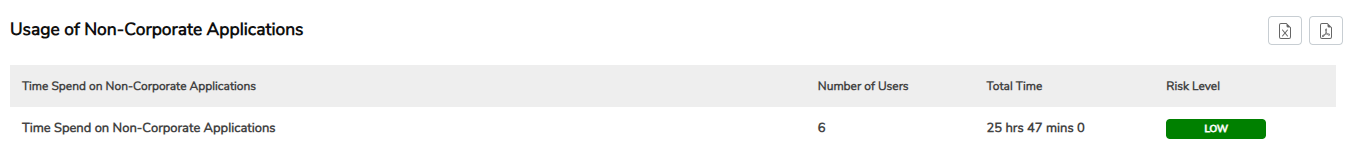
Click a specific record to view detailed information, including the username, PC name, application source, total time spent on the application, and violation date. Use the search box at the top to quickly filter specific information.
General Dashboard
The General Dashboard provides an overview of day-to-day user and system activities across your organisation. It helps you monitor how users interact with applications, websites, and files, and understand how data moves within your network.
You can use the General Dashboard for quick executive summaries and daily monitoring. This dashboard focuses on operational visibility, showing who is active, what they are doing, and how data is being accessed, shared, or transferred.
You can access the General Dashboard from the Dashboard section in the GuardWare INSIGHT Management Console.
Widgets in General Dashboard
Category
Widget Name
System Activity
File Transfers & Applications
Email & Web Communication
Printing & Document Access
Data Loss Prevention (DLP)
User Behaviour
1. PCs Online
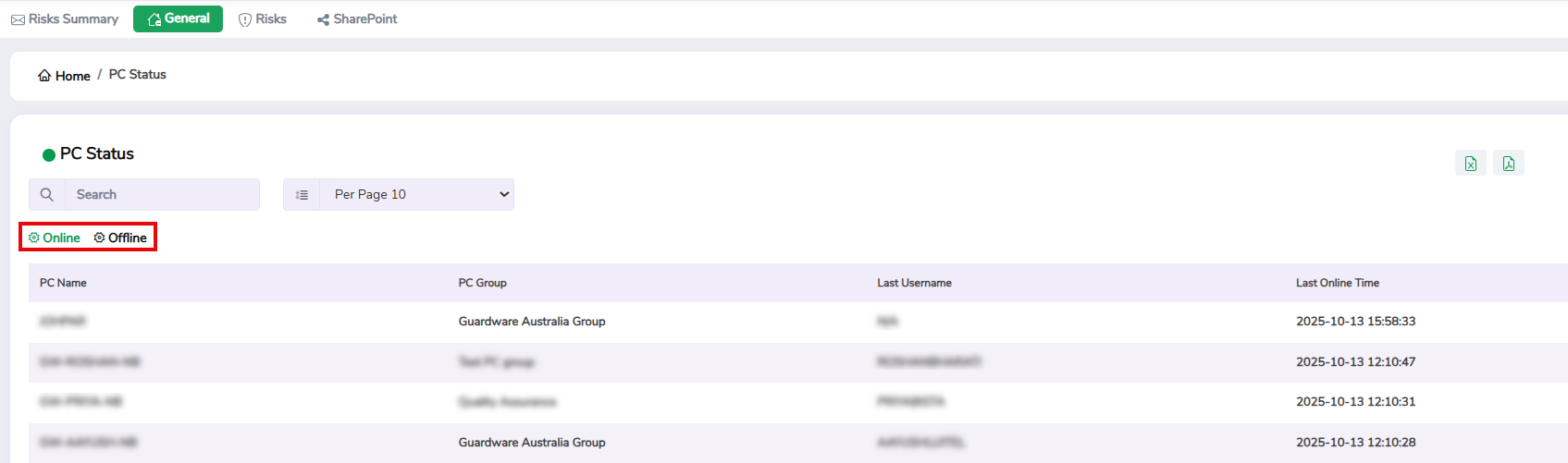
This widget shows the total number of PCs that are online or offline during the selected time period. It helps you monitor endpoint availability and determine which systems are active or inactive across the network.
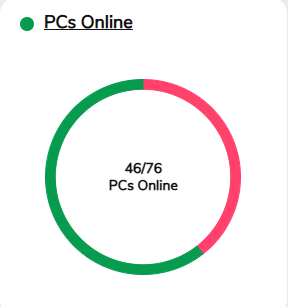
Click the widget to view detailed information, including the PC name, PC group, username, and last online time. Use the Online and Offline tabs to switch between active and inactive PCs, and use the search box at the top to quickly filter specific results.
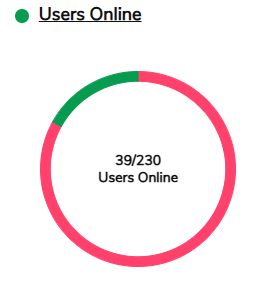
2. Users Online
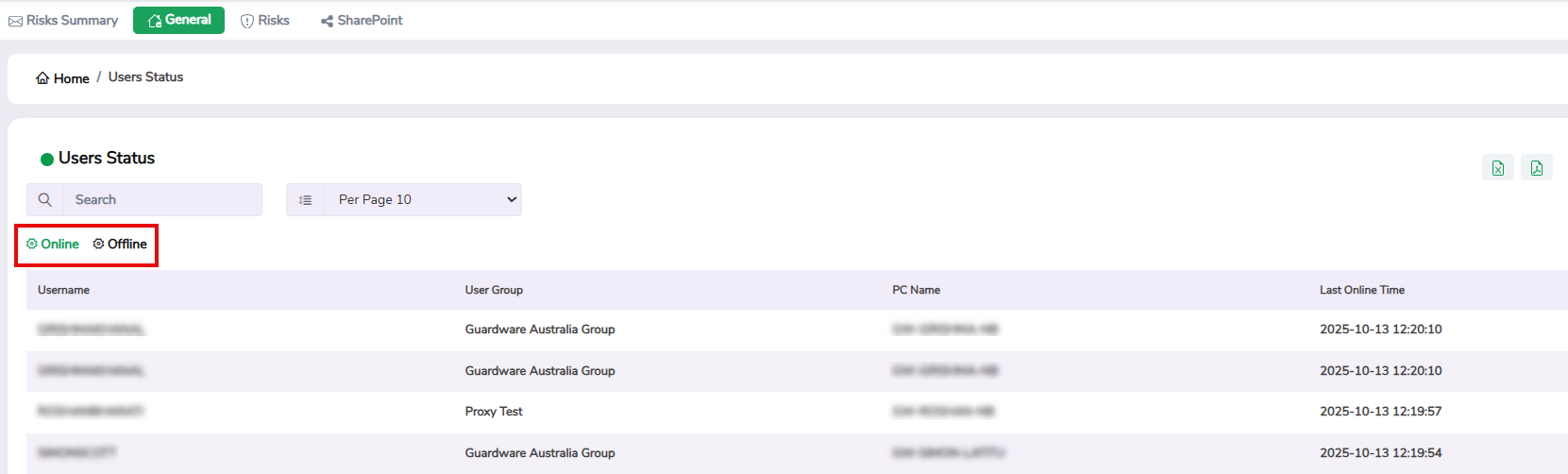
This widget displays the total number of users who are online or offline within the selected time period. It helps you track user activity levels and session availability.
Click the widget to view detailed information, including the username, user group, PC name, and last online time. Use the Online and Offline tabs to switch between active and inactive users, and use the search box at the top to quickly filter specific results.
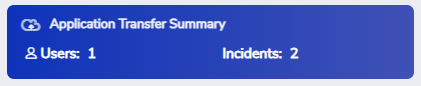
3. Application Transfer Summary
This widget summarises the total number of users and files transferred using applications or cloud-based services such as Dropbox, Google Drive, OneDrive, FileZilla, and WhatsApp. Clicking the widget takes you to the Application Transfers widget, where you can see more details.
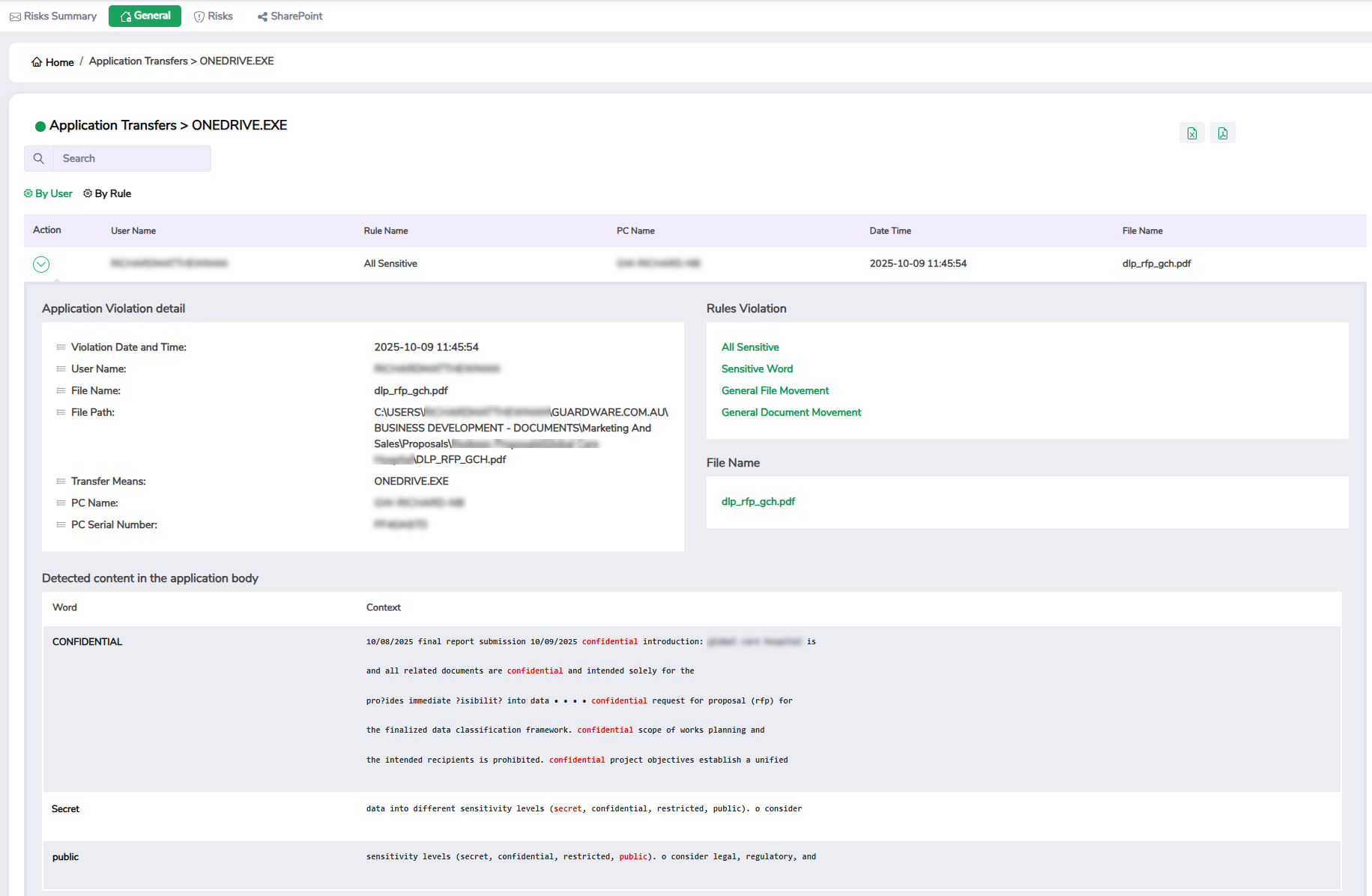
4. Application Transfers
This widget helps you track policy violations detected during file transfers through specific applications. It provides visibility into tools, whether corporate-approved or not, being used to move data and users involved in moving the data, helping identify potential data-leakage channels or policy violations. You can filter the data by application name, rule, and user.
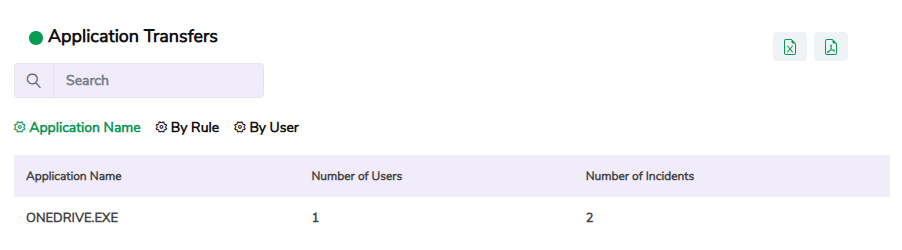
Click a specific record to view detailed information, including the application name, username, rule name, PC name, and the date and time of the violation.
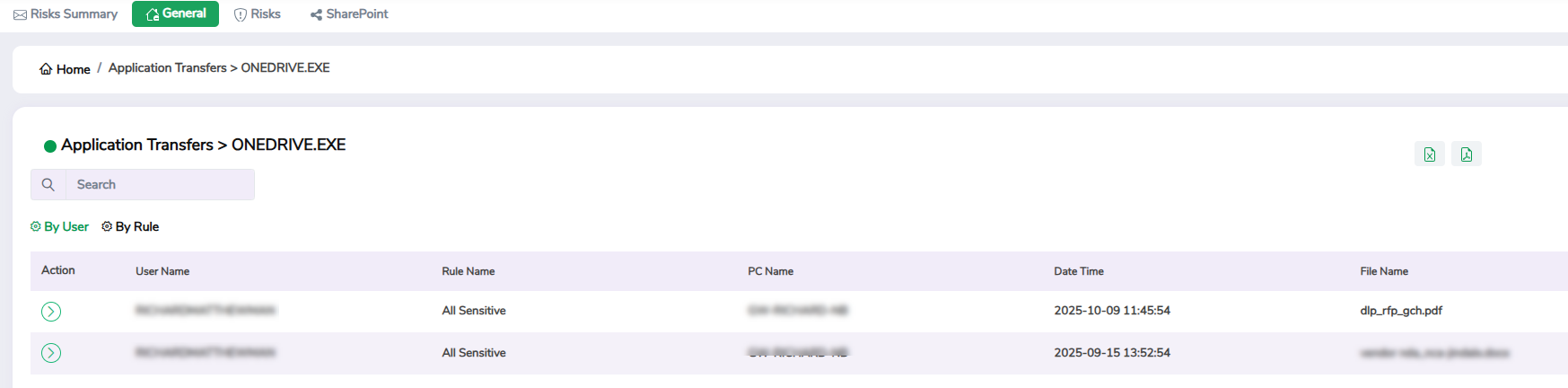
Use the Arrow icon in the Action column to further drill down into details like detected content in the application body, transfer means, and so on. Use the search box at the top to quickly filter specific information.
5. Printed Files Summary
This widget summarises the total number of files printed within your organisation, including the total number of users who initiated print jobs. Clicking the widget takes you to the Printed Files widget, where you can see more details.
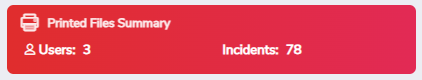
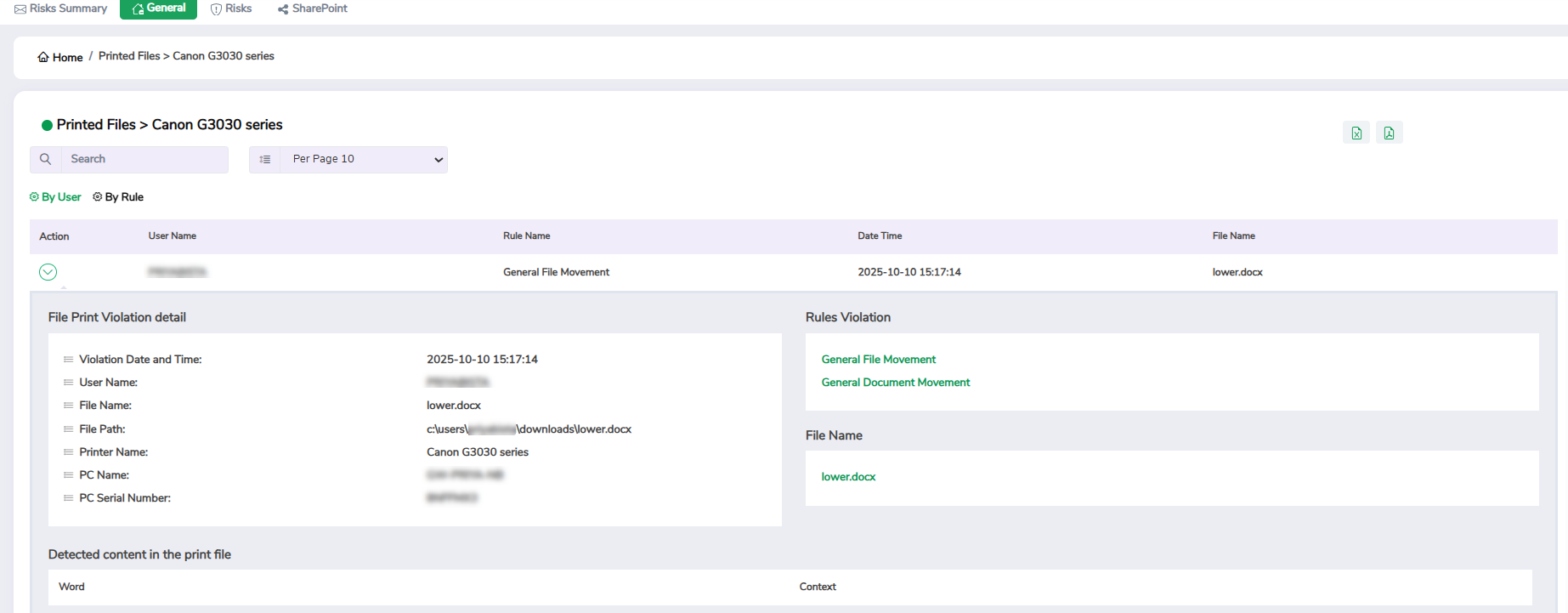
6. Printed Files
This widget helps you track violations related to printing activities and identify potential data leaks through physical copies. It helps you identify unauthorised or excessive printing of sensitive or confidential documents and trace which users and devices were involved. You can filter the data by printer name, rule, and user.
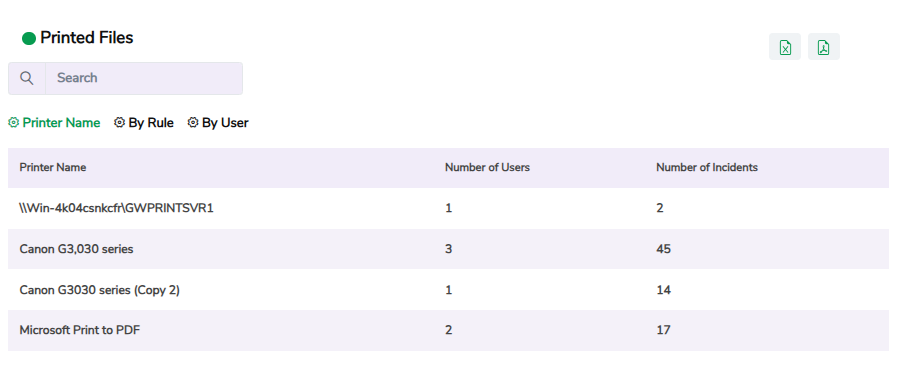
Click a specific record to view detailed information, including the username, printer name, rule name, PC name, file name, and the date and time of the violation. Use the Arrow icon in the Action column to further drill down into details like detected content in the print file, file path, and so on. Use the search box at the top to quickly filter specific information.
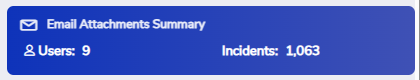
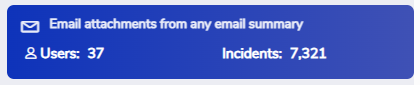
7. Email Attachments Summary
This widget shows the total number of email attachments sent via both corporate and non-corporate email accounts, including the total number of users who sent the attachment. Clicking the widget takes you to the Emailing of Attachments from Any Email Address widget, where you can see more details.
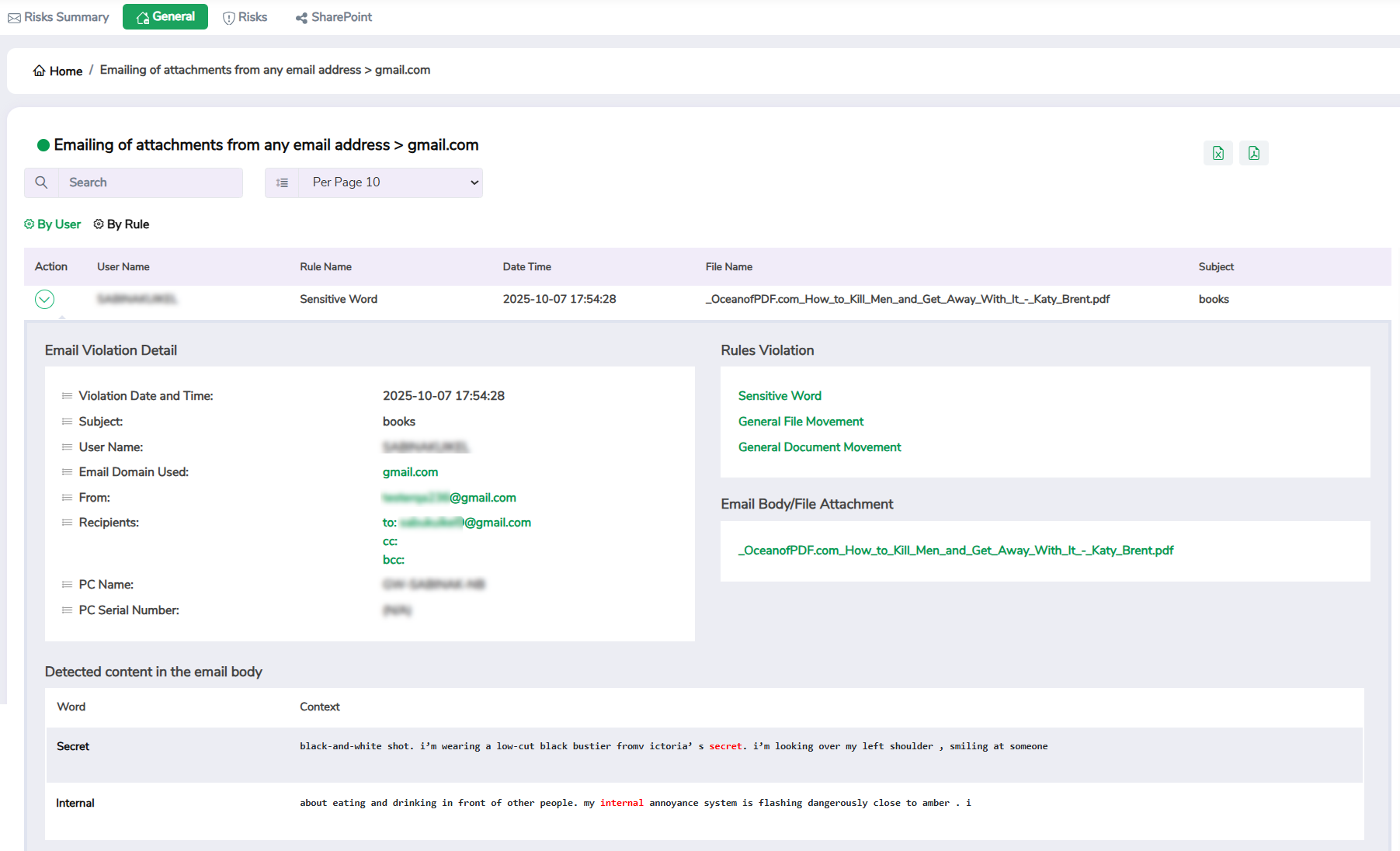
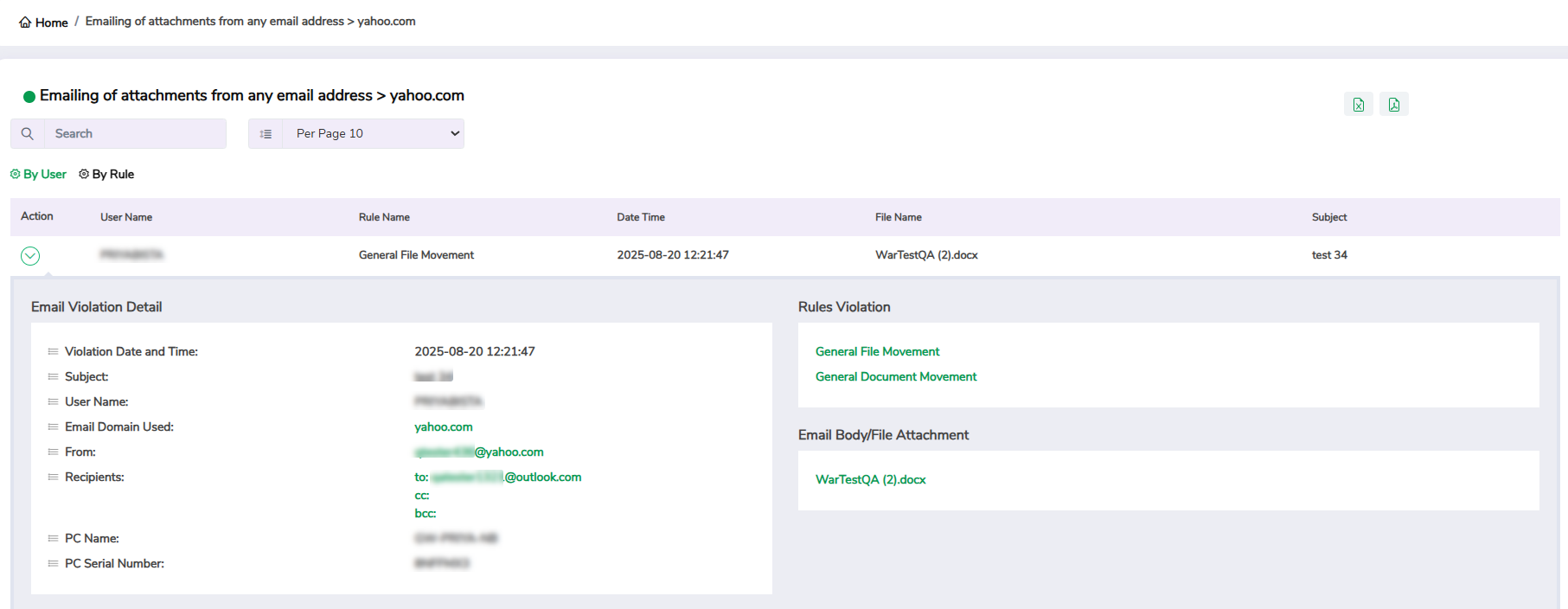
8. Emailing of Attachments from Any Email Address
This widget helps you track violations involving email attachments sent from any email account, including both corporate and non-corporate. It helps you identify when sensitive files are being shared externally and track which users are sending attachments that may violate your organisation’s policies. You can filter the data by email provider, violation rule, and user.
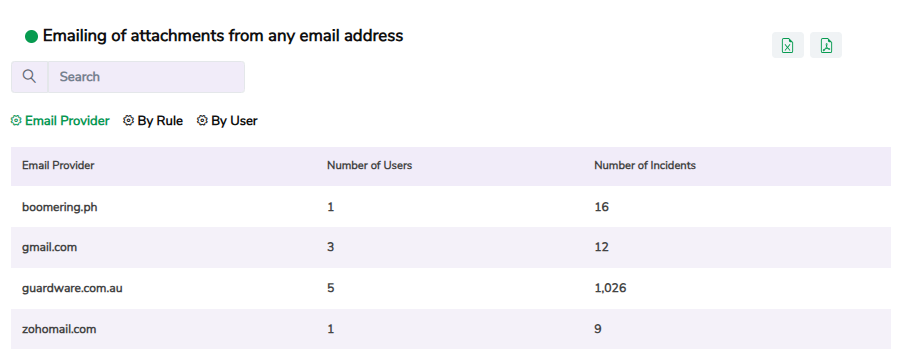
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
9. Website Uploads Summary
This widget shows the total number of file uploads or transfers made to corporate and non-corporate websites, such as public file-sharing services or personal cloud storage platforms, including the total number of users who initiated the upload. Clicking the widget takes you to the Website Incidents widget, where you can see more details.
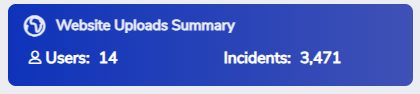
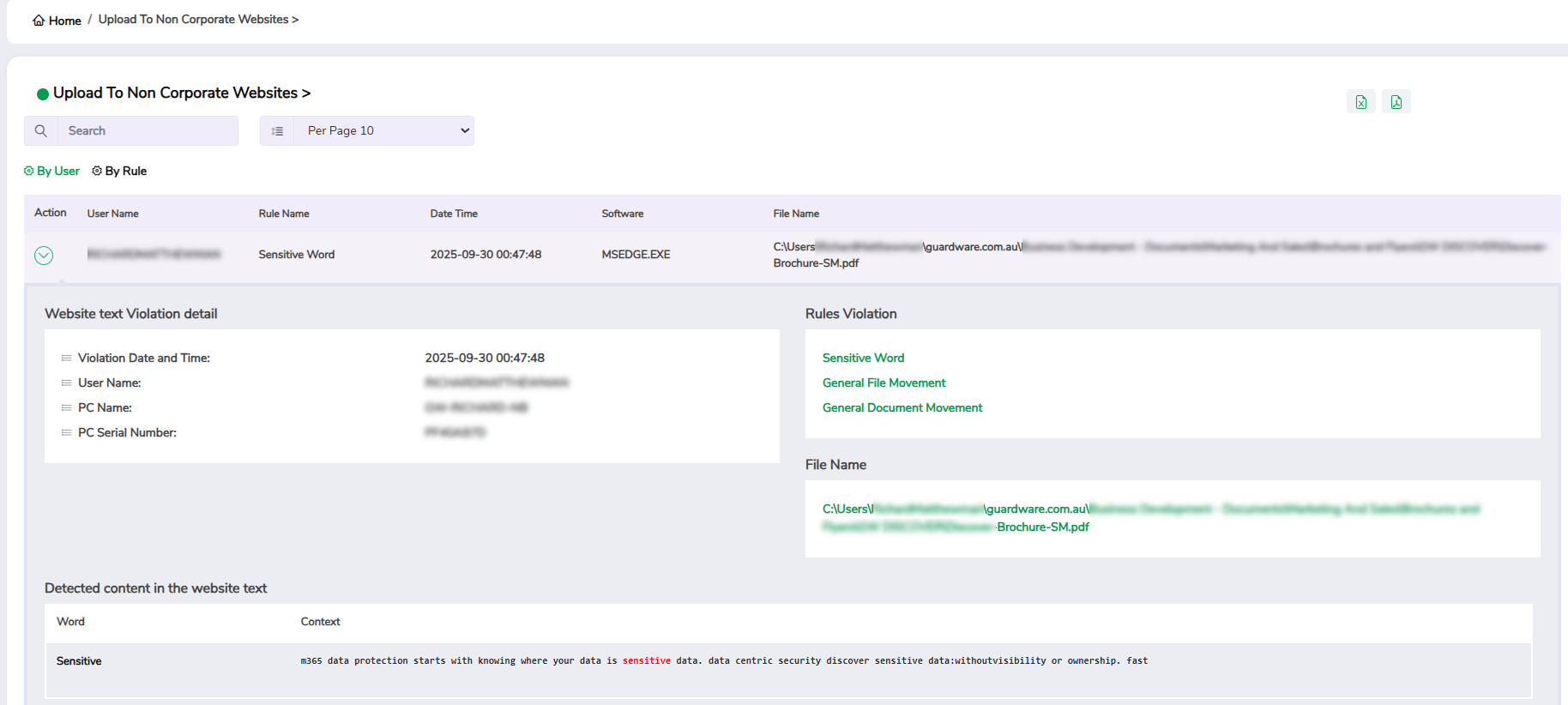
10. Website Incidents
This widget helps you detect and prevent potential data leaks by identifying websites where sensitive content was uploaded or shared. You can filter the data by URL, rule, and user.
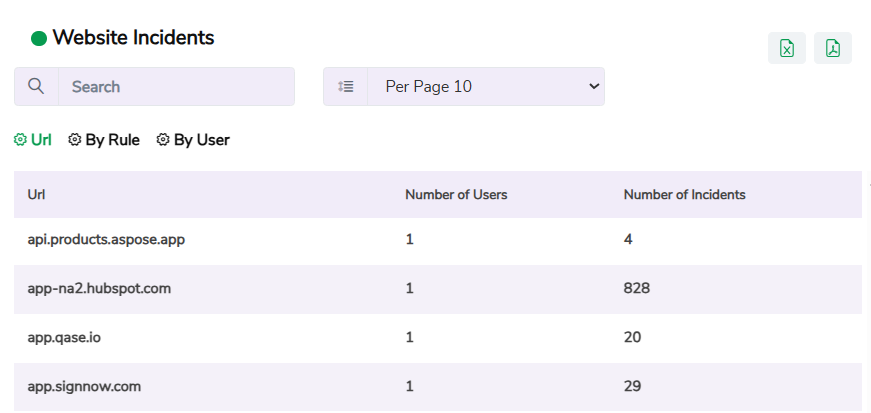
Click a specific record to view detailed information, including the username, rule name, URL, the date and time of the violation, software used, and the name and path of the file uploaded. Use the Arrow icon in the Action column to further drill down into details like detected content in the website text, PC name, and so on. Use the search box at the top to quickly filter specific information.
11. Email Body Summary
This widget displays the total number of emails that violated content rules within the body of the message, including the total number of users who sent them. Clicking the widget takes you to the Email Body widget, where you can see more details.
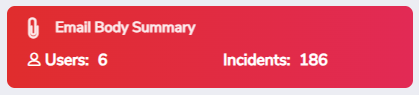
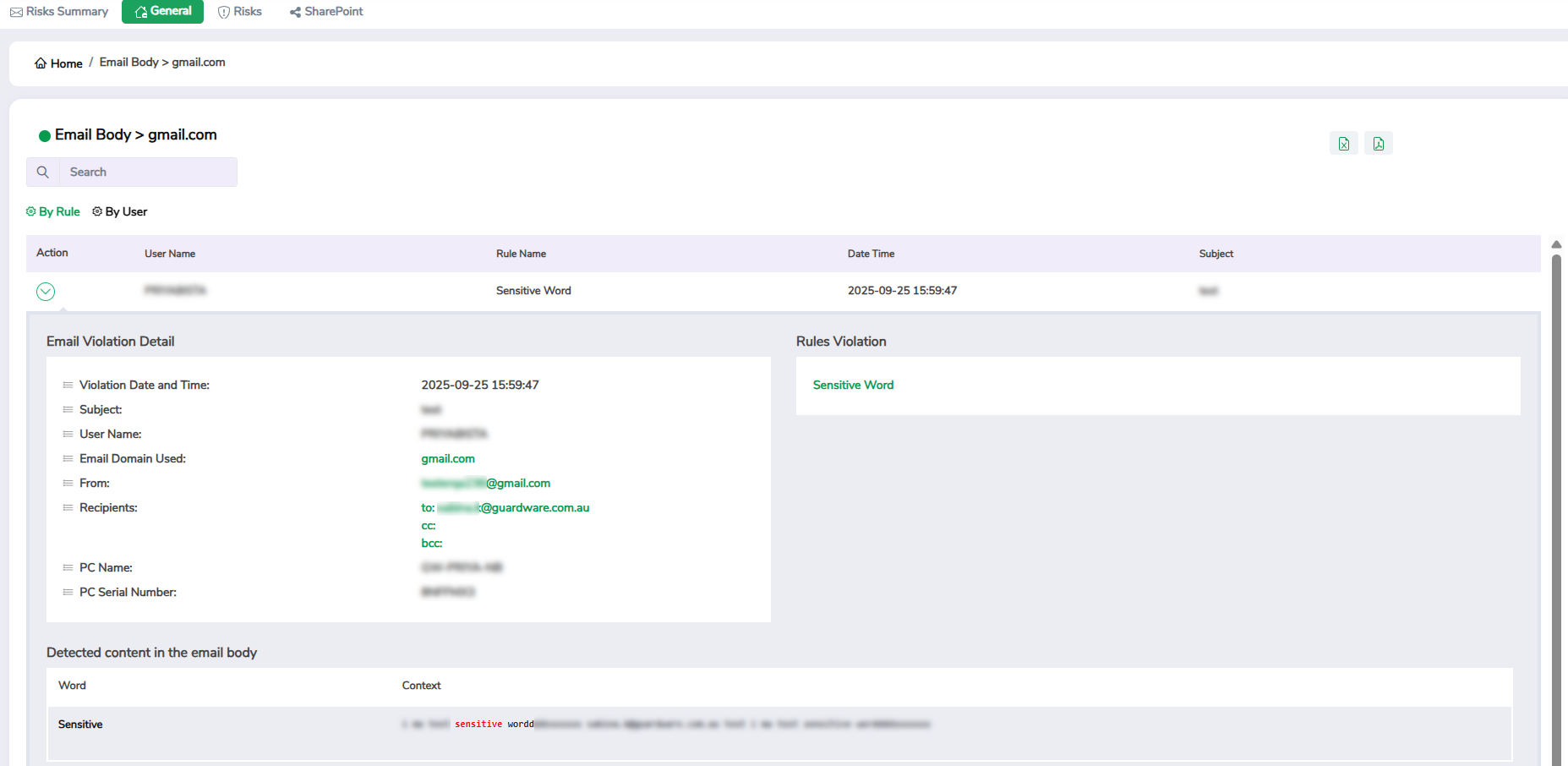
12. Email Body
This widget helps you track details of emails containing restricted words, sensitive information, or policy breaches written directly in the message text. It helps you assess whether users are adhering to communication policies and prevent exposure of sensitive data through email. You can filter the data by email provider, rule, and user.
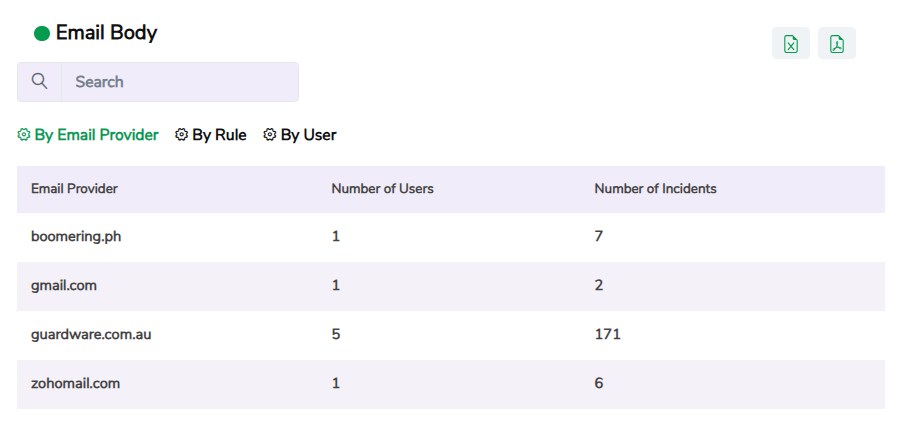
Click a specific record to view detailed information, including the email provider, username, rule name, URL, the date and time of the violation, and email subject. Use the Arrow icon in the Action column to further drill down into details like sender’s and receiver’s email, detected content in the email body, and so on. Use the search box at the top to quickly filter specific information.
13. Website Text Summary
This widget shows the total number of sensitive words or phrases posted on websites, along with the total number of users who posted them. Clicking the widget takes you to the Website Text widget, where you can see more details.
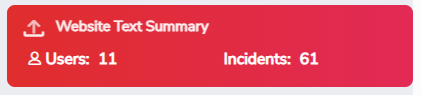
14. Website Text
This widget helps you track confidential or restricted text or phrases shared on websites or through online forms. You can filter the data by URL, rule, and user.
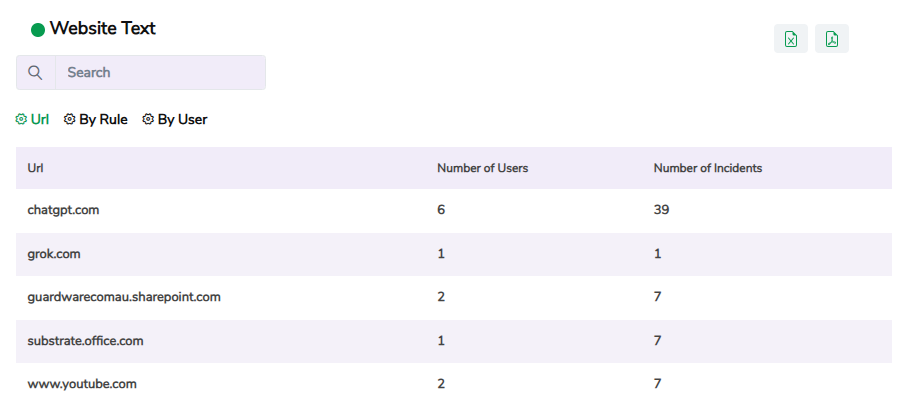
Click a specific record to view detailed information, including the username, rule name, URL, and the date and time of the violation. Use the Arrow icon in the Action column to further drill down into details like detected content in the website text, PC name, and so on. Use the search box at the top to quickly filter specific information.
15. Storage Transfer Summary
This widget displays the total number of files copied or transferred to USB drives or external storage devices, along with the total number of users who performed these actions. Clicking the widget takes you to the Storage Transfers widget, where you can see more details.
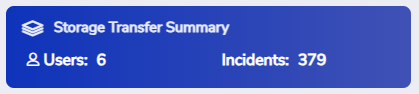
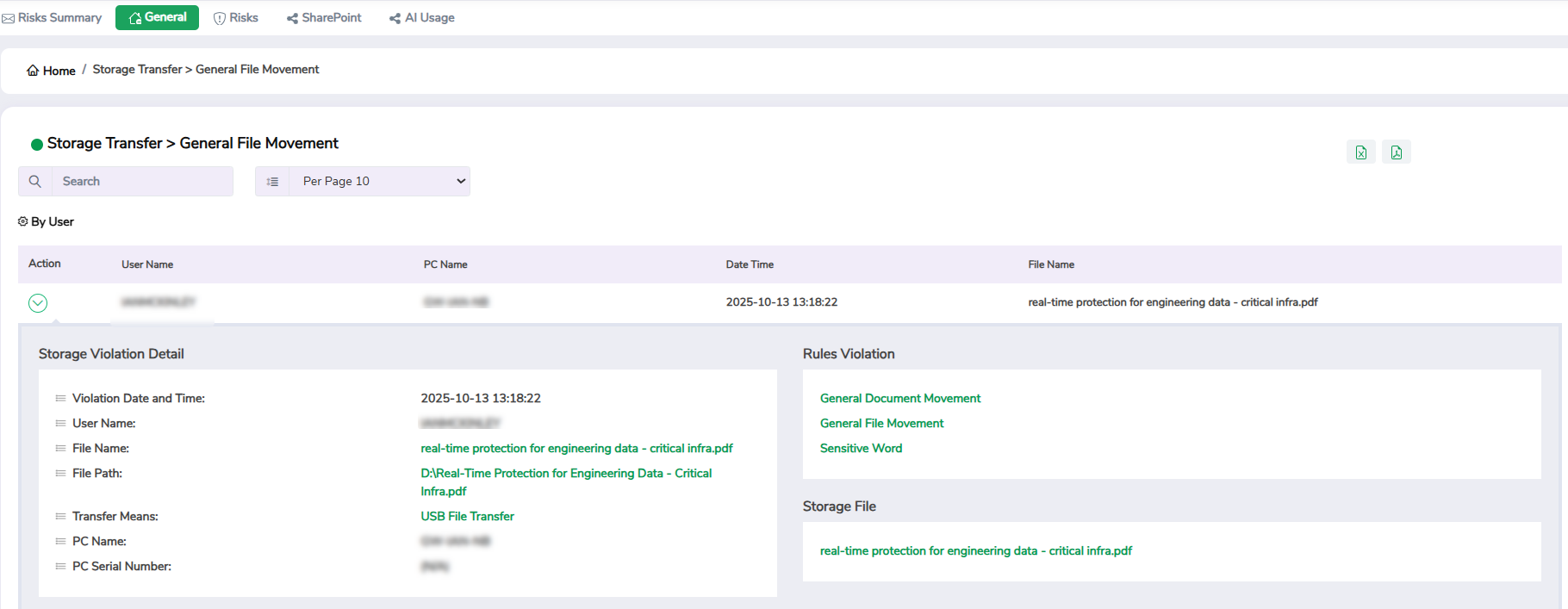
16. Storage Transfers
This widget helps you track which users copied files and whether the transfers align with your organisation’s policies by providing a detailed view of files transferred to USB or external storage devices. It helps detect and prevent unauthorised offline data transfers or potential data leakage through removable media. You can filter the data by rule and user.
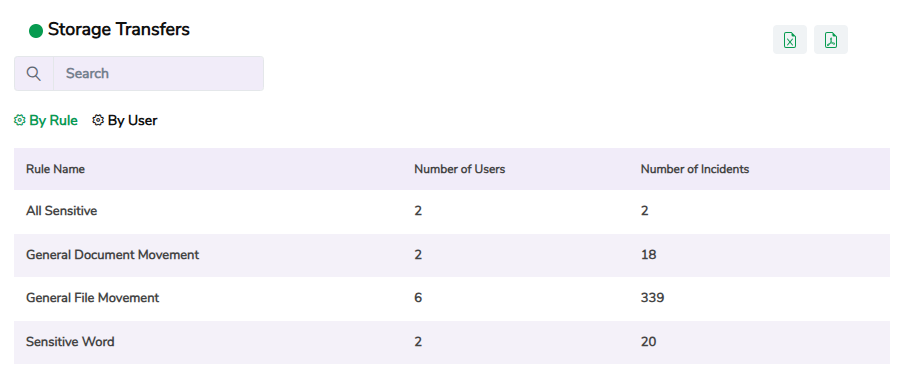
Click a specific record to view detailed information, including the username, rule name, PC name, file name, and the date and time of the violation. Use the Arrow icon in the Action column to further drill down into details like file path, transfer means, and so on. Use the search box at the top to quickly filter specific information.
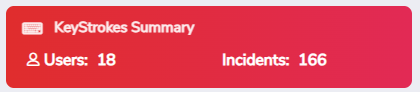
17. Keystrokes Summary
This widget displays the total number of sensitive words or monitored phrases typed by users, including the total number of users who typed them. Clicking the widget takes you to the Keystrokes widget, where you can see more details.
18. Keystrokes
This widget helps you track sensitive phrases typed by users. It helps you identify insider threats and monitor attempts to manually share confidential information in chat messages, documents, or forms. You can filter the data by application, rule, and user.
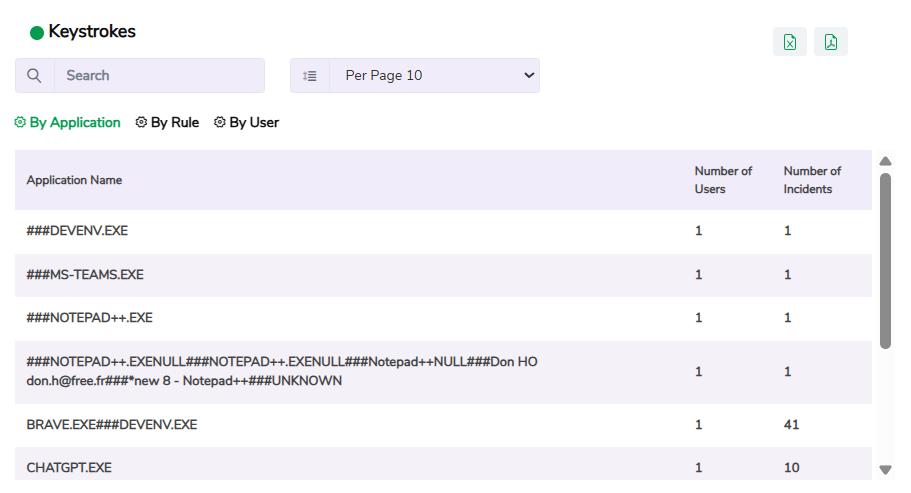
Click a specific record to view detailed information, including the application name, username, rule name, and the date and time of the violation. Use the Arrow icon in the Action column to further drill down into details. Use the search box at the top to quickly filter specific information.
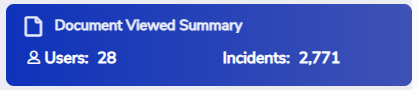
19. Document Viewed Summary
This widget shows the total number of documents accessed or opened, along with the total number of users who viewed them. Clicking the widget takes you to the Document View widget, where you can see more details.
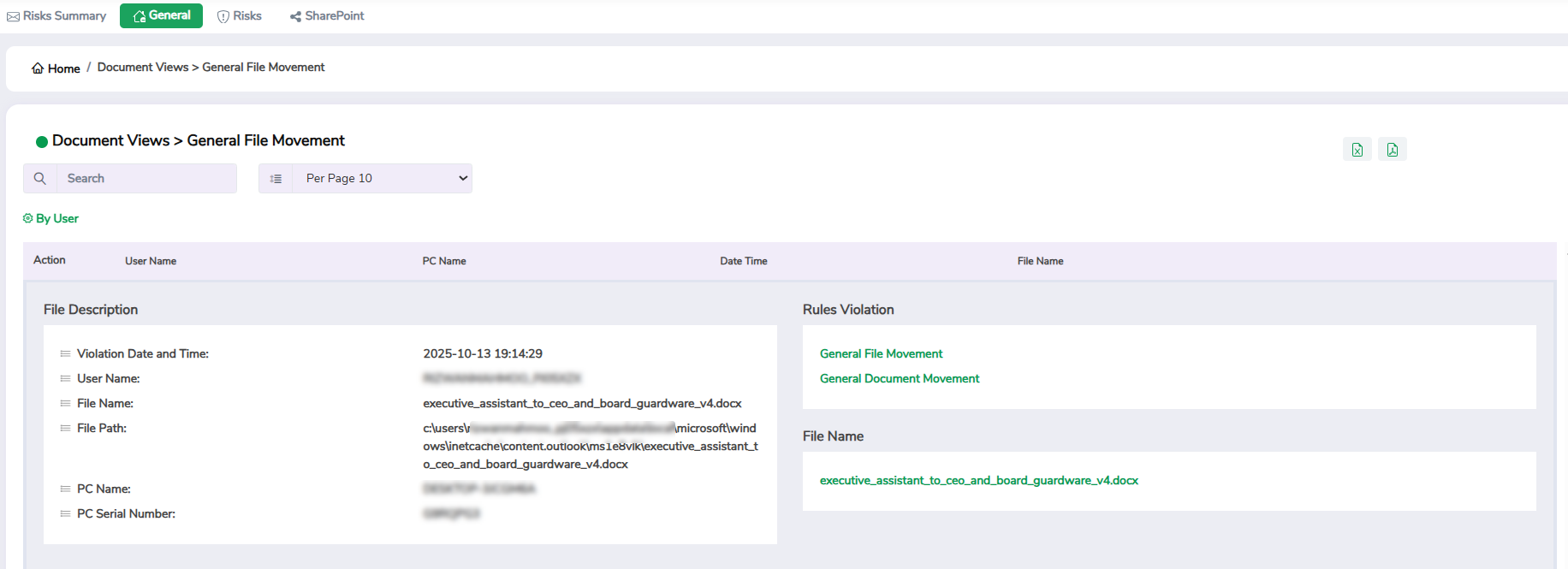
20. Document View
This widget helps you monitor document access patterns and ensure that confidential files are being viewed only by authorised users within authorised limits. You can filter the data by rule and user.
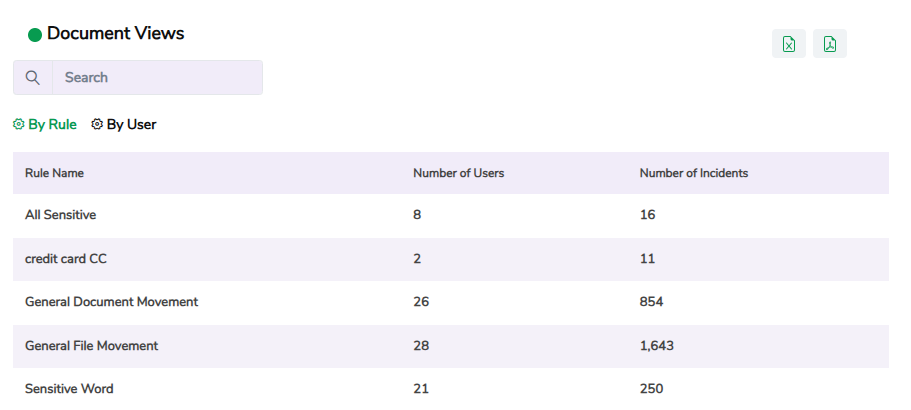
Click a specific record to view detailed information, including the username, rule name, PC name, file name, and the date and time of the violation. Use the Arrow icon in the Action column to further drill down into details. Use the search box at the top to quickly filter specific information.
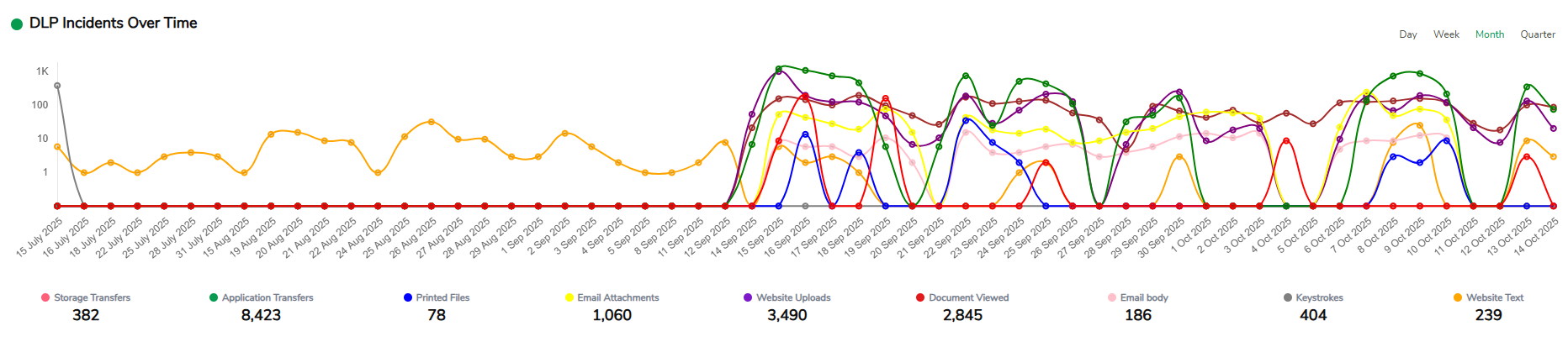
21. DLP Incidents Over Time
This widget displays a trend graph of Data Loss Prevention (DLP) incidents over time. It helps you analyse how frequently violations occur in each monitored category, such as email, printing, storage and application transfers, website, document view, and keystrokes. You can filter the data by day, week, month, and quarter.
22. DLP Incidents
This widget lists the total number of policy violations detected across all monitored rules on each monitored category, such as email, printing, storage and application transfers, website, document view, and keystrokes. It gives a consolidated view of where sensitive data breaches or unauthorised activities occurred.
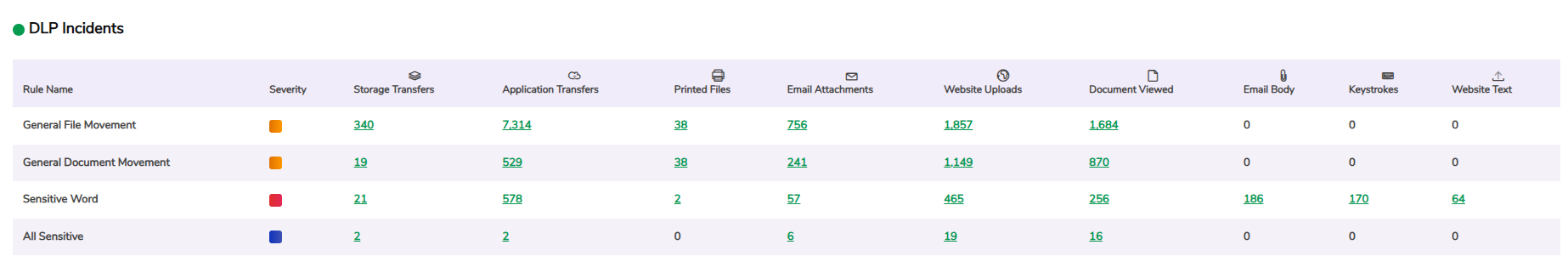
Click on a record to view detailed information about each violation on each monitored category. Use the Arrow icon in the Action column to further drill down into details. Use the search box at the top to quickly filter specific information.
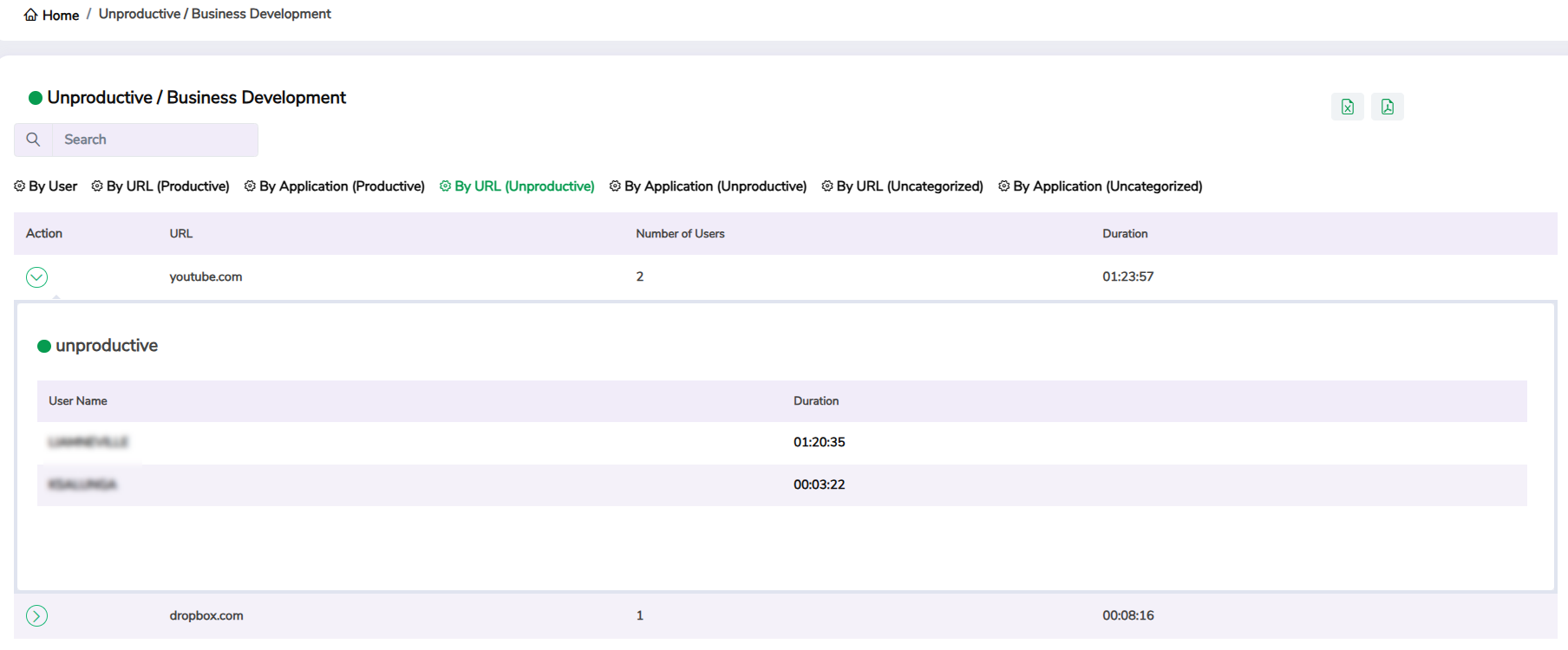
23. Productivity
This widget shows time spent by users and user groups on productive, unproductive, or uncategorised applications and websites. These categories are configured in the GuardWare INSIGHT Management Console. It helps you evaluate how users spend their time and identify opportunities to improve efficiency.
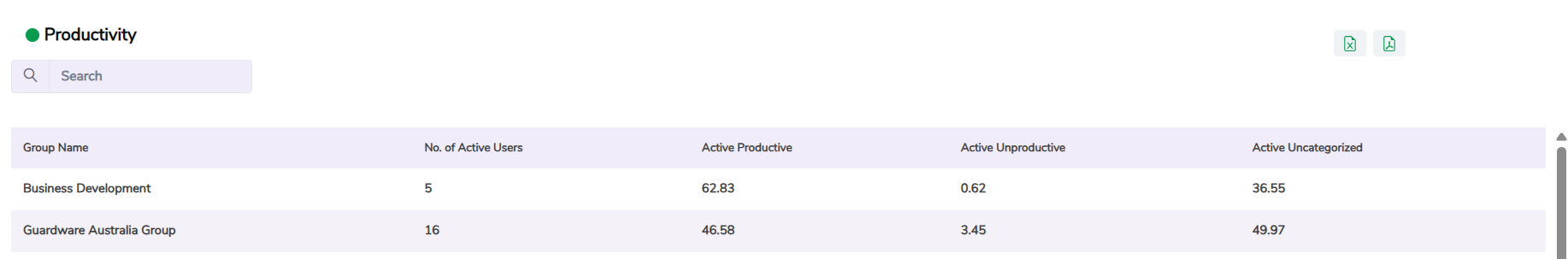
Click on a specific group to view detailed information, including the username and time spent on the productive, unproductive, and uncategorised websites and applications.
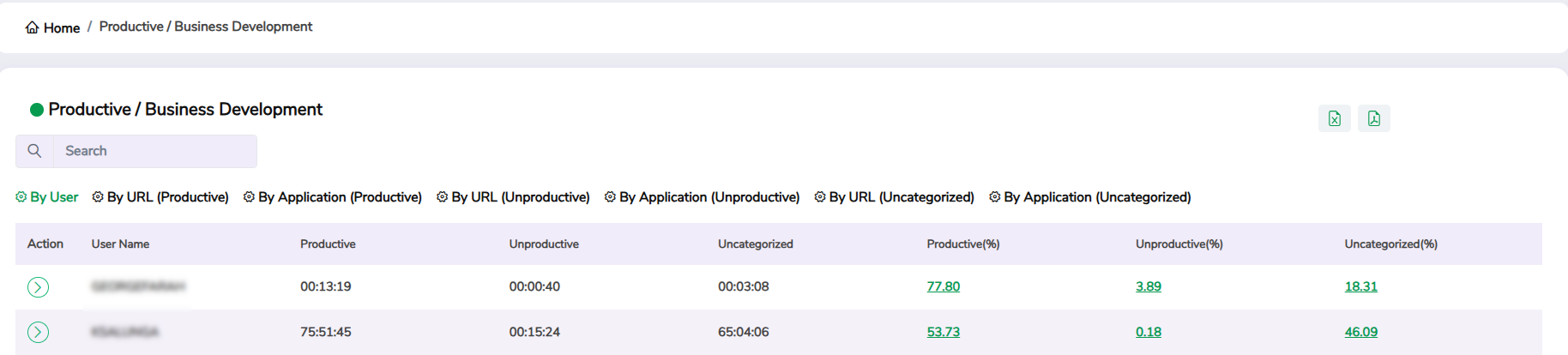
You can filter the data by user, productive, unproductive, and uncategorised URL, and productive, unproductive, and uncategorised Application.

Use the arrow icon in the Action column to further drill down into details. Use the search box at the top to quickly filter specific information.
Risks Dashboard
The Risks Dashboard provides a detailed view of high-risk user activities and policy violations occurring across your organisation. It consolidates critical data from multiple monitoring categories, such as file transfers, application usage, email activity, and printing, to help you detect, assess, and respond to potential data security threats.
Unlike the Risk Summary Dashboard, which focuses on summarised risk levels, the Risks Dashboard delivers deeper visibility into the specific sources of risk. It highlights where violations are happening, which users are involved, and how sensitive information is being accessed, shared, or transferred.
This dashboard is particularly useful for security and compliance teams who need to investigate incidents, track behavioural patterns, and ensure adherence to data protection policies. Use the Risks Dashboard when you need a focused view of who, what, and how risks are occurring within your organisation.
You can access the Risks Dashboard from the Dashboard section in the GuardWare INSIGHT Management Console.
Widgets in Risks Dashboard
Category
Widget Name
System Activity
Storage Devices
Keystrokes
Cloud Storage
Website Uploads
Email Attachments
Documents
Data Loss Prevention (DLP)
Application Control
1. Use of Monitored Non-Organisational Applications Summary
This widget shows the total time users spent on non-organisational applications, such as unauthorised communication or file-sharing tools, along with the number of users involved. Clicking the widget takes you to the Use of Monitored Non-Organisational Applications widget, where you can see more details.
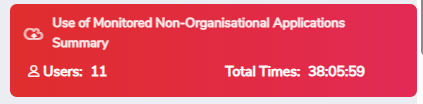
2. Use of Monitored Non-Organisational Applications
This widget helps you identify the use of applications outside authorised corporate systems and assess potential data security or compliance risks. It shows which users used which non-organisational applications, and how much time they spent using them. You can filter the data by application name and user.
Click a specific record to view detailed information. Use the search box at the top to quickly filter specific information.

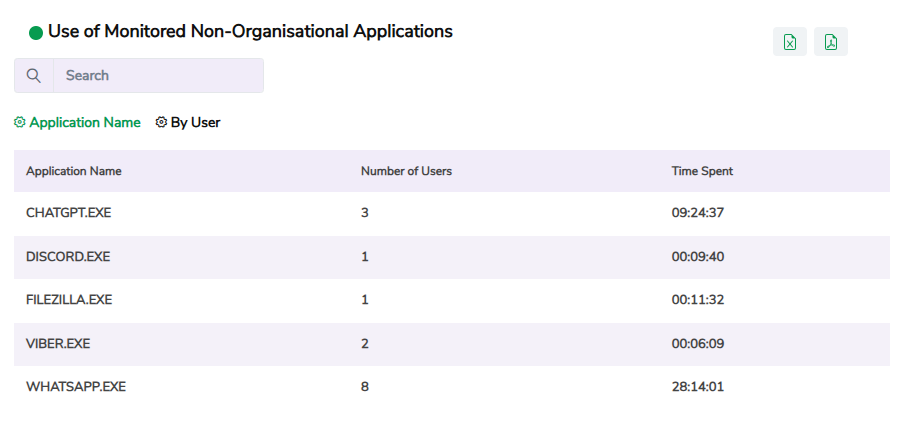
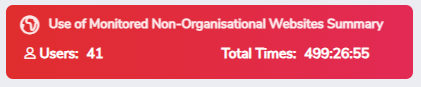
3. Use of Monitored Non-Organisational Websites Summary
This widget displays the total time users spend on non-organisational websites along with the number of users involved. Clicking the widget takes you to the Use of Monitored Non-Organisational Websites widget, where you can see more details.
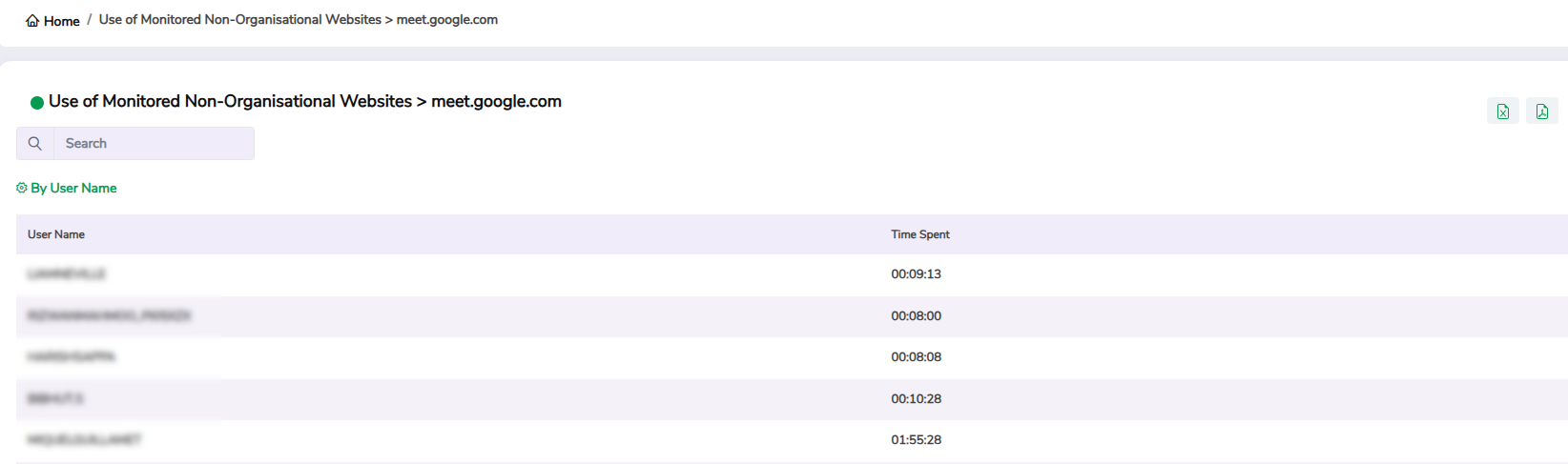
4. Use of Monitored Non-Organisational Websites
This widget helps you identify the use of websites outside corporate domains and identify high-risk browsing activities that may pose security or productivity concerns. It shows which users visited non-organisational websites and how much time they spent on them. You can filter the data by URL and user.

Click a specific record to view detailed information. Use the search box at the top to quickly filter specific information.
5. Use of Non-Corporate OneDrive Folders Summary
This widget shows the total number of files uploaded to or accessed from non-corporate OneDrive folders, including the total number of users involved. Clicking the widget takes you to the Use of Non-Corporate OneDrive Folders widget, where you can see more details.
6. Use of Non-Corporate OneDrive Folders
This widget helps you detect instances where corporate files are being stored or shared through personal OneDrive accounts rather than secured organisational storage. It shows the total number of file uploads made through non-corporate OneDrive folders, and the users who initiated them.
Click a specific record to view detailed information. Use the search box at the top to quickly filter specific information.
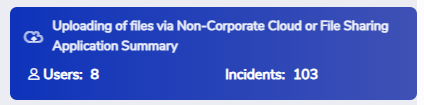
7. Uploading of Files via Non-Corporate Cloud or File-Sharing Application Summary
This widget shows the total number of file uploads made through non-corporate cloud or file-sharing applications, such as Dropbox or Google Drive, and the number of users who initiated them. Clicking the widget takes you to the Uploading of Files via Non-Corporate Cloud or File-Sharing Application widget, where you can see more details.
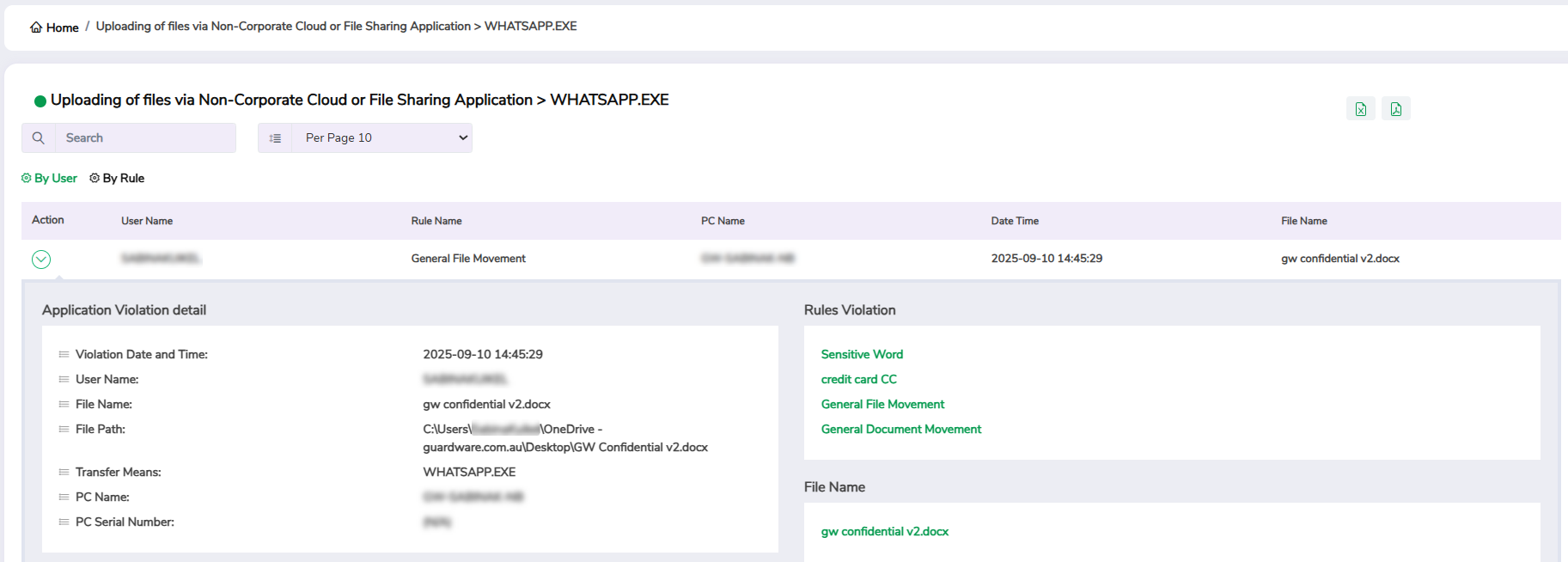
8. Uploading of Files via Non-Corporate Cloud or File-Sharing Application
This widget displays the information on which user uploaded which file on which non-corporate cloud or file-sharing application. It helps you identify unauthorised uploads that may lead to data loss. You can filter the data by application name, rule, and user.
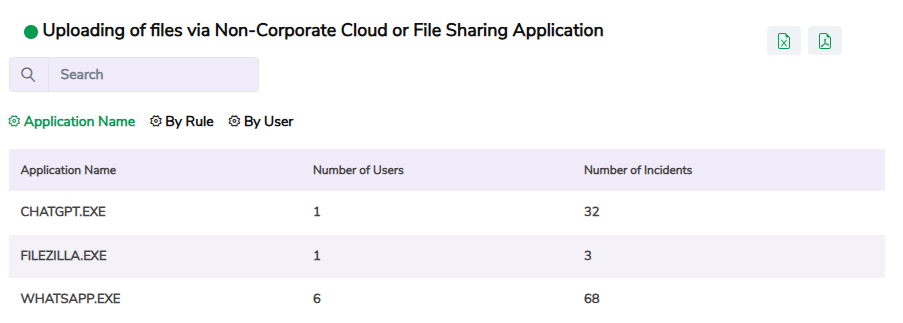
Click a specific record to view detailed information, including the application name, username, rule name, PC name, the date and time of the violation, and the name of the file that was uploaded. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
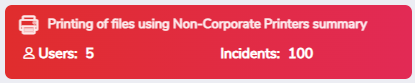
9. Printing of Files Using Non-Corporate Printers Summary
This widget displays the total number of files printed via non-corporate printers, along with the number of users who performed the print jobs. Clicking the widget takes you to the Printing files using non-corporate printers widget, where you can see more details.
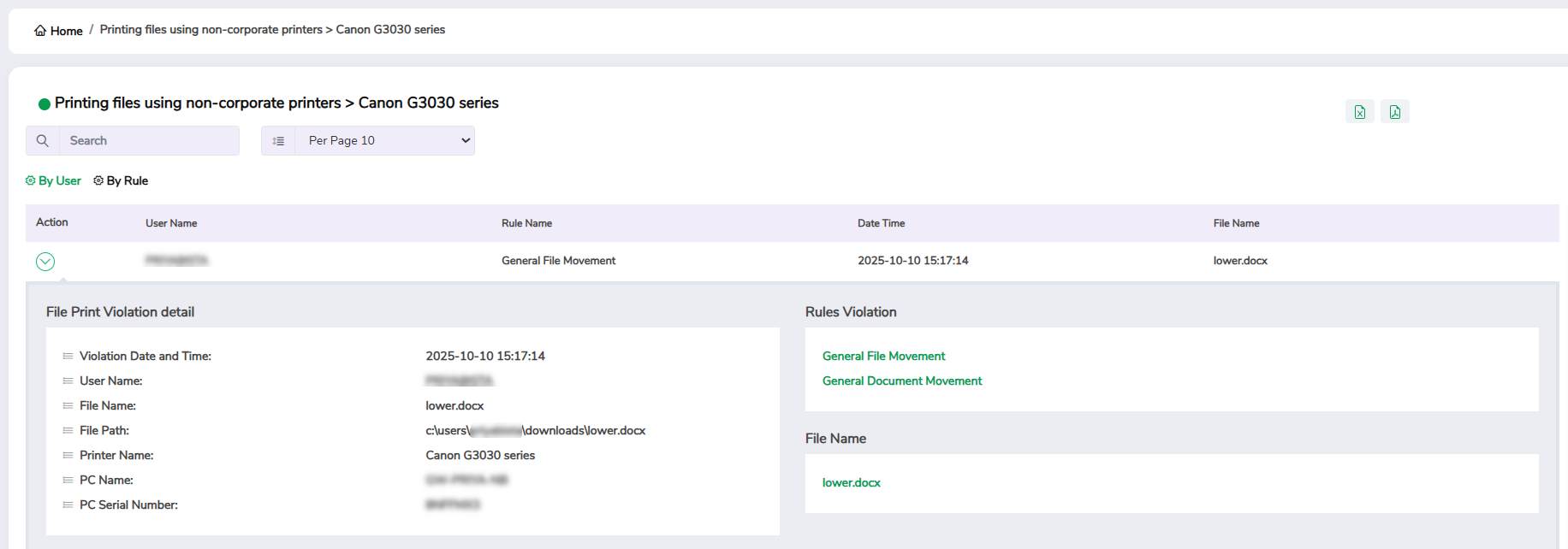
10. Printing files Using Non-Corporate Printers
This widget helps you track files printed using non-corporate or unauthorised printers. It provides visibility into printing activities that may lead to hard-copy data leaks. You can filter the data by printer name, rule, and user.
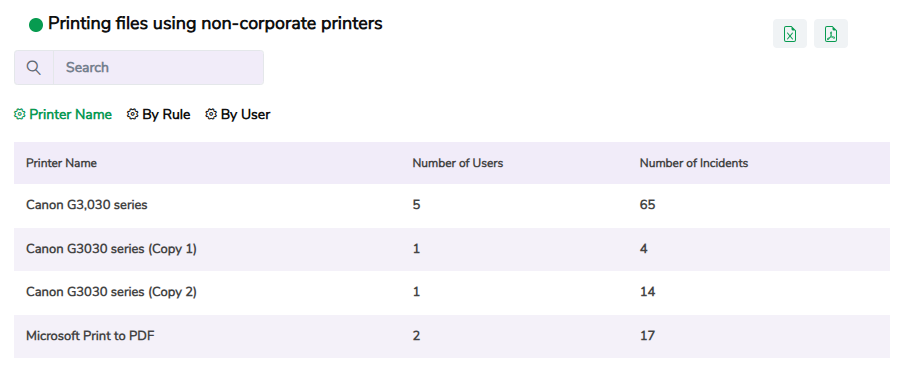
Click a specific record to view detailed information, including the username, file name, file path, printer name, PC name, and violation date and time. Use the Arrow icon in the Action column to further drill down into details, and use the search box at the top to quickly filter specific information.
11. Uploads of Data to Non-Corporate Websites Summary
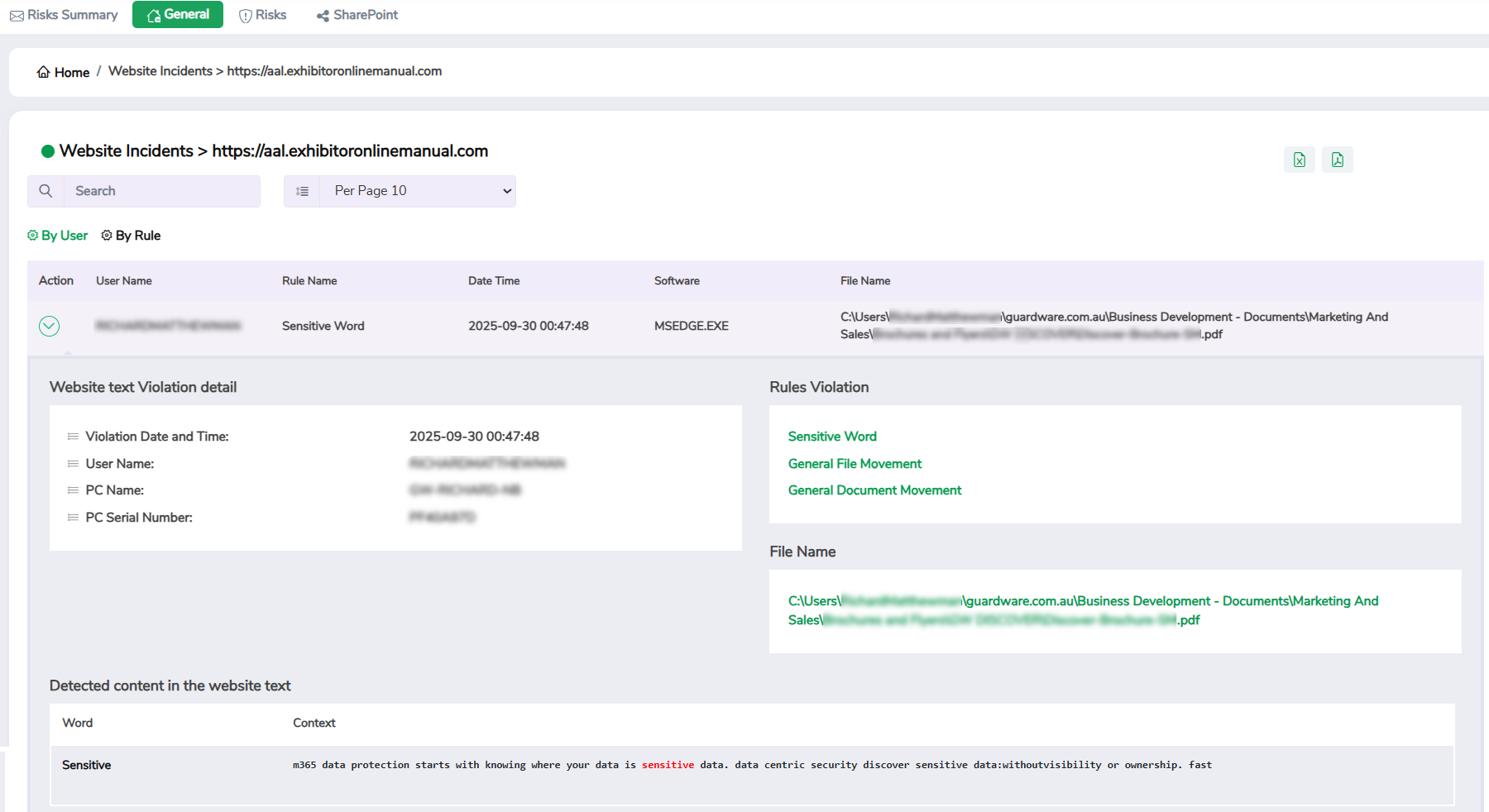
This widget shows the total number of file uploads or transfers made to corporate and non-corporate websites, such as public file-sharing services or personal cloud storage platforms, including the total number of users who initiated the upload. Clicking the widget takes you to the Uploads of Data to Non-Corporate Websites widget, where you can see more details.
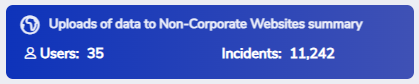
12. Uploads of Data to Non-Corporate Websites
This widget helps you detect and prevent potential data leaks by identifying websites where sensitive content was uploaded or shared. You can filter the data by URL, rule, and user.
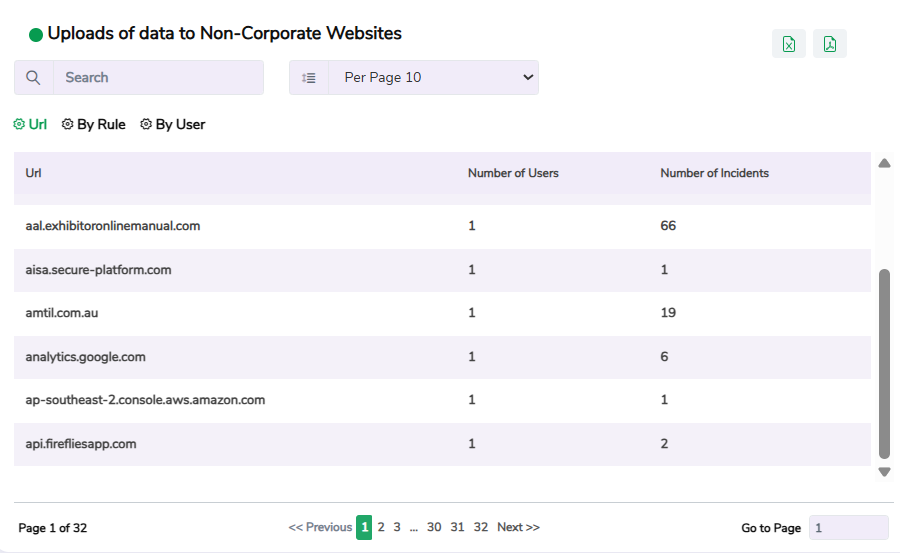
Click a specific record to view detailed information, including the username, rule name, URL, the date and time of the violation, software used, and the name and path of the file uploaded. Use the Arrow icon in the Action column to further drill down into details like detected content in the website text, PC name, and so on. Use the search box at the top to quickly filter specific information.
13. Email Attachments From Any Email Summary
This widget shows the total number of email attachments sent via both corporate and non-corporate email accounts, including the total number of users who sent the attachment. Clicking the widget takes you to the Emailing of attachments from any email address widget, where you can see more details.
14. Emailing of Attachments From Any Email Address
This widget helps you track violations involving email attachments sent from any email account, including both corporate and non-corporate. It helps you identify when sensitive files are being shared externally and track which users are sending attachments that may violate your organisation’s policies. You can filter the data by email provider, violation rule, and user.
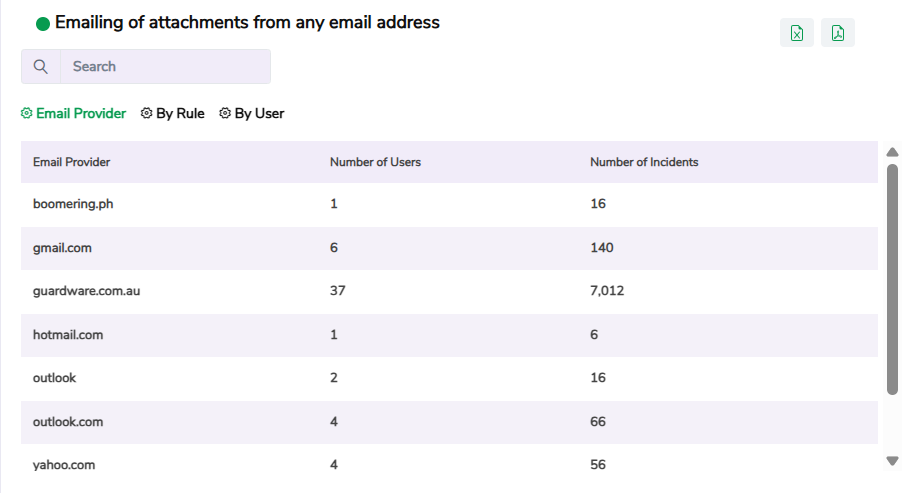
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
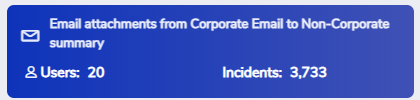
15. Email Attachments From Corporate Email to Non-Corporate Summary
This widget shows the total number of attachments sent from corporate email addresses to non-corporate domains, which are not part of your organisation’s authorised or managed domain, along with the total number of users involved. Clicking the widget takes you to the Emailing of attachments from Corporate Email Address to Non-Corporate Email Address widget, where you can see more details.
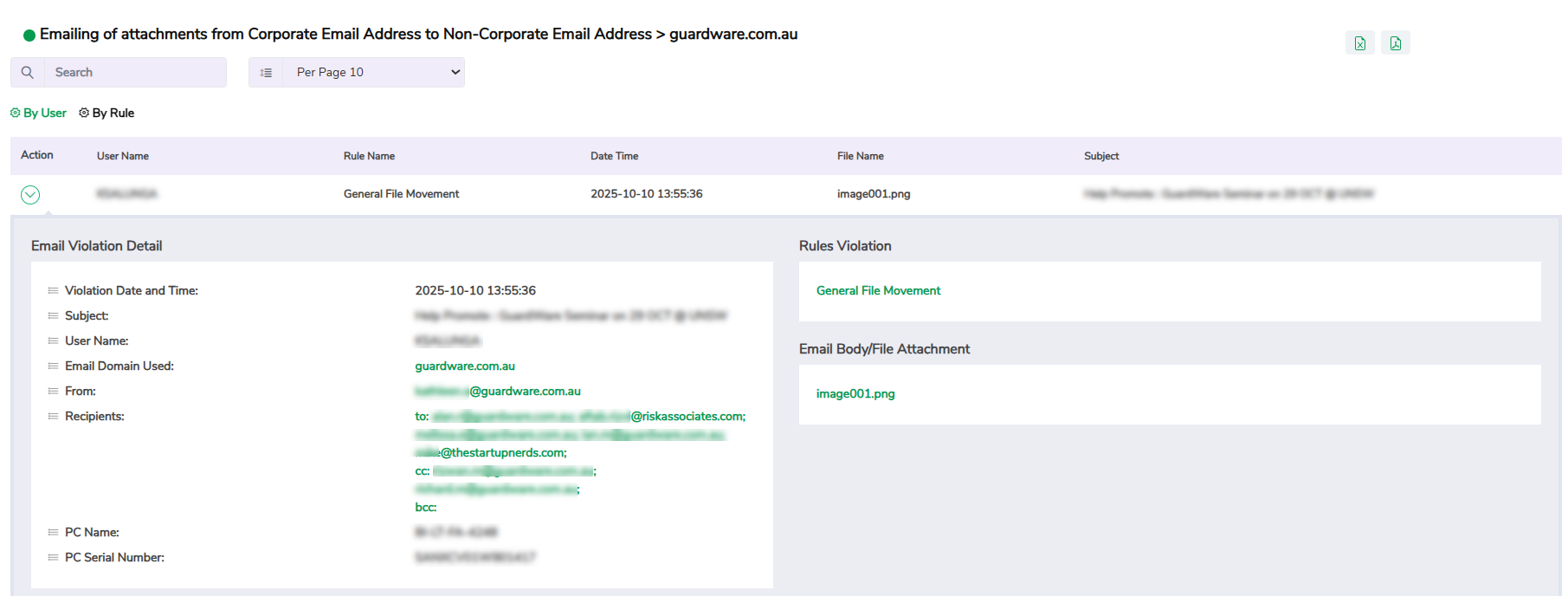
16. Emailing of Attachments from Corporate Email Address to Non-Corporate Email Address
This widget displays information about attachments sent from corporate email accounts to non-corporate domains. It helps identify external data sharing and ensure that outbound communication follows corporate data-sharing standards. You can filter the data by email provider, violation rule, and user.
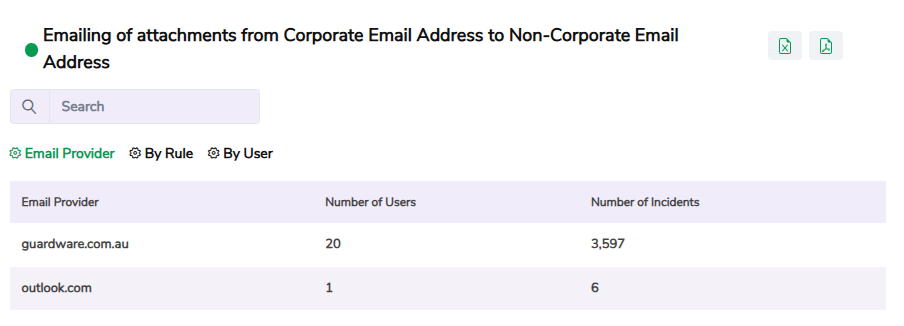
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
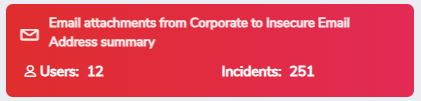
17. Email Attachments from Corporate to Insecure Email Address Summary
This widget shows the total number of attachments sent from corporate email accounts to insecure email providers that do not meet the organisation’s defined security standards, including the total number of users involved. Clicking the widget takes you to the Emailing of attachments from Corporate Email Address to Insecure Email Address widget, where you can see more details.
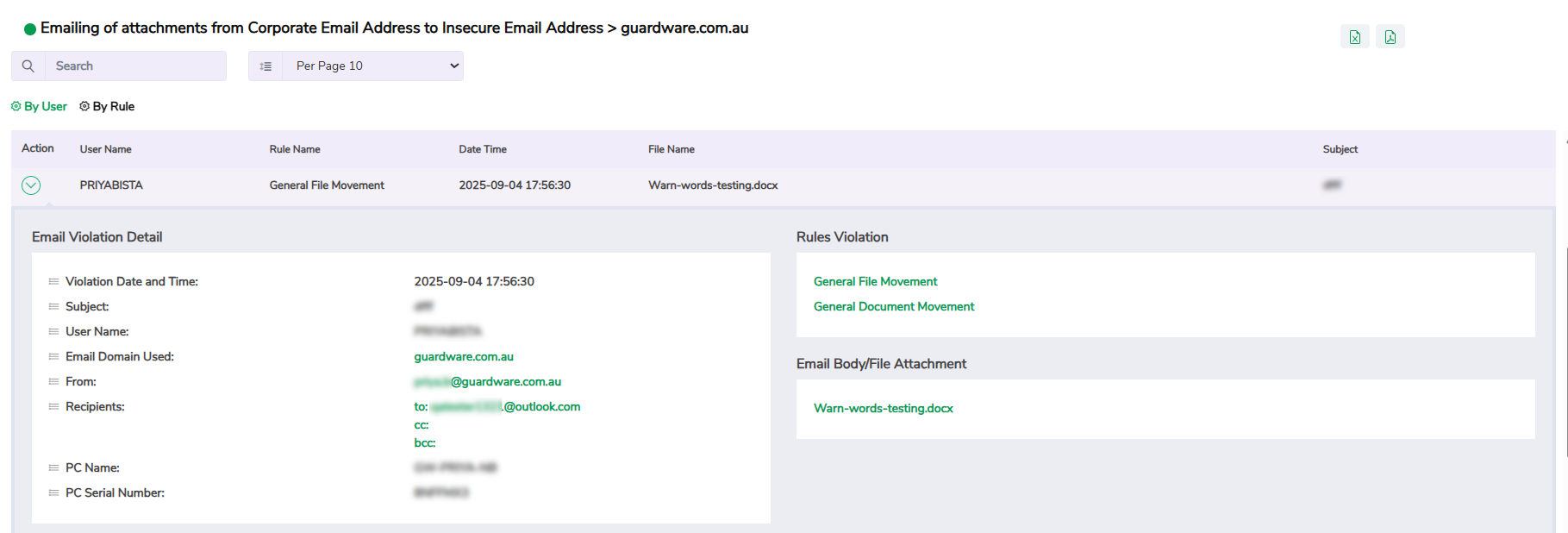
18. Emailing of Attachments from Corporate Email Address to Insecure Email Address
This widget lists incidents where attachments were sent from corporate accounts to insecure email addresses, such as lacking encryption, using outdated protocols, or failing to meet compliance requirements. It helps detect potential exposure of sensitive data to unprotected or unverified email providers. You can filter the data by email provider, violation rule, and user.
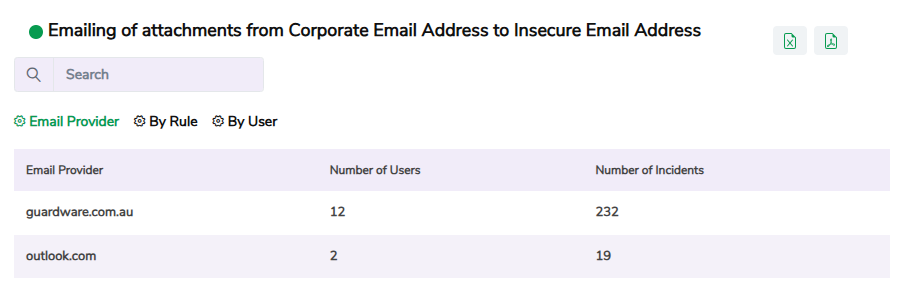
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
19. Emailing of Attachments from Non-Corporate Email Address Summary
This widget displays the number of attachments sent using non-corporate email addresses, along with the total number of users who received them. Clicking the widget takes you to the Emailing of attachments from Non-Corporate Email Address widget, where you can see more details.
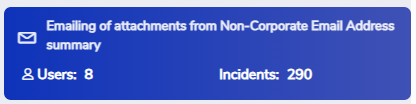
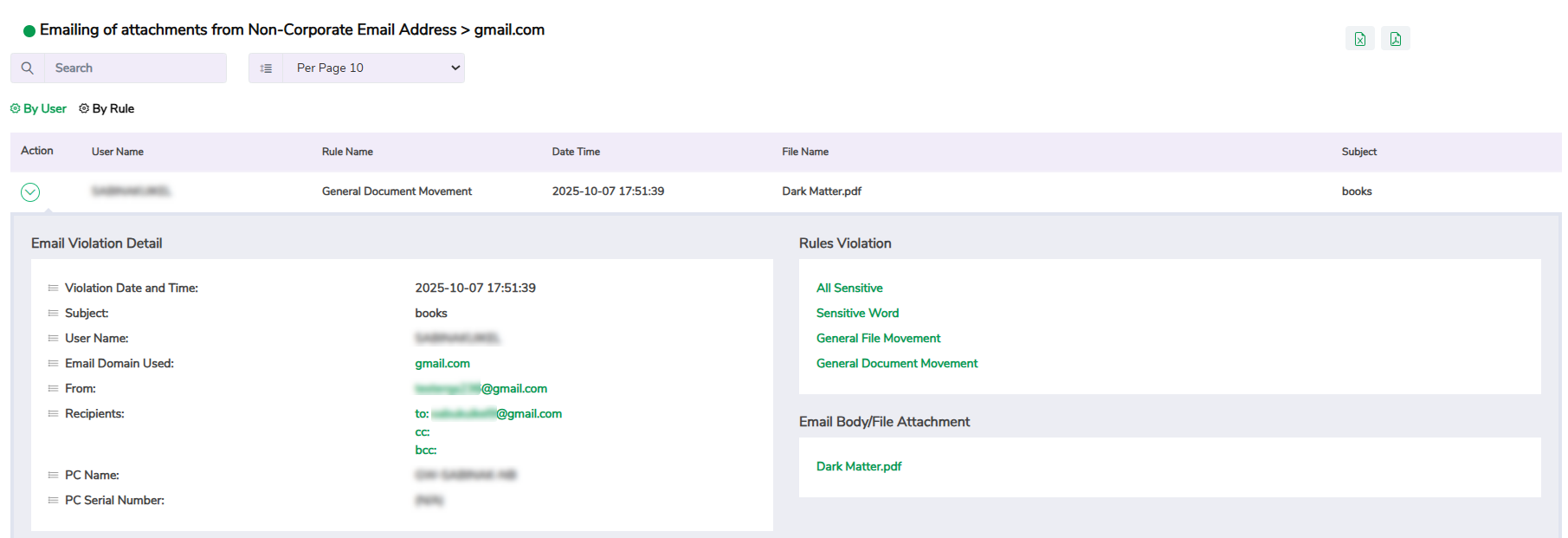
20. Emailing of Attachments from Non-Corporate Email Address
This widget displays incidents where attachments were sent from non-corporate email addresses. It helps you identify unauthorised data transfers performed through personal or unmonitored email accounts. You can filter the data by email provider, violation rule, and user.
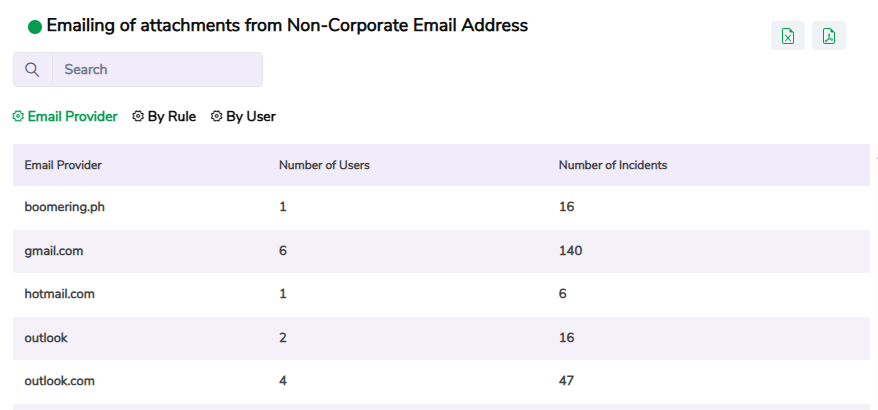
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
21. Email Attachments from Corporate Email to Personal Email Summary
This widget shows the number of attachments sent from corporate email accounts to personal addresses, including the total number of users who performed the action. Clicking the widget takes you to the Emailing of attachments from Corporate Email Address to Personal Email Address widget, where you can see more details.
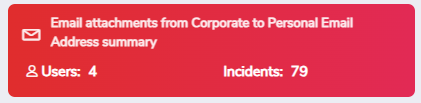
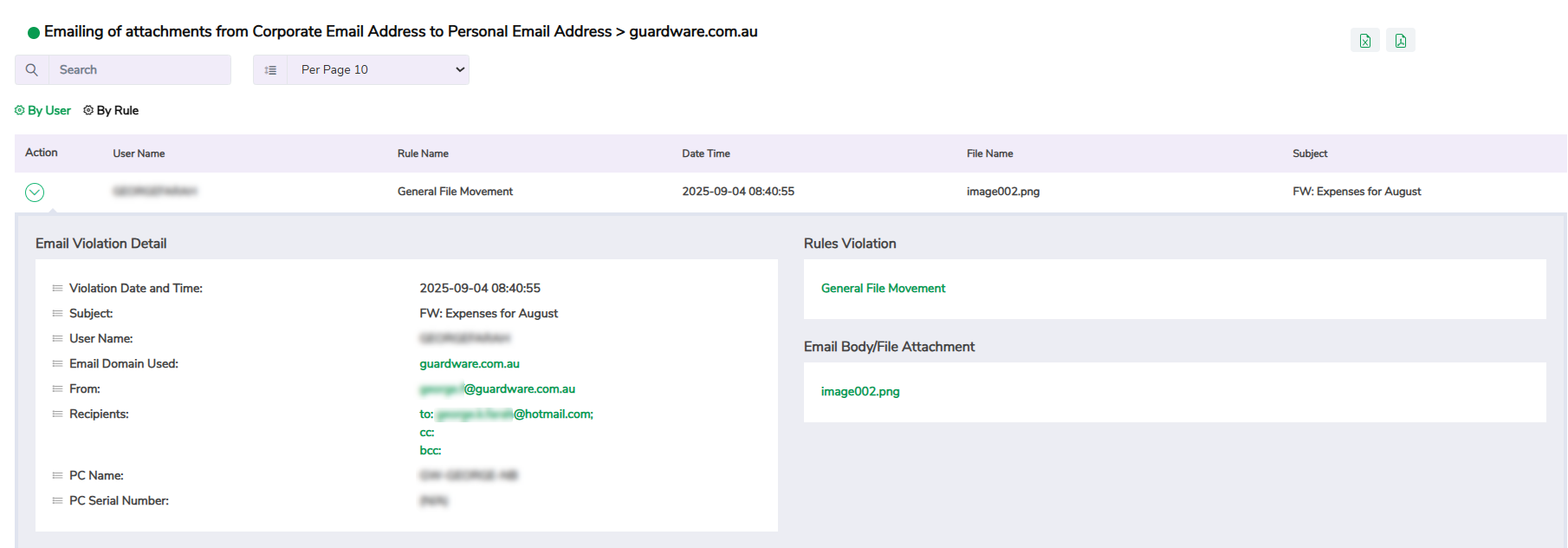
22. Emailing of Attachments from Corporate Email Address to Personal Email Address
This widget displays incidents where attachments were sent from corporate accounts to personal email addresses. It helps you identify users who transfer company data to private inboxes. You can filter the data by email provider, violation rule, and user.
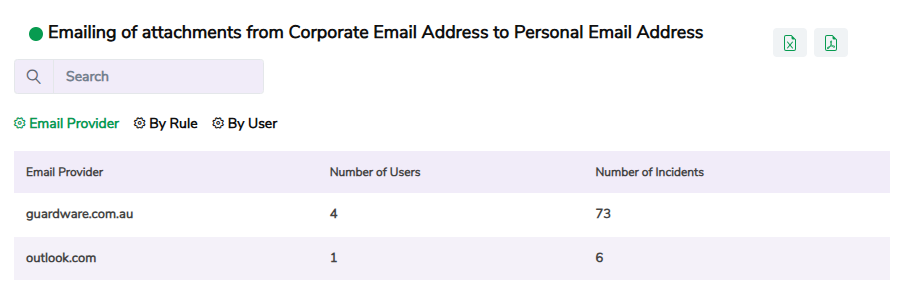
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
23. Email Attachments from Corporate Email to Potential Personal Email Summary
This widget shows the number of attachments sent from corporate email accounts to potential personal email addresses (that may belong to individual users, but are not from a recognised public email domain), including the total number of users who performed the action. Clicking the widget takes you to the Emailing of attachments from Corporate Email Address to Potential Personal Email Address widget, where you can see more details.
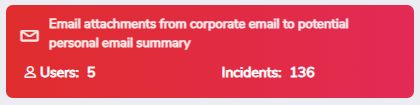
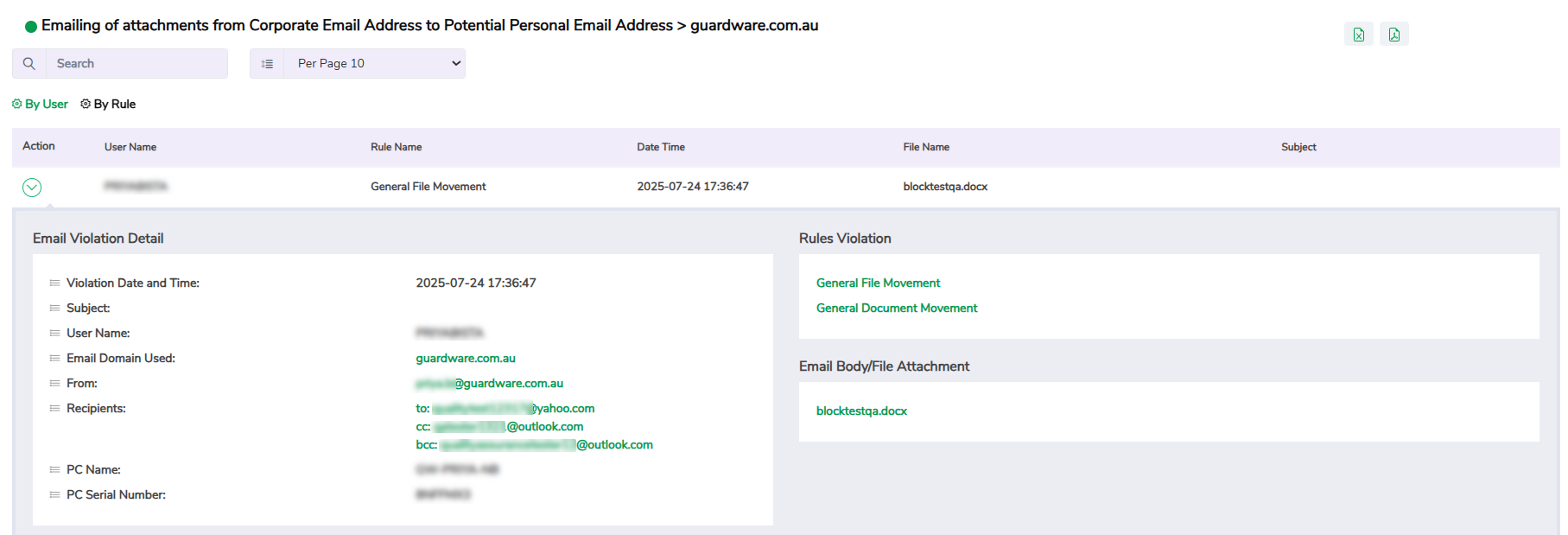
24. Emailing of attachments from Corporate Email Address to Potential Personal Email Address
This widget lists incidents of attachments sent from corporate accounts to potential personal email accounts. It helps you flag suspicious email activity for review. You can filter the data by email provider, violation rule, and user.
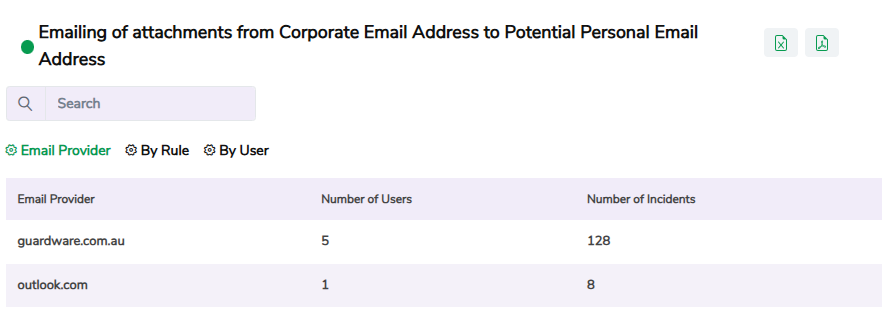
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
25. Email Attachments from Corporate Email to Own Corporate Email Summary
This widget tracks emails where users sent attachments from their corporate email accounts to their own corporate addresses, including the number of users who did so. Clicking the widget takes you to the Emailing of attachments from Corporate Email to Own Corporate Email Address widget, where you can see more details.
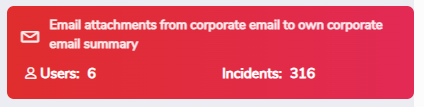
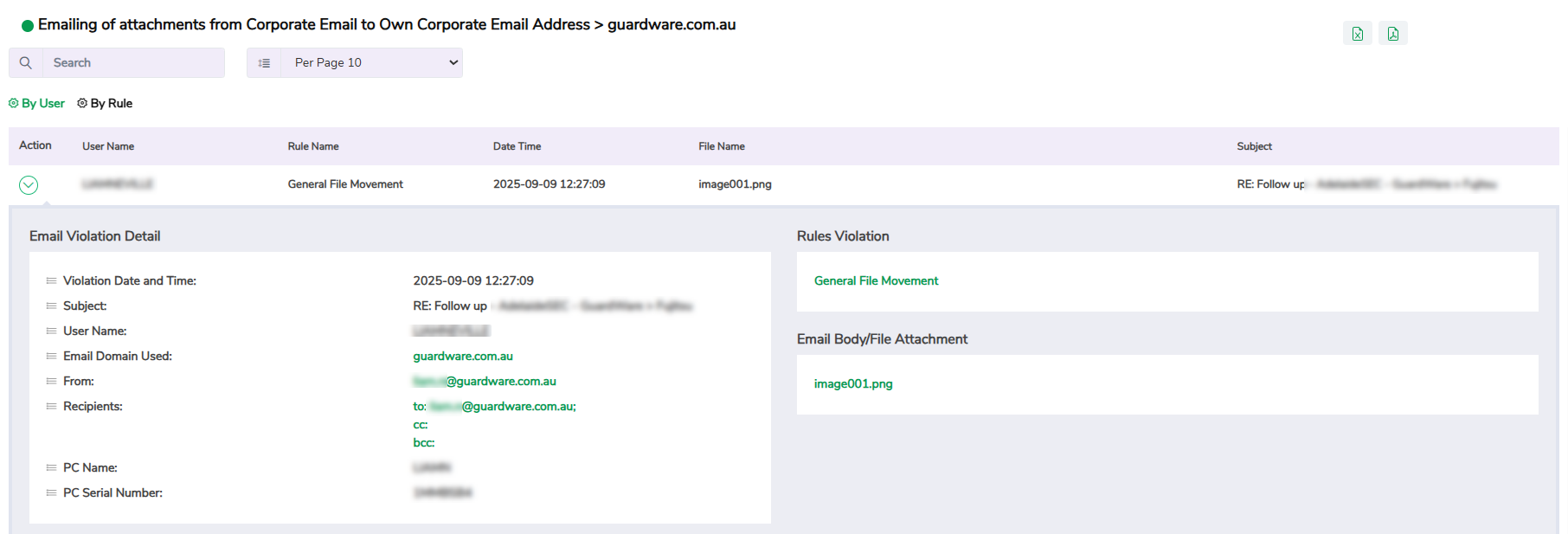
26. Emailing of attachments from Corporate Email to Own Corporate Email Address
This widget displays self-emailing incidents where users sent attachments to their own corporate accounts. It helps monitor self-transfers that may indicate attempts to bypass data-handling policies or duplicate sensitive files. You can filter the data by email provider, violation rule, and user.
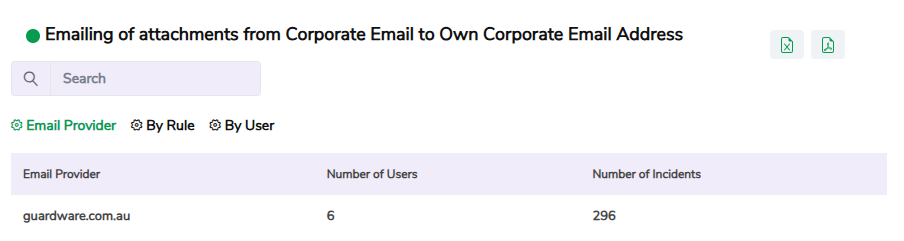
Click a specific record to view detailed information, including the email provider, username, rule name, the date and time of the violation, the name of the file that was shared, and the email subject. Use the Arrow icon in the Action column to further drill down into details like sender and receiver’s email address, and so on. Use the search box at the top to quickly filter specific information.
27. Application Control
This widget provides visibility into application (for example, browsers, work-related, and non-work applications) usage across your organisation. It shows which users accessed which applications and how much time they spent using them. It helps you enforce application usage policies, detect unapproved tools, and maintain compliance with security guidelines.
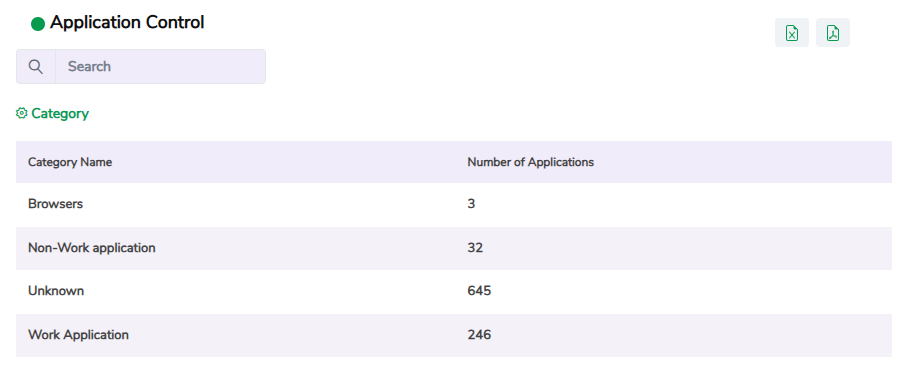
Click a specific record to view detailed information, including the application name, description, number of users, time spent on the application, and vendor name.
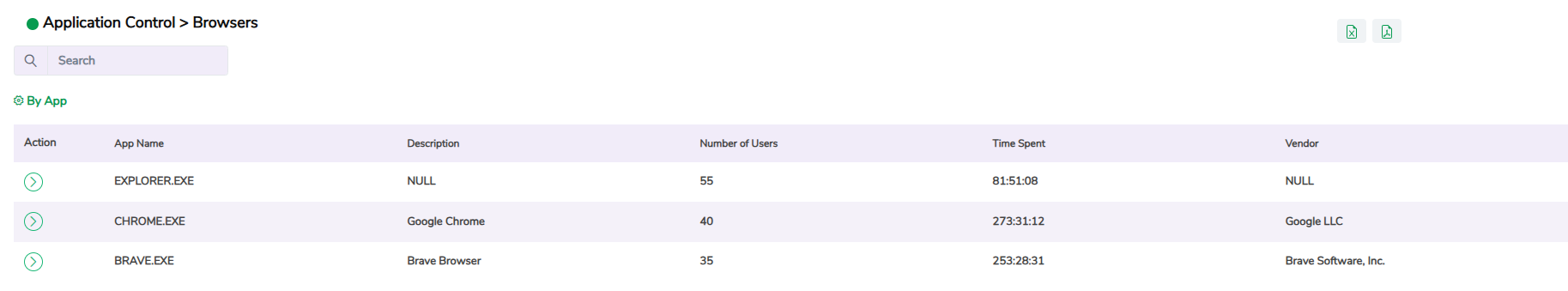
Use the Arrow icon in the Action column to further drill down into details like PC name, user name, date, and time. Use the search box at the top to quickly filter specific information.

SharePoint Dashboard
The SharePoint Dashboard provides detailed visibility into file access, sharing, and download activities within your organisation’s SharePoint environment. It consolidates user interactions, link-sharing patterns, and platform-based access data to help administrators monitor collaboration, detect unusual behaviour, and ensure secure handling of sensitive corporate information.
Unlike other dashboards that focus on general system activity or user risk, the SharePoint Dashboard specifically analyses SharePoint-related data usage, giving insights into how files are accessed internally and externally, how sharing links are created, and which devices or platforms are used to view or download content.
This dashboard is especially useful for security administrators and compliance teams who need to audit SharePoint access, track file exposure through anonymous or external links, and ensure that data stored in SharePoint sites is being accessed according to organisational policy.
You can access the SharePoint Dashboard from the Dashboard section in the GuardWare INSIGHT Management Console.
Widgets in SharePoint Dashboard
Category
Widget Name
File and User Activity
Library Activity
Link and Access Management
Downloads and Access by Platform
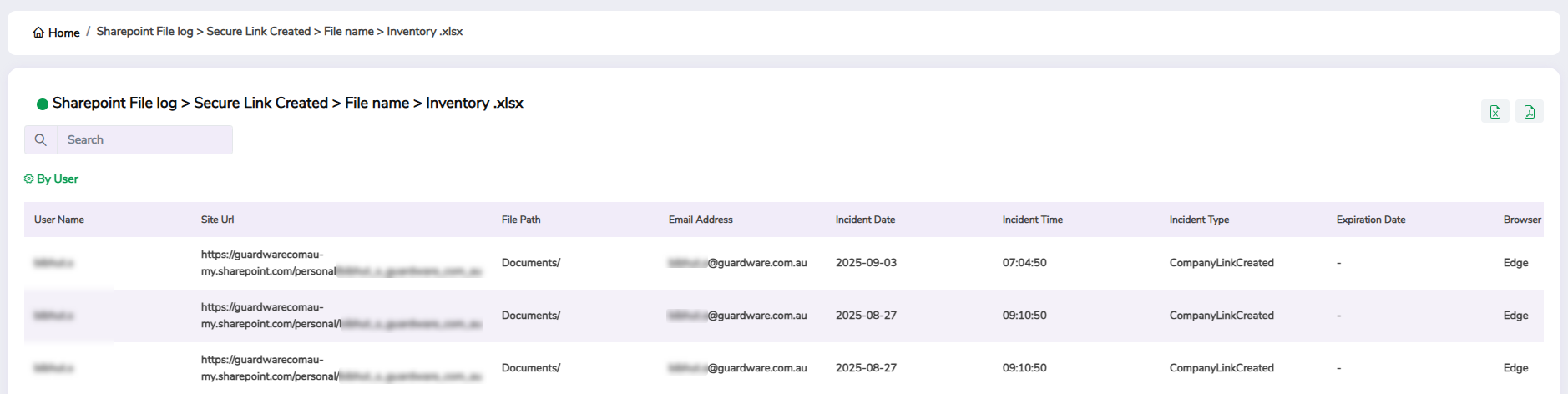
1. SharePoint File Access and Download Logs by File Name or by Platform
This widget displays detailed logs of file access and download activity for SharePoint files. It provides visibility into how and where files are being used across your organisation’s SharePoint environment, helping you track external collaboration and detect potential unauthorised sharing through anonymous or external access links. You can filter the data by filename, platform name, and IP address.
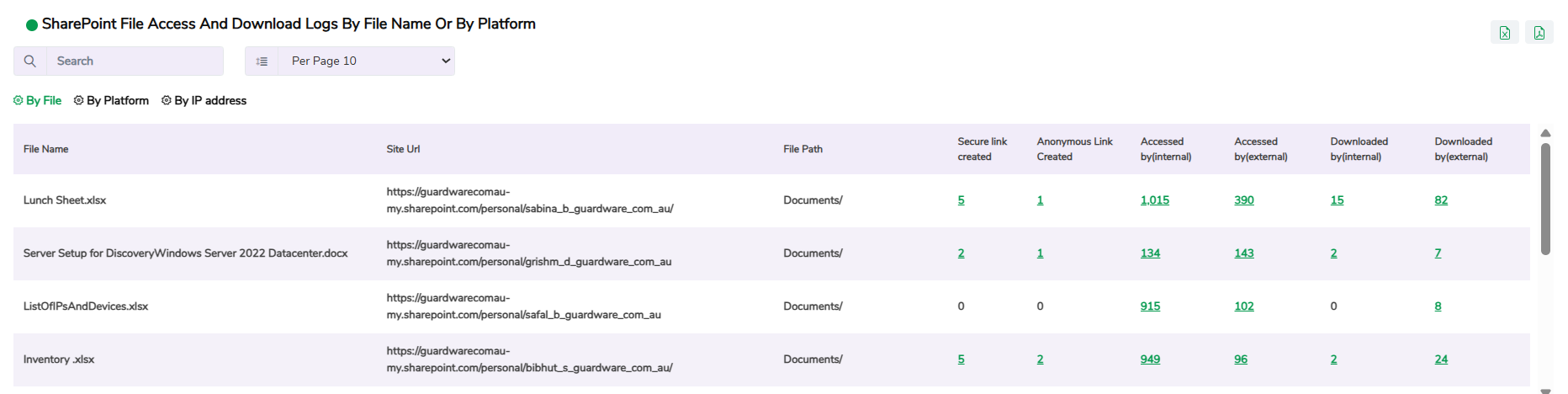
For each file, the widget shows:
Secure Links Created: Number of secure or organisation-approved sharing links created.
Anonymous Links Created: Number of public or unrestricted sharing links generated.
Accessed by (Internal/External): Number of times files were accessed by internal or external users.
Downloaded by (Internal/External): Number of times files were downloaded within or outside the organisation.
Click a specific record to view detailed information, including the user who accessed or shared the file, file path, incident date and time, browser name, and so on.
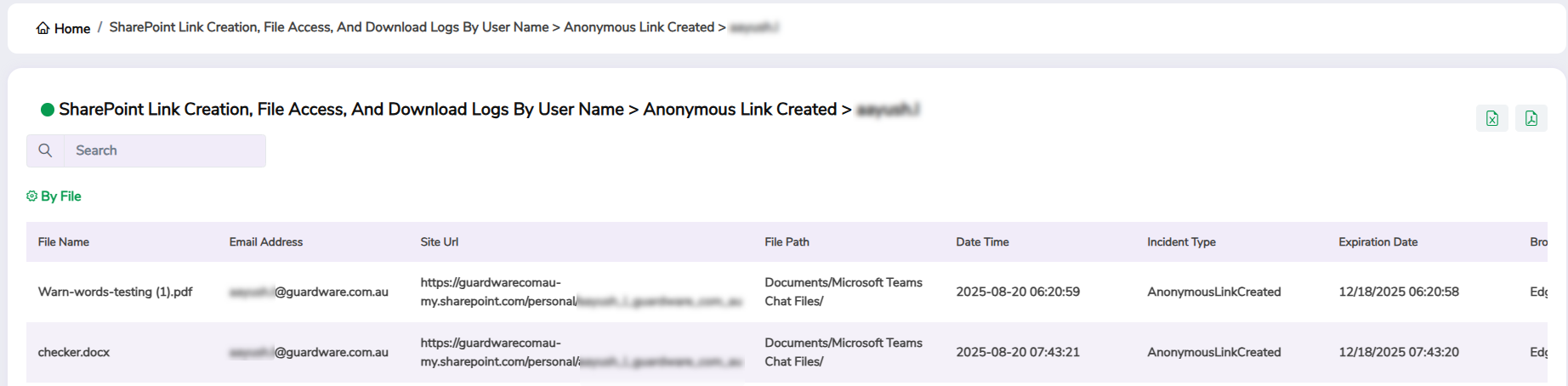
2. SharePoint Link Creation, File Access, and Download Logs by User Name
This widget provides a user-level view of SharePoint link creation, file access, and download activity. It displays each user’s total number of links created and files accessed or downloaded, helping you identify who is sharing, accessing, or exporting SharePoint content. This widget helps detect excessive or unusual file-sharing activity, monitor external collaboration, and ensure that all file access and sharing actions comply with organisational data-security policies.
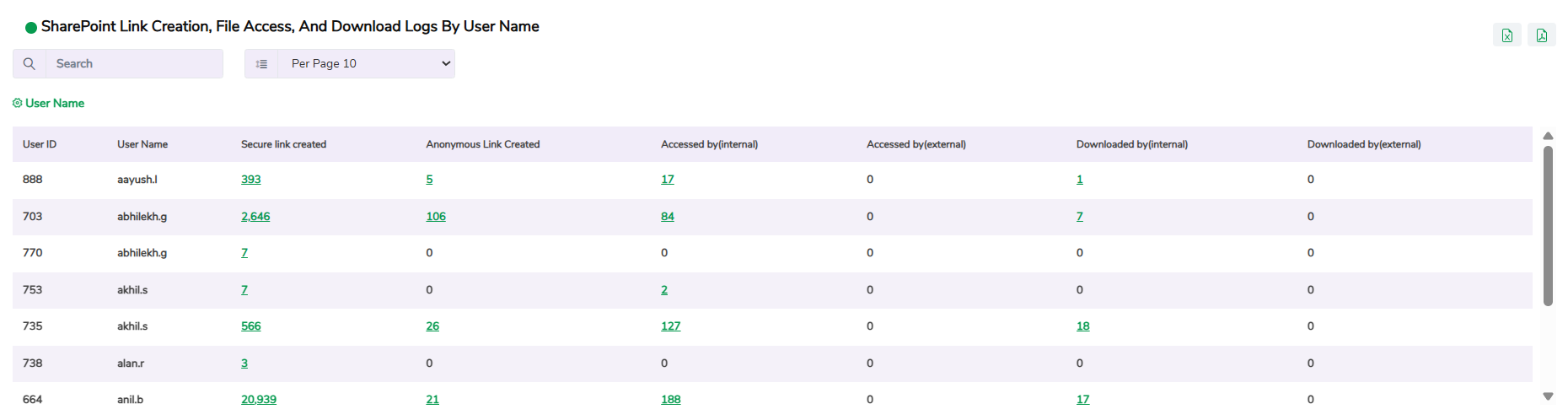
For each user, the widget shows key details such as:
Secure Links Created: Number of secure or organisation-approved sharing links created.
Anonymous Links Created: Number of public or unrestricted sharing links generated.
Accessed by (Internal/External): Number of times files were accessed by internal or external users.
Downloaded by (Internal/External): Number of times files were downloaded within or outside the organisation.
Click a specific record to view detailed information, including the user’s email address, file name, file path, URL, incident date and time, browser name, and so on.
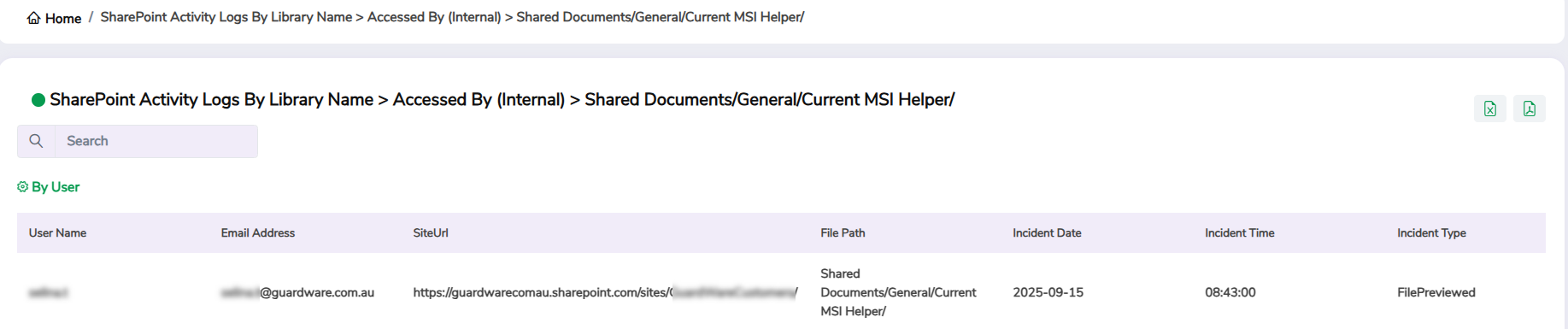
3. SharePoint Activity Logs by Library Name
This widget displays activity logs for SharePoint libraries, showing file access, sharing, and download activity within each document library. It helps you track how data is being used within different libraries and identify which files or folders are being accessed most frequently, and detect unusual access patterns.
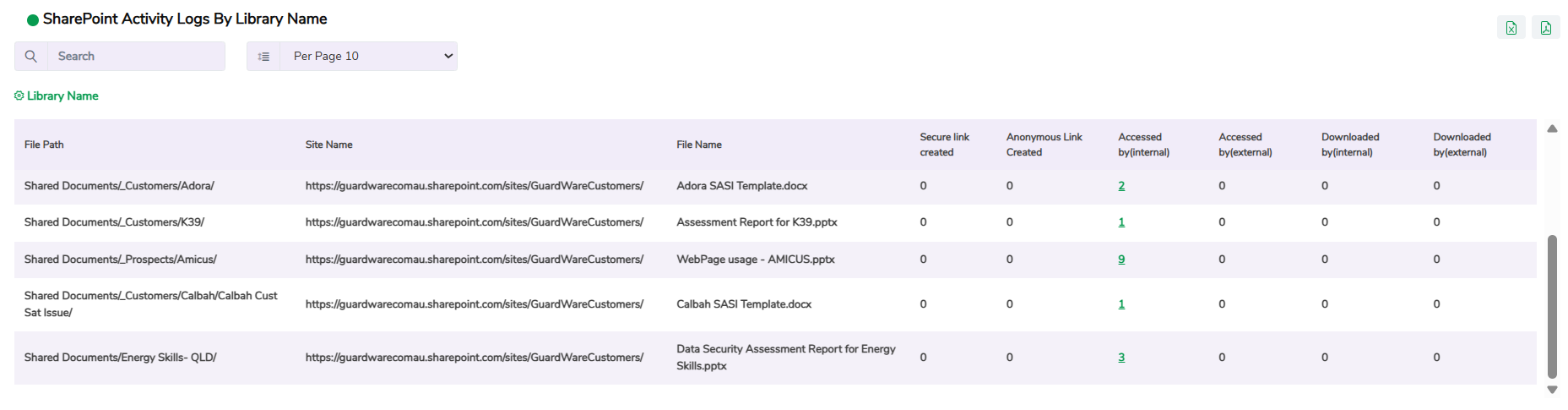
For each library, the widget lists details such as:
File Path and Site Name: Location of the library and the associated SharePoint site.
File Name: Name of the file stored in that library.
Secure Links Created / Anonymous Links Created: Number of secure or public links generated for files within the library.
Accessed by (Internal/External): Number of times files were accessed by internal staff or external users.
Downloaded by (Internal/External): Number of times files were downloaded inside or outside the organisation.
Click a specific record to view detailed information, including the user who accessed the file, file name, file path, URL, incident date and time, browser name, and so on.
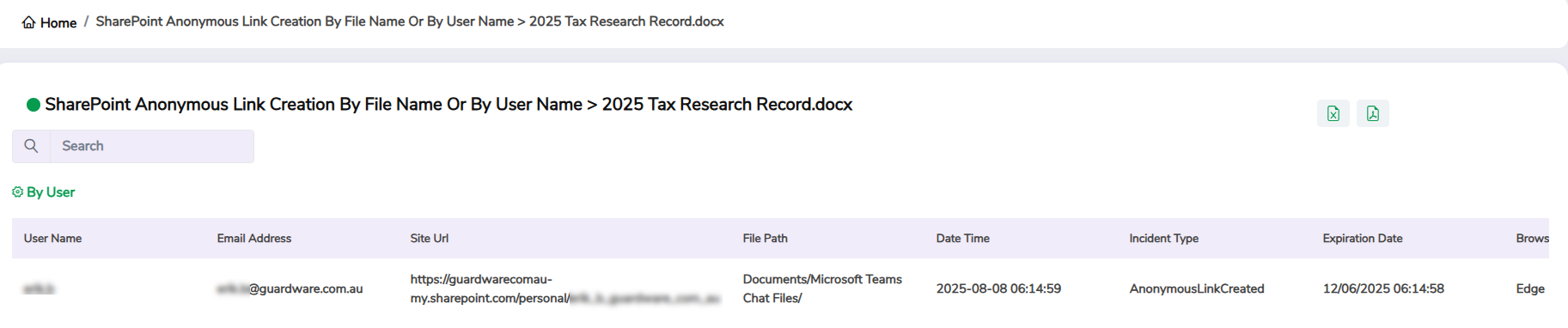
4. SharePoint Anonymous Link Creation by File Name or by User Name
This widget displays details of anonymous link creation activity within SharePoint. It helps you identify when files are shared publicly through links that allow access without authentication. This widget is crucial for monitoring data exposure risks, as anonymous links bypass user identity verification and can be forwarded to unauthorised recipients. By tracking which files and users are involved, you can review, revoke, or restrict public sharing and enforce secure link policies. You can filter the data by file name or user name.
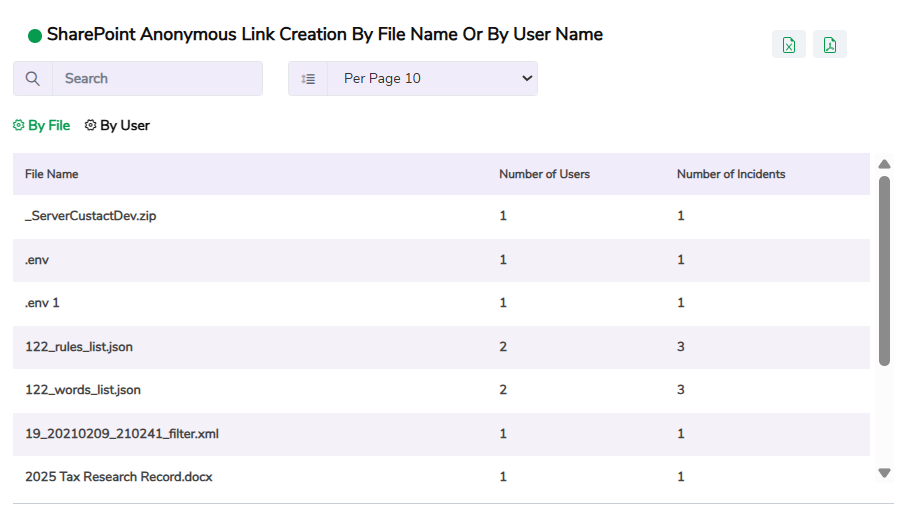
For each file or user, the widget shows:
Number of Users: How many users created anonymous links for the listed files.
Number of Incidents: How many times anonymous links were generated for the same file or by the same user.
Click a specific record to view detailed information, including the user who created the link, file name, file path, URL, incident date and time, browser name, and so on.
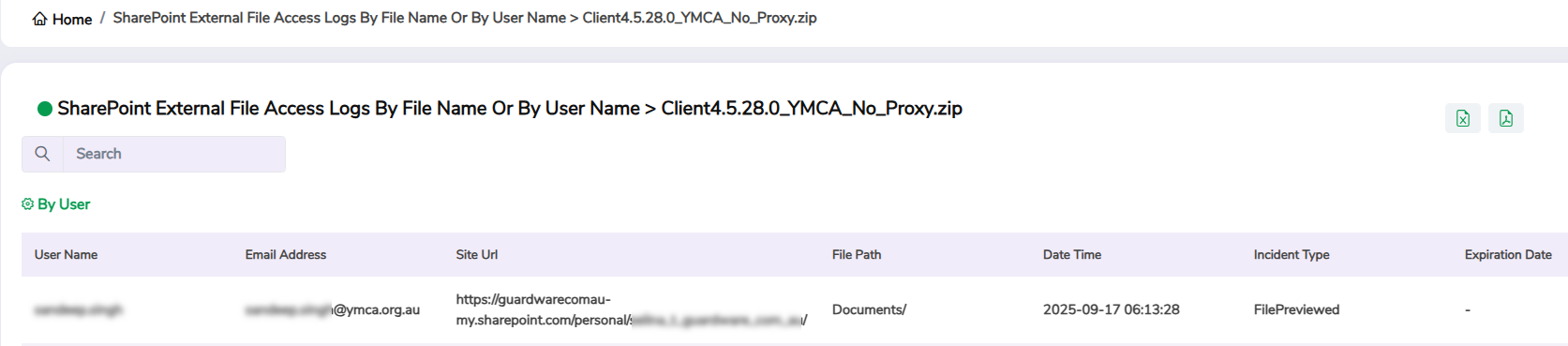
5. SharePoint External File Access Logs by File Name or by User Name
This widget provides visibility into external access activity for SharePoint files. It helps you track when and how files stored in SharePoint are being accessed by users outside the organisation’s domain. This widget is essential for identifying data exposure risks through external collaboration or sharing. By reviewing external access patterns, you can verify whether file-sharing aligns with business requirements and take action to revoke access or strengthen permissions when needed. You can filter the data by file name or user name.
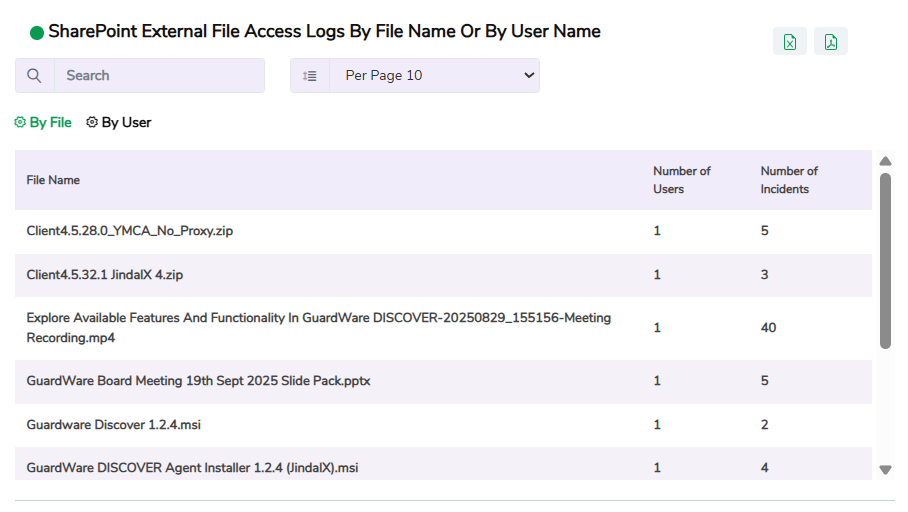
For each file or user, the widget includes:
Number of Users: Total external users who accessed the file.
Number of Incidents: Total number of times the file was accessed externally.
Click a specific record to view detailed information, including the user who accessed the file, file name, file path, URL, incident date and time, browser name, and so on.
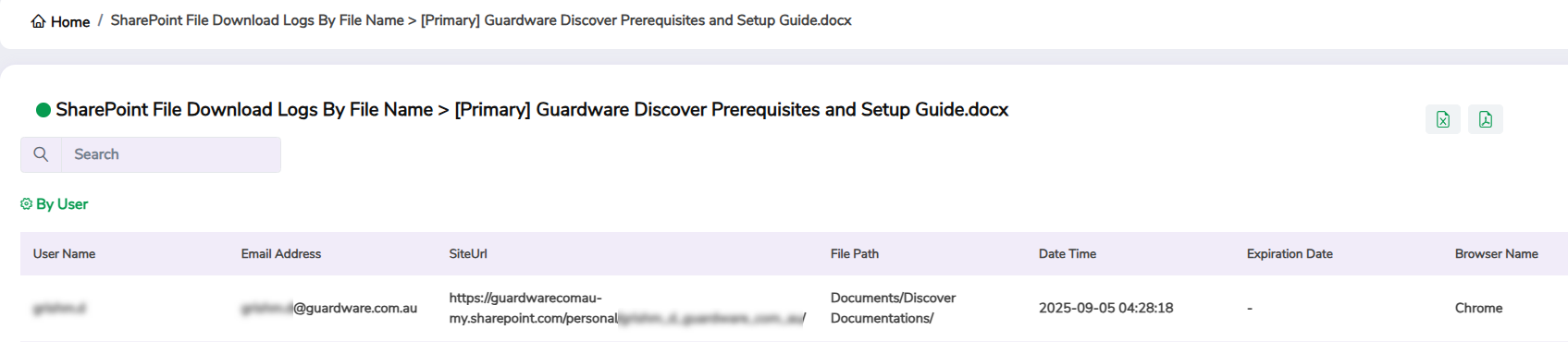
6. SharePoint File Download Logs by File Name
This widget displays detailed logs of file download activity within SharePoint. It helps you track which files are being downloaded, by whom, and how often, helping ensure that downloads comply with organisational data handling policies. You can filter the data by internal or external users.
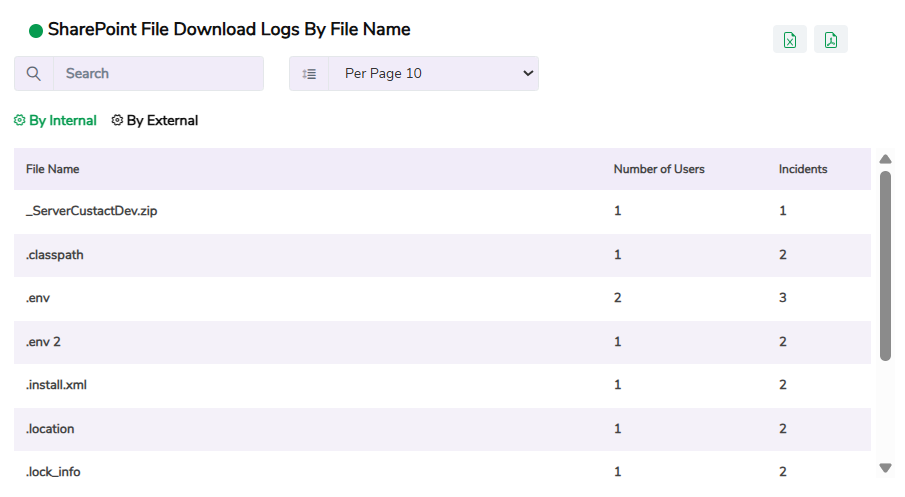
For each file, the widget shows:
Number of Users: Total users who downloaded the file.
Incidents: Total number of download actions recorded for that file.
Click a specific record to view detailed information, including the user who downloaded the file, file name, file path, URL, incident date and time, browser name, and so on.
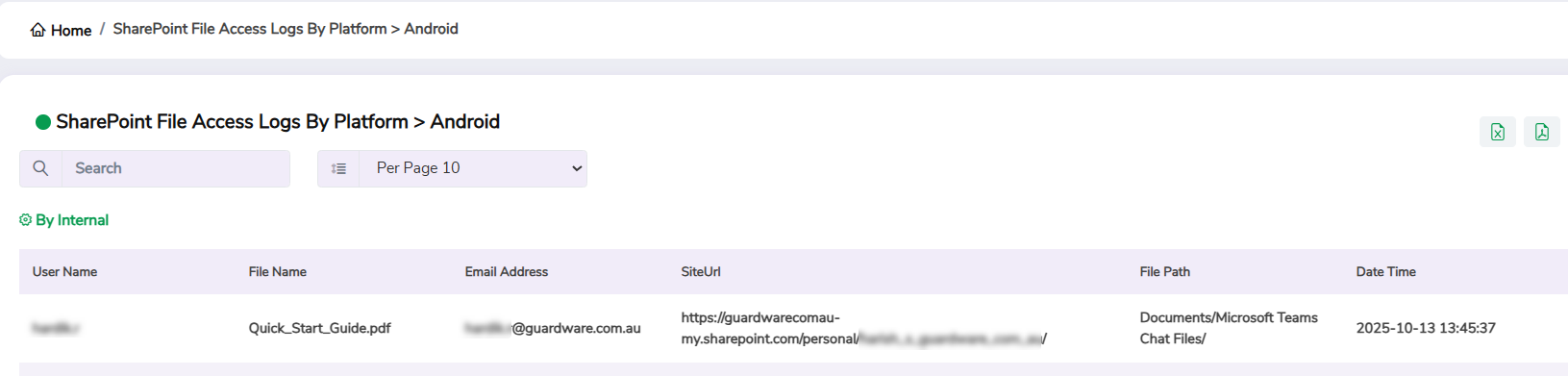
7. SharePoint File Access Logs by Platform
This widget displays detailed records of SharePoint file access activity, categorised by platform or device type. It provides visibility into which operating systems and applications are being used to access SharePoint files, helping you detect unusual access from unauthorised devices, such as personal mobile phones or unregistered systems. You can filter the data by internal or external users.
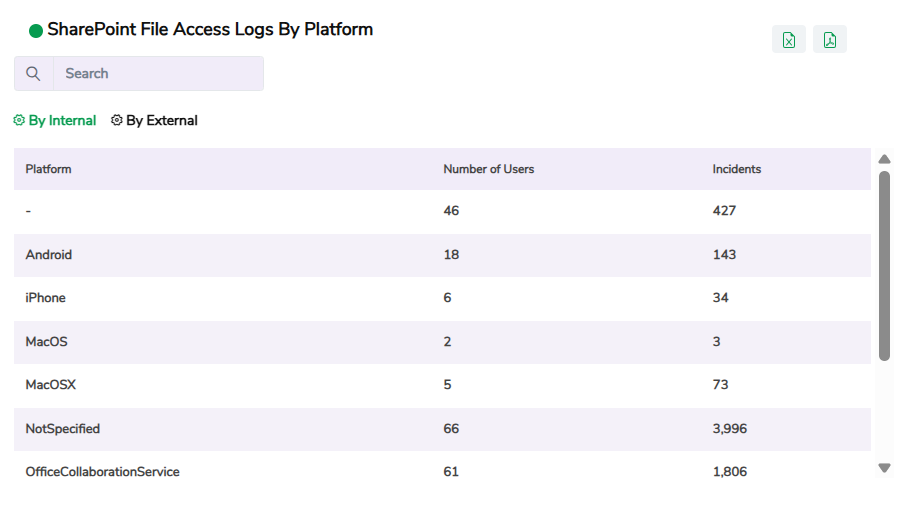
For each platform, the widget shows:
Number of Users: Total users who accessed files using that platform.
Incidents: Total number of access events recorded for that platform.
Click a specific record to view detailed information, including the user who accessed the file, file name, file path, URL, incident date and time, browser name, and so on.
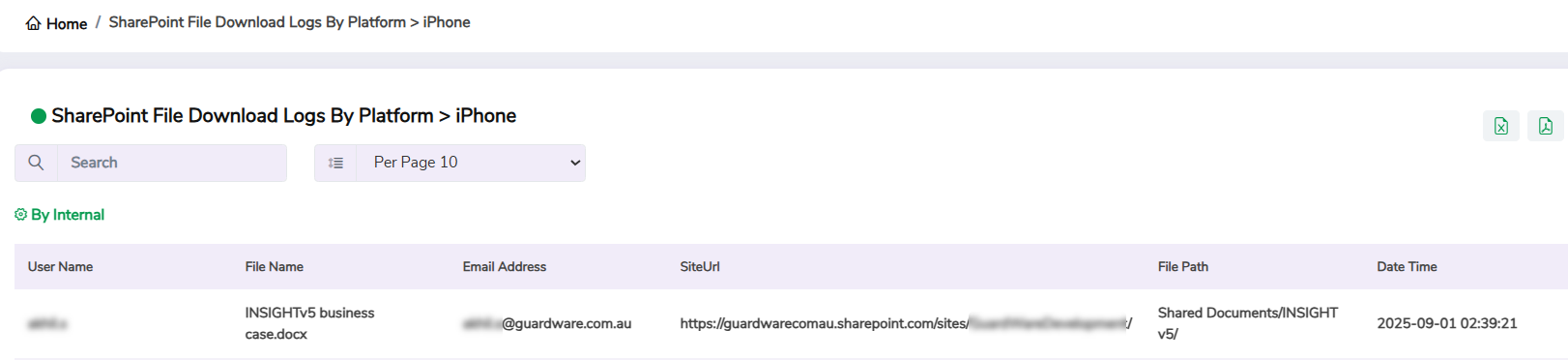
8. SharePoint File Download Logs by Platform
This widget shows detailed information on SharePoint file download activity, categorised by platform or device type. It helps you identify which devices and operating systems are being used to download files, offering insights into unusual download patterns, such as large file transfers from unverified devices or unapproved operating systems. You can filter the data by internal or external users.
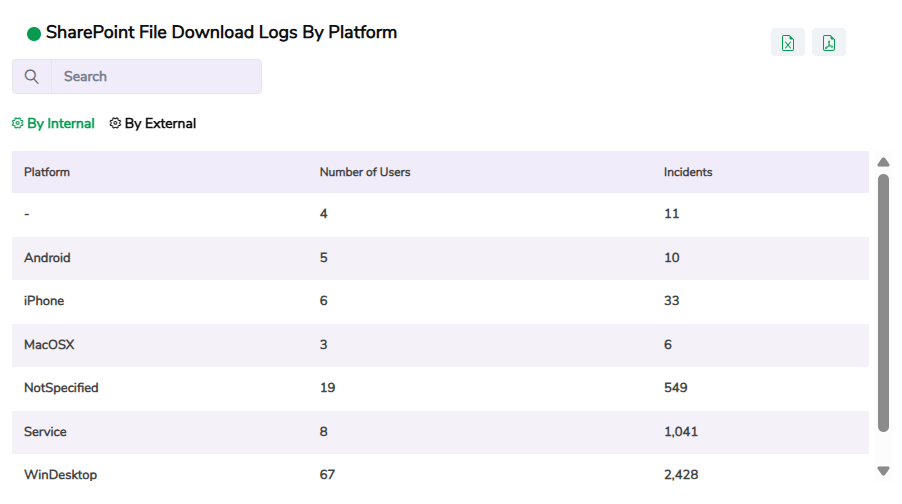
For each platform, the widget displays:
Number of Users: Total users who downloaded files using that platform.
Incidents: Total number of download actions recorded for that platform.
Click a specific record to view detailed information, including the user who downloaded the file, file name, file path, URL, incident date and time, browser name, and so on.
AI Usage Dashboard
The AI Usage Dashboard provides visibility into how users interact with AI tools across both applications and web platforms. It helps organisations detect file uploads, sensitive prompts, and overall time spent on AI systems such as ChatGPT, Claude, Gemini, DeepSeek, Perplexity, and other emerging AI assistants. This dashboard is particularly useful for monitoring data-loss risks, ensuring compliance with AI usage policies, and assessing the business impact of AI adoption in the workplace.
You can access the AI Usage Dashboard from the Dashboard section in the GuardWare INSIGHT Management Console.

Widgets in AI Usage Dashboard
Category
Widget Name
System Activity
AI Website Usage
AI Application Usage
AI Website Uploads
AI Application Uploads
Sensitive Prompt Monitoring
1. PCs Online
This widget shows the total number of PCs that are online or offline during the selected time period. It helps you monitor endpoint availability and determine which systems are active or inactive across the network.

Click the widget to view detailed information, including the PC name, PC group, username, and last online time. Use the Online and Offline tabs to switch between active and inactive PCs, and use the search box at the top to quickly filter specific results.

2. Users Online
This widget displays the total number of users who are online or offline within the selected time period. It helps you track user activity levels and session availability.

Click the widget to view detailed information, including the username, user group, PC name, and last online time. Use the Online and Offline tabs to switch between active and inactive users, and use the search box at the top to quickly filter specific results.

3. Time Spent on Generative AI Website Summary
This widget displays how much total time users spent on web-based Generative AI platforms, such as ChatGPT, Claude, Gemini, DeepSeek, and so on. It shows the number of users using AI websites and the total browsing duration. You can use it to monitor engagement levels with AI tools, detect excessive usage, and evaluate whether users are relying on external AI systems for work-related tasks. Clicking the widget takes you to the Time Spent on Generative AI Website widget, where you can see more details.

4. Time Spent on Generative AI Website
This widget displays time spent per AI website or domain, listing the number of users and the total time for each platform. It provides visibility into how long employees interact with AI services such as ChatGPT, Claude, Gemini, DeepSeek, and so on. This widget helps you understand the scale of AI tool usage and detect patterns that may indicate policy breaches or overuse of external AI resources.

Click a specific record to view detailed information, including the username, total time spent by each user on the website, and the date when users accessed the site. Use the search box at the top to quickly filter specific information.

5. Time Spent on Generative AI Application Summary
This widget displays the total time users spend using Generative AI applications installed on their devices, such as CHATGPT.EXE or other desktop-based AI tools. It helps identify how much time employees are actively engaging with AI software that may handle sensitive or corporate data. You can use this information to assess productivity impact, detect unauthorised AI tool usage, and ensure compliance with organisational policies. Clicking the widget takes you to the Time Spent on Generative AI Application widget, where you can see more details.

6. Time Spent on Generative AI Application
This widget displays how much time users spend using installed Generative AI applications on their devices, such as the desktop version of ChatGPT (e.g. CHATGPT.EXE). It shows the number of users who accessed the application and the total time spent, helping you understand how frequently AI tools are being used within the organisation. This information is useful for identifying productivity impact, monitoring adoption of AI tools, and enforcing internal policies around authorised and unauthorised software usage.

Click a specific record to view detailed information, including the username, total time spent by each user on the application, and the date when users accessed the application. Use the search box at the top to quickly filter specific information.

7. Files Uploaded to Generative AI Website Summary
This widget tracks files uploaded to AI-powered web platforms, such as ChatGPT, Claude, Gemini, Perplexity, and so on. It displays the number of users involved and the total upload incidents recorded. Monitoring this widget helps you detect instances where sensitive information may have been shared with online AI systems, which could pose privacy or confidentiality risks. Clicking the widget takes you to the Files Uploaded to Generative AI Website widget, where you can see more details.

8. Files Uploaded to Generative AI Website
This widget lists all URLs of Generative AI websites, such as ChatGPT, Claude, Gemini, DeepSeek, and so on, where users uploaded files, along with the number of users and total incidents for each platform. This view helps you pinpoint which specific platforms are most frequently used for file uploads, supporting targeted awareness or restriction policies.

Click a specific record to view detailed information, including the username, violated rule name, date and time of violation, software used to access and upload to the website, and name of the uploaded file.

Use the Arrow icon in the Action column to further drill down into details like detected content in the uploaded file, PC name, and so on. Use the search box at the top to quickly filter specific information.

9. Files Uploaded to Generative AI Application Summary
This widget helps you monitor when files are uploaded to Generative AI applications, such as desktop versions of AI assistants (e.g. CHATGPT.EXE). It shows the total number of users who performed uploads and the total incidents recorded during the selected period. It’s useful for detecting potential data-loss events when corporate files are shared through locally installed AI tools rather than approved platforms. Clicking the widget takes you to the Files Uploaded to Generative AI Application widget, where you can see more details.

10. Files Uploaded to Generative AI Application
This widget shows how many users uploaded files directly into installed Generative AI applications, such as desktop-based AI tools (e.g. CHATGPT.EXE), and the total number of upload incidents. It helps you detect when corporate documents, reports, or other sensitive files are shared through local AI software instead of approved channels. This is useful for preventing data leakage through unmanaged or offline AI applications that bypass browser-based monitoring.

Click a specific record to view detailed information, including the username, violated rule name, date and time of violation, and name of the uploaded file.

Use the Arrow icon in the Action column to further drill down into details like detected content in the uploaded file, PC name, PC Serial number and so on. Use the search box at the top to quickly filter specific information.

11. Sensitive Prompts Used in AI Website Summary
This widget highlights users who have entered sensitive or policy-violating prompts into AI websites such as ChatGPT, Grok, or Perplexity. It shows the number of users and incidents where monitored or restricted phrases were detected. It helps detect attempts to share confidential content or company-specific information through AI prompts, supporting proactive compliance monitoring. Clicking the widget takes you to the Sensitive Prompts Used in AI Website widget, where you can see more details.

12. Sensitive Prompts Used in AI Website
This widget lists URLs, users, and incident counts where sensitive prompts were entered into AI websites. It helps administrators identify which AI platforms are most frequently used for potentially risky queries or data sharing. It helps you review prompt-level violations, validate DLP detections, and take corrective actions such as user training or access restrictions.

Click a specific record to view detailed information, including the username, violated rule name and date and time of violation.

Use the Arrow icon in the Action column to further drill down into details like detected content in the website text, PC name, and so on. Use the search box at the top to quickly filter specific information.

Custom Dashboards
You can create your own dashboards to view the data and activities that matter most to you. You can choose the widgets you want to include and apply filters to focus on specific users, time periods, or activities. Creating a custom dashboard helps you monitor key metrics, track usage trends, and quickly access insights relevant to your role, all in one place.
Create Custom Dashboards
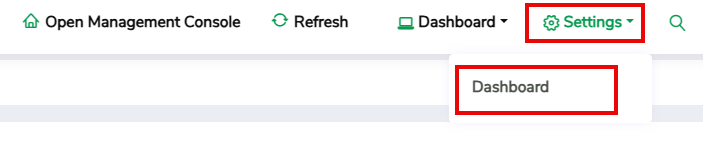
Navigate to Settings > Dashboard.
Click +Add New.
Enter the Dashboard Name and Description. Use a clear, descriptive name that reflects the dashboard’s purpose.
Select the Duration for which you want the data to be displayed (for example, Day, Week, Month, Quarter).
Select Set as Default if you want this dashboard to be your default and appear first when you open the Dashboard.
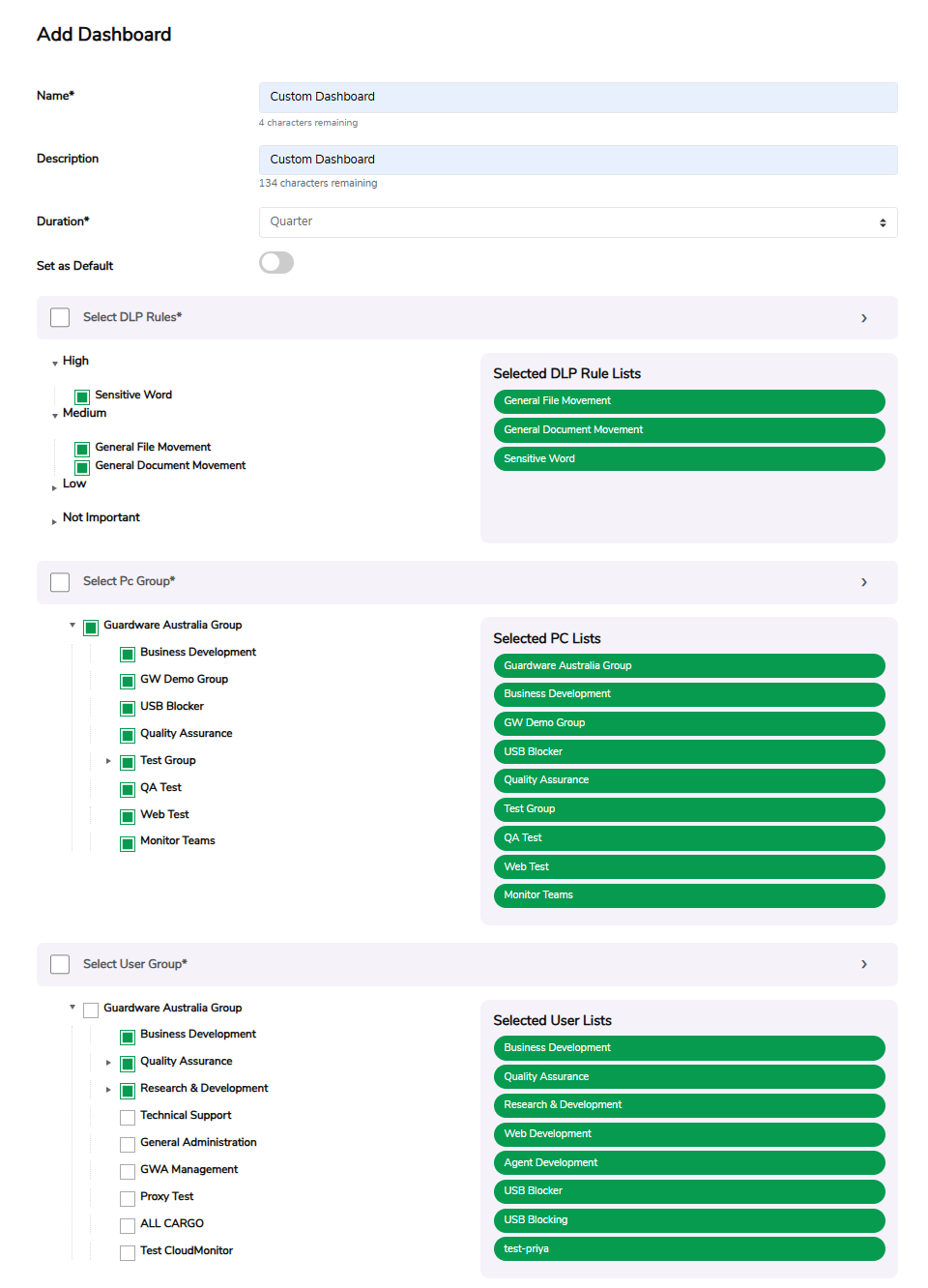
Select DLP Rules. Data Loss Prevention (DLP) Rules are security policies that detect and prevent the unauthorised sharing or transfer of sensitive information. You can select one or more DLP rules to filter dashboard data based on specific monitoring criteria. The selected DLP rules appear in the panel on the right.
Select PC Groups. PC Groups represent collections of endpoint devices within your organisation (for example, HR Laptops or Finance Desktops). Selecting a PC Group filters the dashboard’s data to activities performed on those specific devices. The selected PC groups appear in the panel on the right.
Select User Groups. User Groups are sets of users with similar roles, permissions, or departments (for example, IT Team or Sales Department). Selecting user groups allows you to monitor data generated only by those users. The selected User groups appear in the panel on the right.
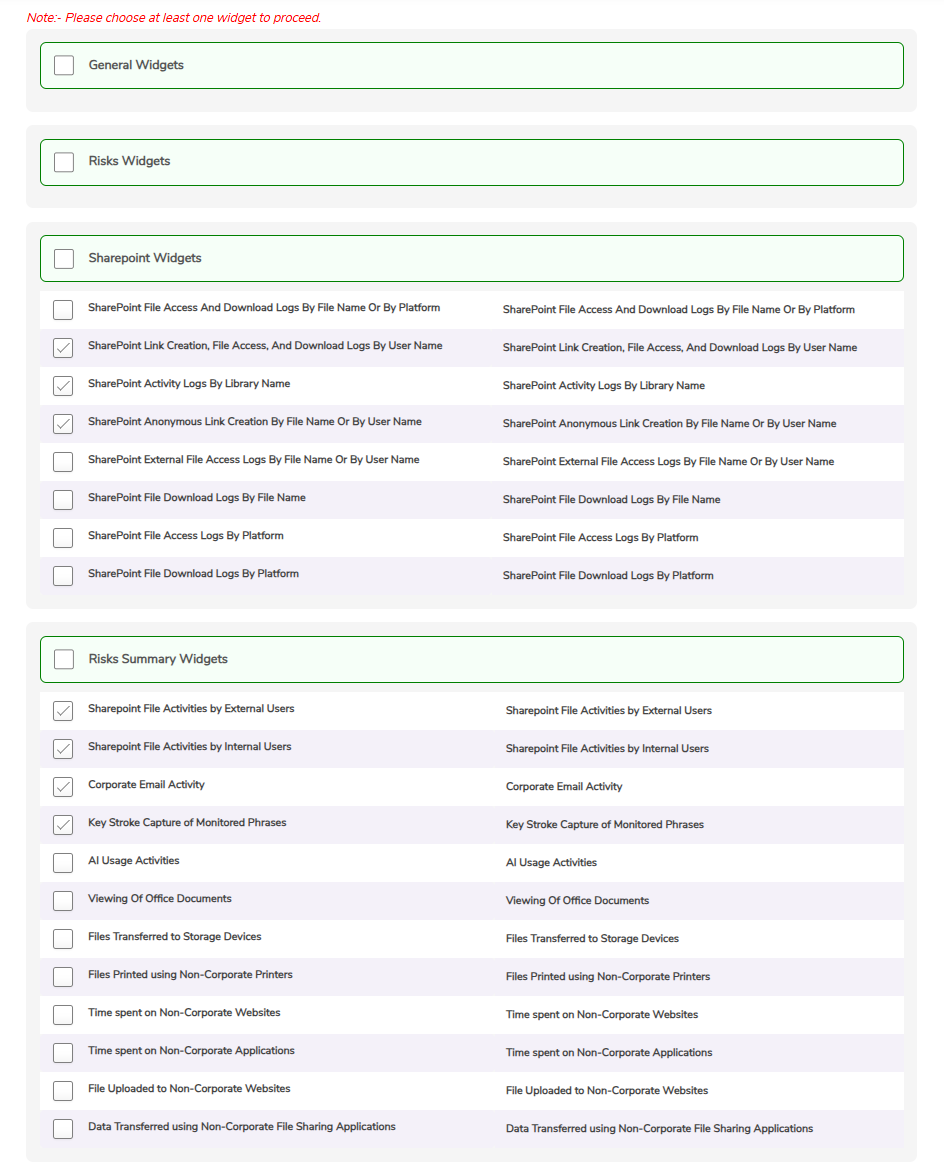
Select the widgets you want to include in the dashboard. Widgets can be selected from different dashboards, such as General, Risks, SharePoint, and Risks Summary dashboards. You must select at least one widget to continue.
Click Save Changes to create the dashboard.
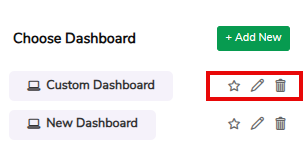
Manage Custom Dashboards
After creating a dashboard, you can manage it from Settings > Dashboard.
From this page, you can:
View the list of all custom dashboards you’ve created.
Edit an existing dashboard to update its widgets, filters, or duration.
Delete dashboards that are no longer needed.
Set any dashboard as the default to make it your primary dashboard view.
Access Custom Dashboards
To access your dashboards:
Go to Dashboard from the main navigation menu.
Select your custom dashboard from the dropdown list at the top of the page.
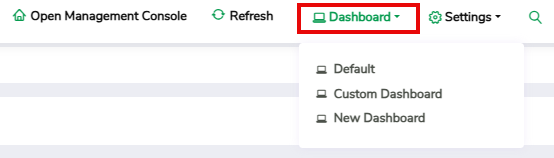
The dashboard will load with the widgets and filters you’ve configured. You can switch between dashboards at any time and adjust the time filters.
Advanced Search
The Advanced Search feature allows you to locate specific activity logs, files, or events more efficiently by applying multiple filters. It helps narrow down large data sets to show only the information you need, such as specific users, PCs, DLP rules, or SharePoint files, saving time and improving data visibility.
You can use Advanced Search to find detailed activity records within a specific date and time range, filter events based on Data Loss Prevention (DLP) rules or PC Groups, search for SharePoint-related activities by site URL, file name, or file path, and so on.
You don’t need to fill every field. Entering even one or two filters will refine your search results.
To perform an advanced search:
Click the Search icon()located at the top-right corner of the relevant dashboard.
Fill in one or more of the available fields:
Date From / Date To: Specify the date range for the data you want to view.
Time From / Time To: Specify a specific time to narrow the search further.
Select User Groups: Filter results by user groups to view activities performed by specific teams or departments.
Select PC Groups: Filter results by PC groups to view activities performed by selected endpoint groups, such as HR Laptops or Finance Desktops.
Select DLP Rules: Filter results based on defined Data Loss Prevention policies (for example, Email Attachments, File Uploads, or Printing of Files).
Username: Search for activities by a specific user.
PC Name: View results related to a specific device or workstation.
Filename: Search for a particular file by its name.
SharePoint Site URL: Locate activities associated with a specific SharePoint site.
SharePoint File Path: Search for files by their full SharePoint directory path.
Once you’ve entered the filters, click Search. If you want to reset all fields and start a new search, click Clear Search.
For instance, to find all file-sharing activities from the Finance Department PCs between 1st and 11th October, select the relevant PC Group, select 2025-10-01 in Date From and 2025-10-11 in Date To, and click Search. The results will display only activities that match those filters.
Last updated

